14MRXnsQhQ7LQSfKPMsESdJsEPFDyMCmMg
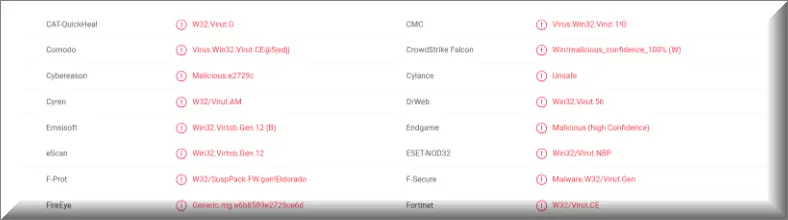
A majority of antivirus programs have detected the virus using 14MRXnsQhQ7LQSfKPMsESdJsEPFDyMCmMg Bitcoin Wallet. You can see the attached report from VirusTotal below:
Many users reached to us for help about a malicious email with the following text:
Subject: I RECORDED YOU
Hello there!
Unfortunately, there are some bad news for you.
Some time ago your device was infected with my private trojan, R.A.T (Remote Administration Tool), if you want to find out more about it simply use Google.
My trojan allows me to access your accounts, your camera and microphone.
Check the sender of this email, I have sent it from your email account.
You truly enjoy checking out porn websites and watching dirty videos, while having a lot of kinky fun.
I RECORDED YOU (through your camera) SATISFYING YOURSELF!
If you still doubt my serious intentions, it only takes couple mouse clicks to share the video of you with your friends, relatives, all email contacts and on social networks.
All you need is $1400 USD in Bitcoin (BTC) transfer to my account (Bitcoin equivalent based on exchange rate during your transfer).
After the transaction is successful, I will proceed to delete everything without delay.
Afterwards, we can pretend that we have never met before.
In addition, I assure you that all the harmful software will be deleted from your device.
Be sure, I keep my promises!
If you are unaware how to buy and send Bitcoin (BTC) – Google: Where to buy Bitcoin (BTC), to send and receive Bitcoin (BTC), you can register your wallet for example here: www.blockchain.com
My Bitcoin (BTC) address is: 14MRXnsQhQ7LQSfKPMsESdJsEPFDyMCmMg
Yes, that’s how the address looks like, copy and paste my address, it’s (cAsE-sEnSEtiVE).
You are given not more than 48 hours after you have opened this email (2 days to be precise).
Everything will be carried out based on fairness!
An advice from me – regularly change all your passwords to your accounts and update your device with newest security patches.
There are all sorts of malicious and dangerous software programs throughout the Internet and if you are not careful every time you go online, you risk landing some nasty cyber threat on your PC that could cause some really serious problems. A recently detected example of a very dangerous PC virus is an insidious piece of software called 14MRXnsQhQ7LQSfKPMsESdJsEPFDyMCmMg. This is a representative of the Trojan Horse category of viruses, like Porn Blackmail and Recorded You Email , Hello My Perverted Friend Email. As you likely already know, trojan horses are among the nastiest of online threats you could possibly come across while browsing the World Wide Web and 14MRXnsQhQ7LQSfKPMsESdJsEPFDyMCmMgis one of the newest members of this malware family. As such, this noxious program is highly dangerous and stealthy and big number of users have already faced the potential consequences from having such a virus on their computers. We assume that a lot of the people who are currently reading this write-up have also had their PCs infiltrated by this dangerous and highly problematic Trojan Horse version. If that is your case as well, we might have some good news for you. At the bottom of the article you’re currently reading, you will find that there’s a removal guide with steps that show how one can potentially locate the insidious piece of malware inside their PC and manually eliminate it. However, since the manual approach towards solving this issue might not be for everyone and might not always be fully effective, we have also made sure to add a suggested removal program for malware within the guide. You can use that tool as an alternative to the manual instructions or you could combine the two methods for maximum results (this is actually what we’d advise you to do). Now, before we show you the guide, we need to tell you some more information about 14MRXnsQhQ7LQSfKPMsESdJsEPFDyMCmMg and the category it belongs to so that you are better acquainted with the typical traits and characteristic features of this malware class.
Trojan Horse stealth
A major factor that plays a big role in the ability of Trojans to infect most computers and execute their criminal tasks on them is the fact that the majority of cyber threats that belong to this virus category are deprive of any specific infection symptoms. This means that a Trojan like 14MRXnsQhQ7LQSfKPMsESdJsEPFDyMCmMg Bitcoin Wallet could potentially attack your computer and infiltrate its system without you noticing anything out of the ordinary. Due to this, many users do not realize that their machines have gotten compromised by some dangerous virus or at least not until the task of the malicious program has already been carried out and the damage has already been caused. This, however, doesn’t mean you aren’t supposed to be looking out for potential symptoms and red flags. With any luck, if you are vigilant enough, you might potentially spot the infection and take counteraction before the malware has fulfilled its purpose. Some of the infection indications that might sometimes give away the virus are increased use of CPU, GPU and RAM, random errors or odd blinking windows on your screen, sudden crashes and freezes as well as other similar system behavior irregularities that seem to be occurring for no visible reason.
One other important aspect of the stealthiness of most Trojans is how they manage to infect the targeted computer in the first place. Most such viruses use sources that are supposed to look harmless on first view. Such sources could be random spam e-mails, misleading offers and adverts that might be showing in your browser when you are visiting some sketchy site or if you have some adware program on your PC, pirated downloadable content, illegal streaming sites or sites with adult content and so on. The possibilities are endless and we cannot list all the possible ways a Trojan Horse virus could get to you. However, what we can say is that you need to always be on your guard when browsing the online world in order to manage to stay away from anything that could be a potential threat.
Trojan Horse-related damage
Many Trojans are used for system and data corruption and for information theft. However, those are only some of the many capabilities of those viruses. Other problems that most typical Trojans could cause are draining your online banking accounts, spying on your activities on your computer and on you personally (through your webcam) and even taking control over your machine and using it for criminal tasks like DDoS or spam e-mail campaigns as a part of the hacker’s botnet. The aforementioned possibilities are only the most frequently encountered ones but there are many other insidious tasks that Trojans like 14MRXnsQhQ7LQSfKPMsESdJsEPFDyMCmMg could be employed for. Due to this, we cannot be sure what this virus would try to do in your particular case but what we can tell you is that you should really consider cleaning your PC before any serious harm has been done to your machine and/or to your virtual privacy.
SUMMARY:
| Name | 14MRXnsQhQ7LQSfKPMsESdJsEPFDyMCmMg |
| Type | Trojan |
| Detection Tool |
Remove 14MRXnsQhQ7LQSfKPMsESdJsEPFDyMCmMg Malware
To try and remove 14MRXnsQhQ7LQSfKPMsESdJsEPFDyMCmMg quickly you can try this:
- Go to your browser’s settings and select More Tools (or Add-ons, depending on your browser).
- Then click on the Extensions tab.
- Look for the 14MRXnsQhQ7LQSfKPMsESdJsEPFDyMCmMg extension (as well as any other unfamiliar ones).
- Remove 14MRXnsQhQ7LQSfKPMsESdJsEPFDyMCmMg by clicking on the Trash Bin icon next to its name.
- Confirm and get rid of 14MRXnsQhQ7LQSfKPMsESdJsEPFDyMCmMg and any other suspicious items.
If this does not work as described please follow our more detailed 14MRXnsQhQ7LQSfKPMsESdJsEPFDyMCmMg removal guide below.
If you have a Windows virus, continue with the guide below.
If you have a Mac virus, please use our How to remove Ads on Mac guide.
If you have an Android virus, please use our Android Malware Removal guide.
If you have an iPhone virus, please use our iPhone Virus Removal guide.
Some of the steps may require you to exit the page. Bookmark it for later reference.
Next, Reboot in Safe Mode (use this guide if you don’t know how to do it).
 Uninstall the 14MRXnsQhQ7LQSfKPMsESdJsEPFDyMCmMg app and kill its processes
Uninstall the 14MRXnsQhQ7LQSfKPMsESdJsEPFDyMCmMg app and kill its processes
The first thing you must try to do is look for any sketchy installs on your computer and uninstall anything you think may come from 14MRXnsQhQ7LQSfKPMsESdJsEPFDyMCmMg. After that, you’ll also need to get rid of any processes that may be related to the unwanted app by searching for them in the Task Manager.
Note that sometimes an app, especially a rogue one, may ask you to install something else or keep some of its data (such as settings files) on your PC – never agree to that when trying to delete a potentially rogue software. You need to make sure that everything is removed from your PC to get rid of the malware. Also, if you aren’t allowed to go through with the uninstallation, proceed with the guide, and try again after you’ve completed everything else.
- Uninstalling the rogue app
- Killing any rogue processes
Type Apps & Features in the Start Menu, open the first result, sort the list of apps by date, and look for suspicious recently installed entries.
Click on anything you think could be linked to 14MRXnsQhQ7LQSfKPMsESdJsEPFDyMCmMg, then select uninstall, and follow the prompts to delete the app.

Press Ctrl + Shift + Esc, click More Details (if it’s not already clicked), and look for suspicious entries that may be linked to 14MRXnsQhQ7LQSfKPMsESdJsEPFDyMCmMg.
If you come across a questionable process, right-click it, click Open File Location, scan the files with the free online malware scanner shown below, and then delete anything that gets flagged as a threat.


After that, if the rogue process is still visible in the Task Manager, right-click it again and select End Process.
 Undo 14MRXnsQhQ7LQSfKPMsESdJsEPFDyMCmMg changes made to different system settings
Undo 14MRXnsQhQ7LQSfKPMsESdJsEPFDyMCmMg changes made to different system settings
It’s possible that 14MRXnsQhQ7LQSfKPMsESdJsEPFDyMCmMg has affected various parts of your system, making changes to their settings. This can enable the malware to stay on the computer or automatically reinstall itself after you’ve seemingly deleted it. Therefore, you need to check the following elements by going to the Start Menu, searching for specific system elements that may have been affected, and pressing Enter to open them and see if anything has been changed there without your approval. Then you must undo any unwanted changes made to these settings in the way shown below:
- DNS
- Hosts
- Startup
- Task
Scheduler - Services
- Registry
Type in Start Menu: View network connections
Right-click on your primary network, go to Properties, and do this:

Type in Start Menu: C:\Windows\System32\drivers\etc\hosts

Type in the Start Menu: Startup apps

Type in the Start Menu: Task Scheduler

Type in the Start Menu: Services

Type in the Start Menu: Registry Editor
Press Ctrl + F to open the search window


Leave a Comment