1PPJpvSPbbMwbESJZXGS8VtKiFQkmm7DvK
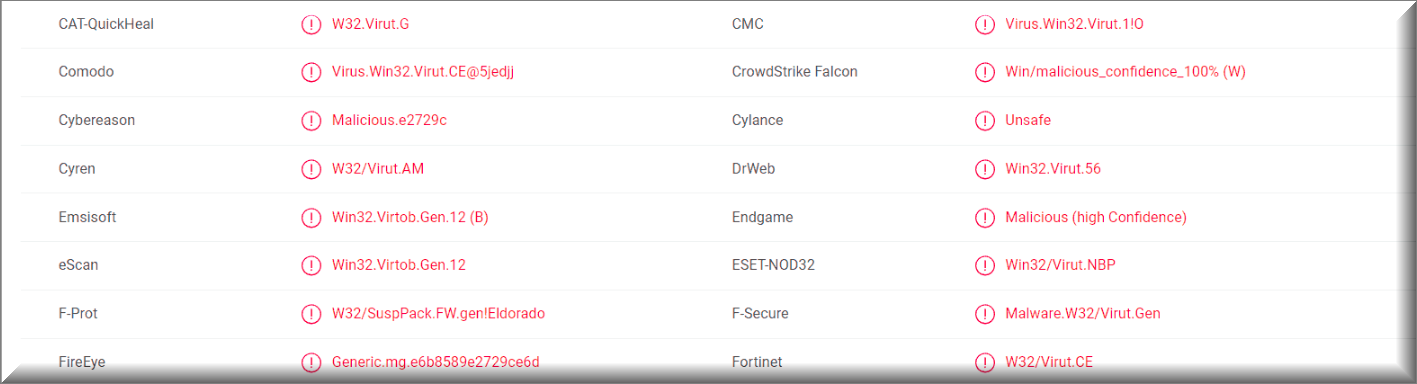
A majority of antivirus programs have detected the virus using 1PPJpvSPbbMwbESJZXGS8VtKiFQkmm7DvK Bitcoin Wallet. You can see the attached report from VirusTotal below:
Some of our readers reported an email that they have received, with the following message:
Subject: Security status not satisfied.
I was planning to say hello, but now I think greetings are unnecessary.
Firstly, I already know you and all your loved ones very well.
Secondly, the occasion for which I’m writing to you is not the happiest one for a friendly greeting.
You’ve heard that the Internet is a dangerous place, infested with malicious links and hackers like me?
Of course, you’ve heard, but what’s the point in it if you are so dismissive of your internet security and don’t care what websites you visit?
Times have changed. You read about AI, judging by your browser history, and still didn’t understand anything?
Technologies have stepped far forward, and now hackers like me use artificial intelligence.
Thanks to it, I can get not only access to your webcam and record your fun with highly controversial video
(I recorded it also, but now that’s not the point), but also to all your devices and not only yours.
And I saved a special sauce for this dish. I went further and sent malicious links to all your contacts from your account.Yes, someone was smarter and realized that this was a trap and you were hacked, but believe me,
about 70% of your contact list (and these are your friends, colleagues, and family) bought into my scam.
They have as many skeletons in their closet as you do. Some turn out to be hidden homosexuals…
I have accumulated and analyzed a huge amount of compromising data on you and those with whom you communicate.
Very soon I’ll start a crossfire – everyone will receive the full history of correspondence
(and there are enough of “sensitive moments”) and recordings from the other contact’s webcam.
I can go further and put all these files, as well as the recorded fun of you and your hacked contacts with “hardcore videos” into the public domain.
You can imagine, it will be a real sensation!
And everyone will understand where it came from – from you.
For all your contacts and, you will be enemy number one. Even your relatives will take a long time to forgive you and forget such a family shame…It will be the real end of the world. The only difference is that there will be not four horsemen of the apocalypse, but only one – (=
But there is no such thing as a completely black stripe without any white dots.
Luckily for you, in my case the “Three M Rule” comes into play – Money, Money and Money again.
I’m not interested in your worthless life, I’m interested in people from whom I can profit.
And today you are one of them.
That’s why: Transfer $1390 in Bitcoin to: 1PPJpvSPbbMwbESJZXGS8VtKiFQkmm7DvK …within 48 hours!
You don’t know how to use cryptocurrencies? Use Google, everything is simple.
Once payment is received, I will delete all information associated with you and you will never hear from me again.
Remember one thing: my crypto address is anonymous, and I generated this letter in your mailbox and sent it to you.
You can call the cops, do whatever you want – they won’t find me, my demands won’t change, but you’ll just waste precious time.
The clock is ticking. Tick tock, a minute out of 48 hours has passed right now. An hour will soon pass, and in two days your old life will pass forever.
Either goodbye forever (if I get my payment), or hello to a brave new world in which there will be no place for you.
Hasta La Vista, Baby!
P.S. Almost forgot. Finally learn what incognito tabs, two-factor authentication, and the TOR browser are, for God’s sake!
There are many different kinds of Trojan Horse viruses – some target your system data, some try to spy on you, some seek to steal sensitive info from your computer and online accounts and some might even be used to silently download other harmful programs the likes of Ransomware and Rootkits on the infected computer. Here, however, we will be focusing on a specific type of e-mail Trojans that are used in phishing e-mail campaigns, which have recently become quite widespread and currently there are a lot of users who have fallen victims to these threats. One example of such a phishing e-mail Trojan Horse virus is 1PPJpvSPbbMwbESJZXGS8VtKiFQkmm7DvK , which will be the main topic of this article. If you have recently noticed some obscure e-mails in your inbox that claim you need to pay a certain amount of BitCoins or something bad would happen, then you likely have 1PPJpvSPbbMwbESJZXGS8VtKiFQkmm7DvK, “Drive by exploit” or “Save Yourself” inside your computer. In order to increase the chances of the scam being successful and make their e-mails be more threatening, the criminals behind this scheme usually claim that your PC has been hacked and that if you do not pay, something bad will happen to the machine. In their e-mails, the scammers might claim that some sensitive information about the user has been acquired by them and that it would be made publicly available online in order to scare the user into paying. This is somewhat similar to the way Ransomware cryptoviruses try to intimidate users into sending money to the hackers by claiming that the user’s files would stay locked if the money isn’t paid. However, the difference here is that the scammers are only bluffing and they don’t actually have any actual leverage over you.
Some more words about 1PPJpvSPbbMwbESJZXGS8VtKiFQkmm7DvK
The problem with having this Trojan which might potentially be inside your computer isn’t solely related to the phishing e-mails you are likely to receive if the infection has reached you. A more experienced and discerning user would easily spot the scam and ignore and delete the phishing letter. However, since the Trojan is still in the PC and because this type of malware is actually highly versatile, the malicious program might still be used to carry out some other insidious and harmful task inside the targeted machine. We already mentioned some of the common uses of a typical Trojan Horse virus at the start of this article. Note that some Trojans could get remotely repurposed to do something different from their initial task after they have already attacked a certain computer. This means that even if you do not fall for the e-mail scam, your PC and your virtual security and privacy are still not going to be safe if the malware doesn’t get removed. The sooner you ensure that all malicious data has been removed from your computer, the less time the malware would have to do some other nasty thing to your computer. Therefore, we advise you to act quickly and use the guide from this page and/or the removal tool attached to it and get rid of 1PPJpvSPbbMwbESJZXGS8VtKiFQkmm7DvK ASAP!
SUMMARY:
| Name | 1PPJpvSPbbMwbESJZXGS8VtKiFQkmm7DvK |
| Type | Trojan |
| Detection Tool |
Remove 1PPJpvSPbbMwbESJZXGS8VtKiFQkmm7DvK Bitcoin Email Virus
You are dealing with a malware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to clean up and reset your browser to its original settings without the malware returning. You can find the removal guide here.
For mobile devices refer to these guides instead: Android, iPhone

Leave a Comment