Taskhostw.exe
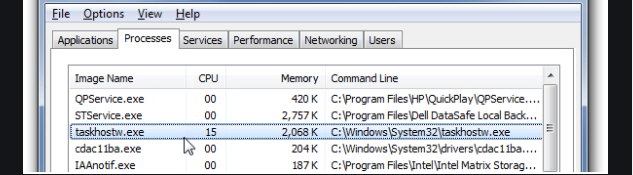
Taskhostw.exe is an integral component of the Windows operating system, serving as the host for tasks within Windows. Its primary role is to initiate Windows services that rely on DLLs (Dynamic Link Libraries) during the system’s startup phase. DLLs are files filled with code and resources that various applications can utilize concurrently. Taskhostw.exe provides a platform for processes running as part of a DLL rather than as standalone executable (EXE) files. The authentic version of taskhostw.exe is found in the C:\Windows\System32 directory. If discovered in a different location, it might indicate the presence of malware posing as taskhostw.exe. To verify the file’s location, you can navigate to it via the Task Manager by right-clicking the file and selecting “Open file location”.
Taskhostw.exe, in its genuine form, is not malicious software. However, it can be exploited by malware to conceal nefarious activities. Malicious programs might forge a counterfeit taskhostw.exe file and locate it outside its standard directory. Additionally, they could embed harmful code into the authentic taskhostw.exe process, leveraging it to execute malevolent deeds.
Any computer, that has been attacked by a malware from the Trojan horse family, could have really serious damage to its system as well as its data. Your PC is not an exception if it has been compromised by a Trojan like Taskhostw.exe Virus, Pinaview, StopAbit or Taskbarify. Once inside the PC, this virus can cause issues, which you would better never experience. Usually, it is very difficult to detect the infection without proper security software because it uses various camouflaging techniques to trick you and remain as long as possible on the computer. That’s why the researchers from our “How to remove” team would advise you to be very careful when trying to deal with Taskhostw.exe Virus. Below, you will find more information about the possible damage that this Trojan may cause and a helpful removal tool along with a manual Removal Guide for proper detection and elimination of all the related malicious scripts.
Whаt is Taskhostw.exe?
Ttaskhostw.exe file is a secure system process of Microsoft Windows 10 operating system Often, malware writers, such as viruses, worms, and trojans, intentionally give their processes Taskhostw.exe a filename to avoid detection.
Taskhostw.exe is a new Trojan horse threat, which has many malicious abilities. A number of online users have already been infected with this malware and have reported different issues. According to the latest security analysis, Taskhostw.exe is a sophisticated virus, which can silently infect any computer, without particular symptoms. The moment it gets inside the system, it can initiate various harmful processes, most of which are unlikely to be detected without a proper antivirus software. The Trojan usually hides its traces and camouflages its malicious activities under guise of regular system processes till the moment when some major damage is caused to the infected computer. Only then the victim is actually likely to find out about the presence of the infection. This method of operation based on stealth and disguise is what makes Taskhostw.exe Virus such a dreadful infection which can cause damage when and where you least expect it.
To prevent such dreadful malicious consequences, our “How to remove” team would highly recommend you remove Taskhostw.exe Virus immediately. The quickest way to do that is to scan your PC with the professional Taskhostw.exe Virus removal tool form this article’s page. You can also use the instructions in the Removal Guide below or contact a professional of your choice for additional assistance.
How can you get infected with Taskhostw.exe Virus?
Usually, in order to enter your system, Taskhostw.exe Virus needs to mislead you about its real nature and purpose. Normally, the infection pretends to be an attractive offer, a seemingly harmless link, file or a file which could be delivered as an email, attachment, social share link or a pop-up message on your screen. The aim of this is to trigger your curiosity and make you click on the malicious transmitter without taking a moment to think about whether or not it’s safe. At that very moment, the Trojan activates and exploits your system through a vulnerability or an exploit kit. If your antivirus program is updated, it may detect the threat and inform you on time. However, if you have not updated your virus definitions, it may not provide you with protection against a new Trojan such as Taskhostw.exe Virus.
What issues may Taskhostw.exe Virus cause once in your system?
Trojans are a multipurpose type of malware. They can be programmed to perform specific criminal tasks and serve the purpose of their criminal creators. What exactly the hackers may decide to use a threat like Taskhostw.exe for is very difficult to predict. Still, here we have listed some of the most common and possible malicious activities, which the Trojans could generally be programmed to perform. Take a look at them and know that Taskhostw.exe may be related to them or even some other forms of fraud or theft.
- System crashing, corruption and destruction of data: Partial or total corruption of the infected computer could be one of the goals of the hackers. They may also want to delete certain files from your system or to wipe off the entire data from the computer’s hard drives and with a Trojan like Taskhostw.exe, this could happen very easily.
- Unauthorized access to the computer and exploitation of its resources: With the help of a Trojan like Taskhostw.exe, your PC may be turned into a bot, which the hackers can control remotely and manipulate as they please. They may exploit it for a number of other criminal purposes without your knowledge and indirectly relate you to them.
- Spreading viruses and Ransomware: A Trojan horse can infect any system by using stealth and disguise. With the same ease, it can also provide a backdoor for other infections such as Ransomware, Spyware, other Trojans or some other form of insidious malware programs.
- Theft of banking credentials, passwords, and data: Any information that you keep on your PC could easily be transmitted to the hackers’ remote servers when a Trojan horse is secretly working on your system. This means that everything you type and you do on the machine might be getting monitored and used for further fraud, theft, blackmailing or some other form of abuse.
Should you believe that Taskhostw.exe is compromised by malware, you may adhere to the following complimentary guide for malware eradication to purify your device.
SUMMARY:
| Name | Taskhostw.exe |
| Type | Trojan |
| Detection Tool |
Remove Taskhostw.exe
To try and remove Taskhostw.exe quickly you can try this:
- Go to your browser’s settings and select More Tools (or Add-ons, depending on your browser).
- Then click on the Extensions tab.
- Look for the Taskhostw.exe extension (as well as any other unfamiliar ones).
- Remove Taskhostw.exe by clicking on the Trash Bin icon next to its name.
- Confirm and get rid of Taskhostw.exe and any other suspicious items.
If this does not work as described please follow our more detailed Taskhostw.exe removal guide below.
If you have a Windows virus, continue with the guide below.
If you have a Mac virus, please use our How to remove Ads on Mac guide.
If you have an Android virus, please use our Android Malware Removal guide.
If you have an iPhone virus, please use our iPhone Virus Removal guide.
Some of the steps may require you to exit the page. Bookmark it for later reference.
Next, Reboot in Safe Mode (use this guide if you don’t know how to do it).
 Uninstall the Taskhostw.exe app and kill its processes
Uninstall the Taskhostw.exe app and kill its processes
The first thing you must try to do is look for any sketchy installs on your computer and uninstall anything you think may come from Taskhostw.exe. After that, you’ll also need to get rid of any processes that may be related to the unwanted app by searching for them in the Task Manager.
Note that sometimes an app, especially a rogue one, may ask you to install something else or keep some of its data (such as settings files) on your PC – never agree to that when trying to delete a potentially rogue software. You need to make sure that everything is removed from your PC to get rid of the malware. Also, if you aren’t allowed to go through with the uninstallation, proceed with the guide, and try again after you’ve completed everything else.
- Uninstalling the rogue app
- Killing any rogue processes
Type Apps & Features in the Start Menu, open the first result, sort the list of apps by date, and look for suspicious recently installed entries.
Click on anything you think could be linked to Taskhostw.exe, then select uninstall, and follow the prompts to delete the app.

Press Ctrl + Shift + Esc, click More Details (if it’s not already clicked), and look for suspicious entries that may be linked to Taskhostw.exe.
If you come across a questionable process, right-click it, click Open File Location, scan the files with the free online malware scanner shown below, and then delete anything that gets flagged as a threat.


After that, if the rogue process is still visible in the Task Manager, right-click it again and select End Process.
 Undo Taskhostw.exe changes made to different system settings
Undo Taskhostw.exe changes made to different system settings
It’s possible that Taskhostw.exe has affected various parts of your system, making changes to their settings. This can enable the malware to stay on the computer or automatically reinstall itself after you’ve seemingly deleted it. Therefore, you need to check the following elements by going to the Start Menu, searching for them, and pressing Enter to open them and to see if anything has been changed there without your approval. Then you must undo any unwanted changes made to these settings in the way shown below:
- DNS
- Hosts
- Startup
- Task
Scheduler - Services
- Registry
Type in Start Menu: View network connections
Right-click on your primary network, go to Properties, and do this:

Type in Start Menu: C:\Windows\System32\drivers\etc\hosts

Type in the Start Menu: Startup apps

Type in the Start Menu: Task Scheduler

Type in the Start Menu: Services

Type in the Start Menu: Registry Editor
Press Ctrl + F to open the search window


Leave a Comment