*Tcbu is a variant of Stop/DJVU. Source of claim SH can remove it.
Tcbu
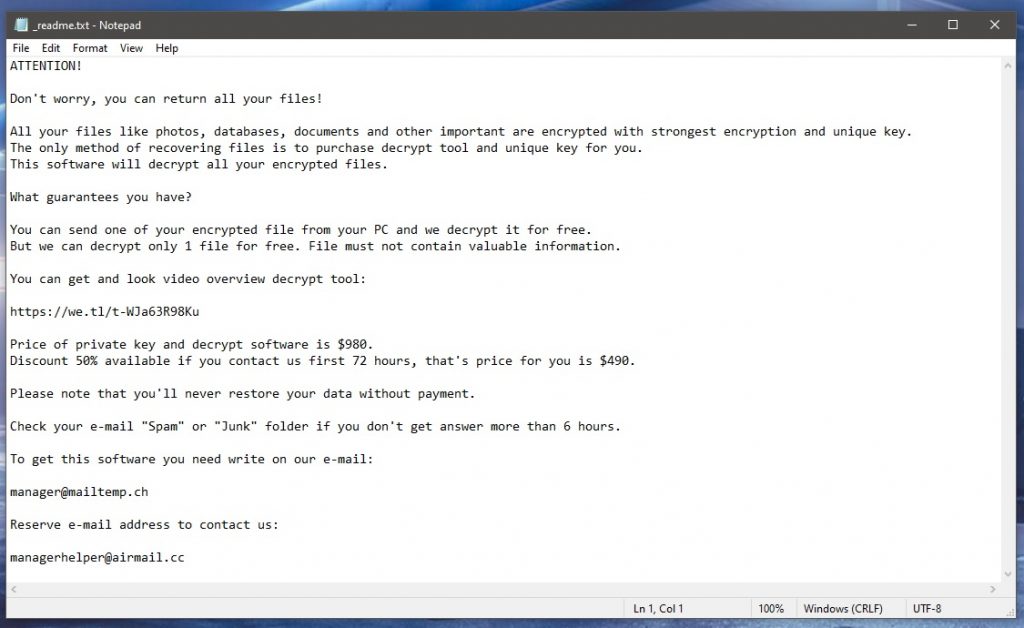
Tcbu is a ransomware virus that asks its victims for a ransom payment in exchange for providing them with access to their encrypted information. Tcbu uses a complex cryptographic code to render the victim’s most used files inaccessible and then blackmails them to pay for a decryption key.
You are most probably interested in reading our article because Tcbu has secretly encrypted your most valuable files and has asked you to transfer some money to the cryptocurrency account of some anonymous criminals. The option offered by the hackers, however, is not the only answer to your problem. There are some alternative methods that could potentially help you avoid the ransom payment and still recover some of your data. In the next lines, we will tell you more about them and will provide you with instructions on how to remove the dreadful Tcbu ransomware from your system.
The Tcbu virus
The Tcbu virus is a ransomware-based program that can scan a computer and encrypt the most commonly used data stored on it. After that, the Tcbu virus will typically ask for a payment in bitcoins in order to provide its victims with a file-decryption key.
Ransomware applications such as Tcbu, Fatp, Fate are typically designed for nothing more than simple blackmail. They can infiltrate a computer in secret and encrypt a specific list of files on your computer without being detected. Upon finishing this task, they appear to do something even more disturbing. They display a message on the infected device that states that you are supposed to pay ransom if you want your data to be accessible again. The requested amount may vary a lot from case to case, but in some situations, the crooks behind the ransomware may demand the equivalent of a couple of thousand of dollars in bitcoins.
The ways of delivery of Tcbu may range from a software package distribution to spam emails and their attachments. However, we should mention that Ransomware rarely arrives by itself. Instead, it normally sneaks in the system with the help of a Trojan horse that exploits the flaws in your OS or the additional programs installed on your computer. Therefore, when you remove the Ransomware, you should also make sure you check your system for a hidden Trojan horse and remove it as well.
The .Tcbu file encryption
The .Tcbu file encryption is a method that is used to encode files and make them inaccessible for the purpose of money extortion. The .Tcbu file encryption can run in the background of the system and remain under the radar of most security programs.

The two most pressing questions that we frequently get asked about are whether it is a good idea to pay the demanded ransom and whether the encrypted information can be recovered. Unfortunately, there is no answer that can be universal for all the cases of ransomware infection. However, it is NEVER a smart idea to send money to anonymous criminals no matter what they promise. The reason is you simply can’t be sure that, once they get the money, they will help you recover your files. Therefore, our recommendation is to try some other methods of dealing with Tcbu before you risk your money. In the case that you decide to remove Tcbu and try to extract data from system backups, our removal guide is here to assist you.
SUMMARY:
| Name | Tcbu |
| Type | Ransomware |
| Detection Tool |
*Tcbu is a variant of Stop/DJVU. Source of claim SH can remove it.
Remove Tcbu Ransomware

In the first step of this guide, we recommend that you bookmark this page in your browser’s favorites, so you can save it and have access to it until you finish the Tcbu removal process.
Next, you should restart the computer infected with the Tcbu ransomware in Safe Mode (follow this link for instructions) so that only the most basic programs and processes are running on your system. In this way, you’ll hopefully be able to identify and terminate the Tcbu-related processes easier.
After you reboot in Safe Mode, click the Start menu, enter “msconfig” in the search area and press Enter. Once you do this, System Configuration will open on the screen. Check the list of startup items to see whether any of them are connected to the malware by clicking on the Startup tab.

Those entries that have “Unknown” Manufacturers, strange names, and entries that you can’t connect to any reputable applications on your PC should be researched online. If the information you discover about them indicates that they pose a risk, the best course of action is to uncheck their relevant checkbox.
After you are done with that, click again on the Start menu button bottom left, carefully type each of the locations written below in the Search bar one by one and press Enter to open them:
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
Search for files and folders with strange names that have been added around the time of the ransomware infection in each location. If you think anything should be eliminated, do it with caution.
When you enter Temp, select everything from that folder and then delete it. This will clear up any ransomware-created temporary files from the system.

WARNING! READ CAREFULLY BEFORE PROCEEDING!
*Tcbu is a variant of Stop/DJVU. Source of claim SH can remove it.
Check the system for active malicious processes in the next step. Click the Processes Tab in the Task Manager window that appears by pressing CTRL + SHIFT + ESC from the keyboard.
Use the CPU and Memory Usage columns to see if any suspicious processes are running in the background of your system. Then attempt to isolate them by looking at their names, how they’re titled, or how much resources they consume while running.
Right-click on any process that appears to be harmful and select Open File Location from the pop-up menu.

After that, you may use the free online virus scanner below to scan the files in the File Location folder for malware.

End the process whose files have been identified as harmful by the scanner, and then remove those malicious files and their directories from the computer.
![]()
Using the Windows Key and R key on the keyboard, start a Run command window. Then copy the following line in it:
notepad %windir%/system32/Drivers/etc/hosts
Click OK after copying the line, find Localhost in the text of the Hosts file that appears on the screen and look for evidence of hacking. If your computer has been hacked, you’ll see a bunch of IP addresses at the bottom of your file under Localhost that look strange, just as seen in the sample image below.

If you find something questionable in your Hosts file, please let us have a look at it by leaving us a comment below this article, and we will give you advice on what to do if we find something suspicious.
If your Hosts file seems to be clean, you may close it and go on to the next step without more ado.
![]()
*Tcbu is a variant of Stop/DJVU. Source of claim SH can remove it.
Malicious entries in the registry that have been added without the victim’s awareness are often the reason why ransomware threats like Tcbu tend to re-appear on the system and are difficult to remove. Therefore, if you want to deal with the infection effectively, the registry of your computer must be carefully checked for such files.
For this, launch the Registry Editor (type Regedit into the Windows search bar and click Enter on the keyboard) and use CTRL and F to search for entries related to the infection. Simply type the ransomware’s name into the Find box that pops up and click Find Next.
Avoid deleting files and directories that aren’t linked to Tcbu while deleting the ones that show in the results, since doing so might harm your operating system. It is preferable to use a professional removal program, such as the one suggested on this page, to prevent any unintended system harm. Detecting and removing malware from sensitive system locations such as the registry is what this program is best at.
![]()
How to Decrypt Tcbu files
Depending on the type of the virus, decrypting encrypted data may need an entirely different approach. The extensions of encrypted files might reveal the precise variant of ransomware that has attacked you.
First, however, please use the help of professional anti-virus software, such as those mentioned on this website, to get rid of Tcbu and other infections. Once the ransomware is removed from your computer, you may begin the process of decrypting any data that may have been encrypted.
New Djvu Ransomware
STOP Djvu, the most recent variant of the Djvu ransomware infection, encrypts data by attaching the .Tcbu suffix to the encoded files. At the time this article is written, only files encrypted with an offline key may presently be deciphered. Check out this link for a decryption program that may be useful in recovering your data:
https://www.emsisoft.com/ransomware-decryption-tools/stop-djvu
Decryption
To get the STOPDjvu.exe decryptor, all you need to do is follow the link provided above and choose “Download”.
After the file has been downloaded on the computer, select “Run as Administrator” and then press the Yes button to start the application. Click the Decrypt button to begin decrypting your data once you’ve read the licensing agreement and the brief instructions. Please note that files that have been encrypted with unknown offline keys or online encryption may not be deciphered using this tool.
For more help, please use the anti-virus software listed on this page or the free online virus scanner to guarantee that Tcbu has been completely removed from the system. Also, if you have any questions, please feel free leave them in the comments’ section below.

Leave a Comment