*Uajs is a variant of Stop/DJVU. Source of claim SH can remove it.
The Uajs File
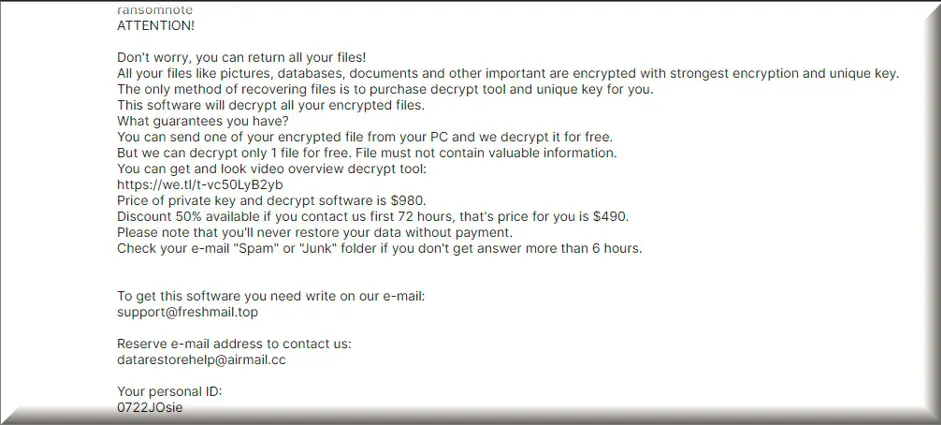
When your computer gets hit by ransomware, such as the Uajs file, it’s like digital extortion. The bad guys lock up your files and demand a ransom, usually in cryptocurrency, for the key to unlock them. Now, getting rid of the actual ransomware from your computer is possible, and you can do it with antivirus software or by seeking help from cybersecurity experts. That’s the first step. But here’s the catch: even if you manage to kick the ransomware out and remove all Uajs files, your digital data may remain encrypted, and paying the ransom doesn’t guarantee you’ll get the decryption key for it.
How to decrypt Uajs ransomware files?
Decrypting Uajs ransomware files hinges on several factors, including the type of ransomware, its encryption strength, and the existence of decryption tools developed by security experts. While some ransomware variants have decryption solutions available, there’s no universal guarantee. Paying the ransom isn’t advisable, as it funds cybercriminal activities and doesn’t guarantee file recovery. Therefore, prevention through regular backups, software updates, and cautious online behavior is the best defense against ransomware.
How to remove Uajs ransomware virus and restore the files?
Removing the Uajs ransomware virus is a critical first step, often done with antivirus software or professional help. However, restoring the encrypted files can be challenging. It’s important to have backups of your data, as paying the ransom is discouraged due to no assurance of file recovery and supporting cybercriminals. Consulting cybersecurity experts is advisable, but be prepared for the possibility of permanent data loss. Therefore, prevention is key; regularly back up your data, keep software up-to-date, and practice safe online habits to avoid ransomware infections.
The Uajs virus
Paying the ransom to the crooks behind the Uajs virus is a risky move. These cybercriminals are not exactly trustworthy individuals, and there’s no honor among thieves, right? So, they might take your money and not send you the key, or the key may not work correctly. Moreover, paying ransoms just fuels their illegal activities and encourages them to keep doing this kind of stuff. So, many experts, including law enforcement agencies, generally advise against it. Therefore, if you become a victim of Uajs, Vook or Looy virus, it is best to consult with cybersecurity experts for advice, or use a detailed manual removal guide like the one below.
Uajs
If you’ve got the Uajs ransomware on your computer, and these cybercriminals are holding your files hostage, there are a few things you can do. The crooks are demanding money, usually in cryptocurrencies like Bitcoin, to give you the key to unlock your files. Now, paying that ransom might seem like a quick fix, a way to get your precious Uajs encrypted files back. But it’s a risky move, and there’s no guarantee you’ll get your files back even if you pay up. The cybercriminals are not exactly known for their trustworthiness. They might take your money and run, or they might send you a faulty decryption key that doesn’t work. So, you’d be out of cash and still without your files.
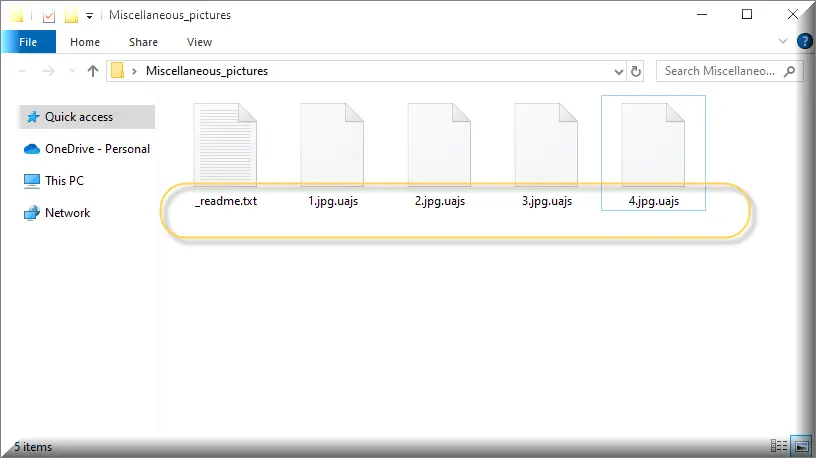
.Uajs
If you’ve got the bad chance to infect your computer with ransomware and get your files encrypted with the .Uajs encryption, don’t panic. There are steps you can take. First, disconnect from the internet or any network you’re on. This will prevent the ransomware from spreading to other devices or encrypting more files. Next, do a full system scan with your antivirus software. Some antivirus programs can detect and remove ransomware quite effectively. If your antivirus doesn’t catch it, don’t worry; it’s not uncommon. As an alternative, you can use our detailed .Uajs removal guide and the detailed instructions provided in it.
Uajs Extension
Keep in mind that paying the ransom in order to remove the Uajs extension isn’t your best option, as we discussed earlier. So, avoid doing that unless you’ve consulted with experts who believe it’s your only way out. Of course, you can learn from this experience. Ransomware attacks often happen due to unsafe online practices. Therefore, you need to be extra cautious with email attachments, downloads, and clicking on suspicious links. Regularly back up your important data, and keep your software up-to-date to prevent future infections. It’s all about staying safe in the digital world and avoiding any encounter with the Uajs extension.
Uajs Ransomware
Unfortunately, there can be legal consequences when it comes to paying a ransom to the cybercriminals behind Uajs Ransomware, and it’s important to understand them. Firstly, when you pay a ransom, you’re essentially sending money to individuals or groups involved in illegal activities. This can get you entangled with the law. Depending on your location and the specific circumstances of the ransom payment, you might find yourself on the wrong side of the legal system. Moreover, paying the ransom doesn’t guarantee that you’ll get your files back or that the cybercriminals won’t target you again. So, you might end up losing your money without any positive outcome. Given these legal and financial risks, it’s generally advised to seek assistance from cybersecurity professionals rather than complying with the demands of the Uajs ransomware.
What is Uajs File?
An Uajs file is essentially any regular file that has fallen victim to a ransomware attack. This means that cybercriminals have used malicious software to lock up this file, making it inaccessible to the rightful owner. Therefore, backing up your data is an essential part of protecting against ransomware. But how often should you do it? The frequency of your backups depends on how much data you can afford to lose. If you can’t bear the thought of losing even a day’s worth of work or precious files, then daily backups are your best friend. This means copying your data to a secure location every single day. If you can manage with losing a little more data, then weekly backups might suffice. It’s a good balance between safety and convenience.
SUMMARY:
| Name | Uajs |
| Type | Ransomware |
| Detection Tool |
*Uajs is a variant of Stop/DJVU. Source of claim SH can remove it.
Uajs Ransomware Removal

If you’ve been infected with Uajs, the first thing you should do is bookmark this webpage with removal instructions, so you can have quick access to it. Next, the infected machine should best be rebooted in Safe Mode, as explained in this link. Once you’ve done these preparations, you can safely proceed to the instructions below to remove the traces of Uajs from your computer.

WARNING! READ CAREFULLY BEFORE PROCEEDING!
*Uajs is a variant of Stop/DJVU. Source of claim SH can remove it.
The next step is to look for any processes associated with the ransomware in the Processes tab of the Task Manager. You open the Task Manager, press CTRL + SHIFT + ESC keyboard keys together, then select the second tab from the top. Look at how much CPU or memory the processes consume, or look at their names to identify any suspicious-looking ones.
When you isolate a suspicious process and right-click on it, you can select Open File Location, and check its files for malicious code.

To be on the safe side, these files need to be scanned with an antivirus program. Those without access to a reputable anti-virus program can use the free online virus scanner provided below:

If the scan results show that there is a danger, right-click on the process that is associated with the infected files and select End Process. The File Location folder must be cleared of all dangerous files before moving on.

In the third step, we will explain to you how to look for any alterations to your system’s Hosts file that can indicate a possible hacking. To do that, hold down the Windows key and R at the same time, then copy/paste the line below in the Run window that pops on the screen and press Enter:
notepad %windir%/system32/Drivers/etc/hosts
In the text of the file, look for anything strange under Localhost, such as Virus Creator IPs like those on the example image below:

If you come across such IPs under “Localhost,” please leave us a comment below this post. They’ll be checked by a member of our team, who will tell you what to do if anything suspicious is found.
As long as there are no unauthorized modifications in your Hosts file, you don’t need to do anything. Just close the Hosts file and return to the Windows Search field.
Type msconfig in the search and press Enter:

Select “Startup” from the tabs at the top, and be sure to do some online research on any startup items with “unknown” manufacturer or random names that you find in the list. If you find enough information that a specific startup item is dangerous and is connected to Uajs, you can disable it by unchecking its respective box and clicking OK.

*Uajs is a variant of Stop/DJVU. Source of claim SH can remove it.
Once it has gained access to the system, ransomware like Uajs has the potential to add malicious entries to the registry. What is more, it is possible that the malware could resurface if these registry entries aren’t removed. Therefore, you’ll need to go through your registry and carefully search it in order to completely remove Uajs.
Attention! There is a risk of system corruption when important registry files and apps are modified or deleted. For this reason, ransomware victims are advised to remove potentially hazardous files from critical system locations like the registry only with the help of specialized malware removal tools.
If you want to proceed with the manual removal of Uajs anyway, please open the Registry Editor and check for Uajs-related entries that need to be removed.
To do that, type regedit in the Windows search field and hit Enter. When the Registry Editor starts, press CTRL and F from the keyboard to access the Editor’s Find window. In it, type the ransomware’s name and start a search. If there are files with that name in the search results, they need to be carefully deleted.
Using the Windows Search field, run a new manual search for Uajs-related files in each of the five locations listed below:
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
If there are no suspicious files or subfolders, you should not make any changes. However, if there are, you should get rid of them. To remove the ransomware’s temporary files, just delete everything in the Temp directory.

How to Decrypt Uajs files
The decryption method for your encrypted data may be different depending on the type of ransomware that has attacked you. The file extension added to the encrypted files can help you identify which Ransomware variant has attacked you.
New Djvu Ransomware
STOP Djvu Ransomware is the most recent version of the Djvu Ransomware. The .Uajs file suffix tell this new version apart from other variants of the ransomware. The good news is that files encrypted with an offline key can currently be decrypted. You can download a decryption software by clicking on the following link:
https://www.emsisoft.com/ransomware-decryption-tools/stop-djvu
Decryption
To start the decryption tool, select “Run as Administrator” and then click Yes. Before proceeding, please read the license agreement and the on-screen instructions carefully. Simply click on the Decrypt icon and follow the on-screen instructions to decrypt your data. It is important to keep in mind that this tool cannot decrypt data that has been encrypted with unknown offline keys or online encryption.
Attention! Remove all files associated with ransomware before attempting to decrypt any files. An anti-virus program like the one on this page and a free online virus scanner can be used to remove infections like Uajs and other malware from the system.

Leave a Comment