Trackmenow.life
Trackmenow.life is a browser hijacker that may compromise your web browsing experience by flooding your Chrome, Firefox, or Explorer browser with banners, pop-up boxes, notifications, and ads. If you’ve noticed unauthorized changes to your homepage or default search engine, it’s likely that your system has been infected with it. This type of browser hijacker can be intrusive, generating unwanted elements that disrupt normal browsing. To address this issue, you can follow proven and effective removal steps provided below. Taking prompt action against Trackmenow.life ensures the manual removal of associated ads, restoring control over your browser settings and eliminating the unwanted disruptions caused by this browser hijacker.
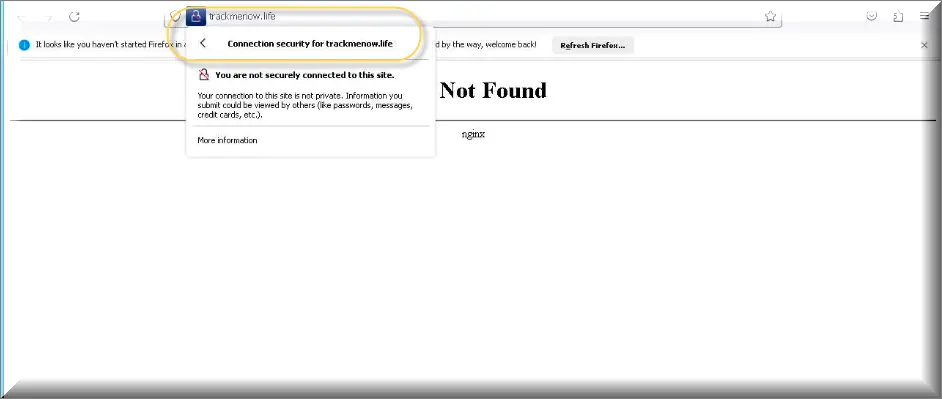
Trackmenow.life is a browser hijacker that is technically not dangerous. In some instances, however, it enormous number of advertisements, banners, pop-ups, blinking notifications, and search page-redirects to various sponsored websites can be seen as potentially unwanted.
Trackmenow.life Virus
The Trackmenow.life virus is not very dangerous, but it is still seen as a security liability because its effects on the browser could result in vulnerabilities that more dangerous programs may exploit. What makes the Trackmenow.life virus potentially dangerous is the questionable nature of the content it promotes. The purpose of hijacker apps, in general, and Trackmenow.life, in particular, is to advertise various kinds of content and to make money for its developers through its paid promotions. Showing ads and automatically page-redirecting you is, in and of itself, not a harmful activity, and it won’t damage your system. The problem comes from the content that you may get exposed to. Most hijackers would typically promote anything – from legitimate and popular sites to sketchy and potentially dangerous ones. If you end up getting an ad that links to the latter category of sites, you could obviously get your computer exposed to a diverse range of dangers, including Ransomware, Trojans, phishing forms, and more.
What is Trackmenow.life?
Trackmenow.life is a browser hijacker that targets Chrome, Edge, Firefox, and other browsers on Windows computers with the goal to use them as advertising platforms. Common Trackmenow.life symptoms are a replaced browser homepage or search engine, as well as automatic page redirects and aggressive push notifications. Most of the time, hijackers like this one manage to get into the browser in one of two ways. The first is through the help of program installers that also carry the hijacker as a bonus component that’s included in the installation by default. If the user doesn’t uncheck the hijacker clause during the installation of that other program, they’d get the unwanted software element added to their main browser. The second common distribution technique is by displaying a permission request disguised as a captcha or something similar. The user is tricked into selecting Allow in the request pop-up, and this grants the hijacker permission to operate within the browser.
The Trackmenow life Malware
Do not panic if you detect higher CPU usage, sluggish system behavior, increased use of internet data, and a steady flow of unstoppable advertisements on your screen. These are all likely caused by the activity of the Trackmenow life malware in your system. Basically, this program is created to collect telemetry information from the users’ browsers. Based on this info, the Trackmenow life malware then shows various advertising messages that can come in different forms, sizes, and colors. The main idea is to get the users to click on them, as these clicks eventually translate intro profit for the browser hijacker’s developers.The more advertisements that get displayed, and the more intrusive they are, the more difficult it is for the web users to remove or close them. This is how the well-known Pay-Per-Click method functions, and how it provides the creators of such hijacker apps (Commonsecurity.co.in, Networkhistory.co.in) with revenue.
And this is the primary reason for developing such kinds of programs. Some users may not enjoy getting constantly harassed by an infinite stream of advertisements, however, and would rather have the programs responsible for them removed.
Trackmenow life what is?
Many users may get frightened when Trackmenow life starts to aggressively redirect them to different sites, and may mistakenly refer to it as a virus infection. But the reality is, this is the worst that Trackmenow life could ever directly do to your system. And, trust us, it’s far less problematic than a real malware infection the likes of Ransomware or a Trojan horse viruses. Not only will your system be severely compromised if such harmful programs infect it, but also you may not be able to access your files until you make a ransom payment to the attackers. Fortunately, this is not something that hijackers do. Pieces of software like Trackmenow.life are entirely focused on ad-generation, and are not intended to harm your machine.
Ways to remove Trackmenow.life
As we mentioned above, the developers of programs like Trackmenow.life earn revenue from the ads this software displays, so they want to make sure that their programs remain in the computer for as long as possible. Therefore, uninstalling the Browser Hijacker can be a bit challenging. That’s why you may need some basic understanding of how to handle such software, as well as a comprehensive guide on how to uninstall it, just like the one below. Make sure you follow it carefully because if you do not pay attention, you may accidentally delete some important system file or Registry key, causing corruption and instability in your computer. For this reason, it is recommend that you try using the Trackmenow.life removal tool for a safer removal, which will automatically detect and remove the browser hijacker without any risks, in case you aren’t a very experienced computer user.
SUMMARY:
| Name | Trackmenow.life |
| Type | Browser Hijacker |
| Detection Tool |
Remove Trackmenow.life Virus
To try and remove Trackmenow.life quickly you can try this:
- Go to your browser’s settings and select More Tools (or Add-ons, depending on your browser).
- Then click on the Extensions tab.
- Look for the Trackmenow.life extension (as well as any other unfamiliar ones).
- Remove Trackmenow.life by clicking on the Trash Bin icon next to its name.
- Confirm and get rid of Trackmenow.life and any other suspicious items.
If this does not work as described please follow our more detailed Trackmenow.life removal guide below.
If you have a Windows virus, continue with the guide below.
If you have a Mac virus, please use our How to remove Ads on Mac guide.
If you have an Android virus, please use our Android Malware Removal guide.
If you have an iPhone virus, please use our iPhone Virus Removal guide
Some of the steps may require you to exit the page. Bookmark it for later reference.
Next, Reboot in Safe Mode (use this guide if you don’t know how to do it).
 Uninstall the Trackmenow.life app and kill its processes
Uninstall the Trackmenow.life app and kill its processes
The first thing you must try to do is look for any sketchy installs on your computer and uninstall anything you think may come from Trackmenow.life. After that, you’ll also need to get rid of any processes that may be related to the unwanted app by searching for them in the Task Manager.
Note that sometimes an app, especially a rogue one, may ask you to install something else or keep some of its data (such as settings files) on your PC – never agree to that when trying to delete a potentially rogue software. You need to make sure that everything is removed from your PC to get rid of the malware. Also, if you aren’t allowed to go through with the uninstallation, proceed with the guide, and try again after you’ve completed everything else.
- Uninstalling the rogue app
- Killing any rogue processes
Type Apps & Features in the Start Menu, open the first result, sort the list of apps by date, and look for suspicious recently installed entries.
Click on anything you think could be linked to Trackmenow.life, then select uninstall, and follow the prompts to delete the app.

Press Ctrl + Shift + Esc, click More Details (if it’s not already clicked), and look for suspicious entries that may be linked to Trackmenow.life.
If you come across a questionable process, right-click it, click Open File Location, scan the files with the free online malware scanner shown below, and then delete anything that gets flagged as a threat.


After that, if the rogue process is still visible in the Task Manager, right-click it again and select End Process.
 Undo Trackmenow.life changes made to different system settings
Undo Trackmenow.life changes made to different system settings
It’s possible that Trackmenow.life has affected various parts of your system, making changes to their settings. This can enable the malware to stay on the computer or automatically reinstall itself after you’ve seemingly deleted it. Therefore, you need to check the following elements by going to the Start Menu, searching for specific system elements that may have been affected, and pressing Enter to open them and see if anything has been changed there without your approval. Then you must undo any unwanted changes made to these settings in the way shown below:
- DNS
- Hosts
- Startup
- Task
Scheduler - Services
- Registry
Type in Start Menu: View network connections
Right-click on your primary network, go to Properties, and do this:

Type in Start Menu: C:\Windows\System32\drivers\etc\hosts

Type in the Start Menu: Startup apps

Type in the Start Menu: Task Scheduler

Type in the Start Menu: Services

Type in the Start Menu: Registry Editor
Press Ctrl + F to open the search window

 Remove Trackmenow.life from your browsers
Remove Trackmenow.life from your browsers
- Delete Trackmenow.life from Chrome
- Delete Trackmenow.life from Firefox
- Delete Trackmenow.life from Edge
- Go to the Chrome menu > More tools > Extensions, and toggle off and Remove any unwanted extensions.
- Next, in the Chrome Menu, go to Settings > Privacy and security > Clear browsing data > Advanced. Tick everything except Passwords and click OK.
- Go to Privacy & Security > Site Settings > Notifications and delete any suspicious sites that are allowed to send you notifications. Do the same in Site Settings > Pop-ups and redirects.
- Go to Appearance and if there’s a suspicious URL in the Custom web address field, delete it.
- irefox menu, go to Add-ons and themes > Extensions, toggle off any questionable extensions, click their three-dots menu, and click Remove.
- Open Settings from the Firefox menu, go to Privacy & Security > Clear Data, and click Clear.
- Scroll down to Permissions, click Settings on each permission, and delete from it any questionable sites.
- Go to the Home tab, see if there’s a suspicious URL in the Homepage and new windows field, and delete it.
- Open the browser menu, go to Extensions, click Manage Extensions, and Disable and Remove any rogue items.
- From the browser menu, click Settings > Privacy, searches, and services > Choose what to clear, check all boxes except Passwords, and click Clear now.
- Go to the Cookies and site permissions tab, check each type of permission for permitted rogue sites, and delete them.
- Open the Start, home, and new tabs section, and if there’s a rogue URL under Home button, delete it.

Leave a Comment