This page aims to help you remove TorPedoHunt3r. Our removal instructions work for every version of Windows.
TorPedoHunt3r
TorPedoHunt3r is a sextortion attempt received by email. The hackers behind TorPedoHunt3r will try to trick you into thinking they have compromising videos or information about you and will demand from you payment to delete it.
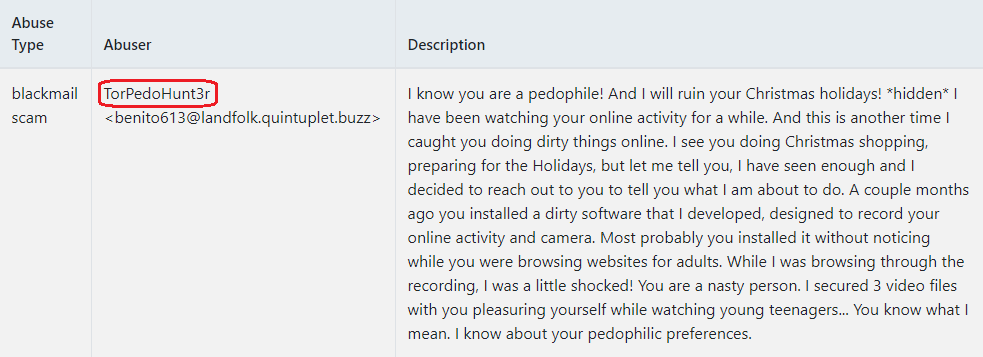
This is an example email distributed by TorPedoHunt3r.
No one likes to get infected with malware, but sometimes such things happen and when they do, one may need a helping hand to get rid of the harmful infection. With this in mind, here we’ve decided to help those of you affected by TorPedoHunt3r. This infection is classified as a Trojan Horse, and you certainly have heard about this type of malware before. The representatives of this category are known for their stealth and their unpredictable harmful abilities. So it is important that you remove TorPedoHunt3r as soon as possible before you experience its malicious potential first hand. If you don’t know how to do that, below we have prepared a special removal guide, which contains detailed step-by-step instructions. Removing a Trojan Horse, however, is a delicate process that involves handling system files. That’s why, apart from the manual instructions, you may also need a professional removal tool that will manage the entire process for you.
What damage can TorPedoHunt3r do?
One of the main characteristics of any Trojan Horse virus is that it can perform a variety of different tasks. Basically, malware of this kind can be set to take full control of your computer and launch certain malicious processes that serve the needs of some anonymous cyber criminals. For example, it could be employed for distributing spam or infecting other computers with Ransomware, Spyware, and other harmful code. Another fairly common use of the Trojans is for theft of personal information. Most often, the malware can implement techniques such as keystroke monitoring to capture sensitive information from you, as well as track your correspondence, your online activity, and everything you do on the infected computer. If you have a webcam the Trojan can secretly hack into it and allow the criminals to stalk you. If your machine has a microphone, the Trojan can compromise it and let the crooks listen to your conversations. Basically, the hackers can use the virus to access anything on your computer, including your personal information, which can later be used as a foundation for blackmailing or even physical harassment and robbery. Therefore, keeping an infection such as TorPedoHunt3r away from your system is important.
If you have already been infected, do not hesitate to use the instructions in the removal guide below to remove the malware quickly and reliably. After you do that, it is also important that you take action to protect your system from such infections in the future. One of the ways to do that is to keep your device up-to-date and to protect it with a reliable anti-malware tool. Another way is to avoid the possible sources of malware and to practice safe browsing. This involves being very careful with incoming emails or messages on other platforms, as well as spam and random pop-up ads. These may sometimes trick you into following a link or opening an attached file that could be used to distribute something malicious.
SUMMARY:
| Name | TorPedoHunt3r |
| Type | Trojan |
| Detection Tool |
TorPedoHunt3r Email Scam Removal
Search Marquis is a high-profile hijacker – you might want to see if you’re not infected with it as well.

Leave a Comment