What Type of Malware is Waqa?
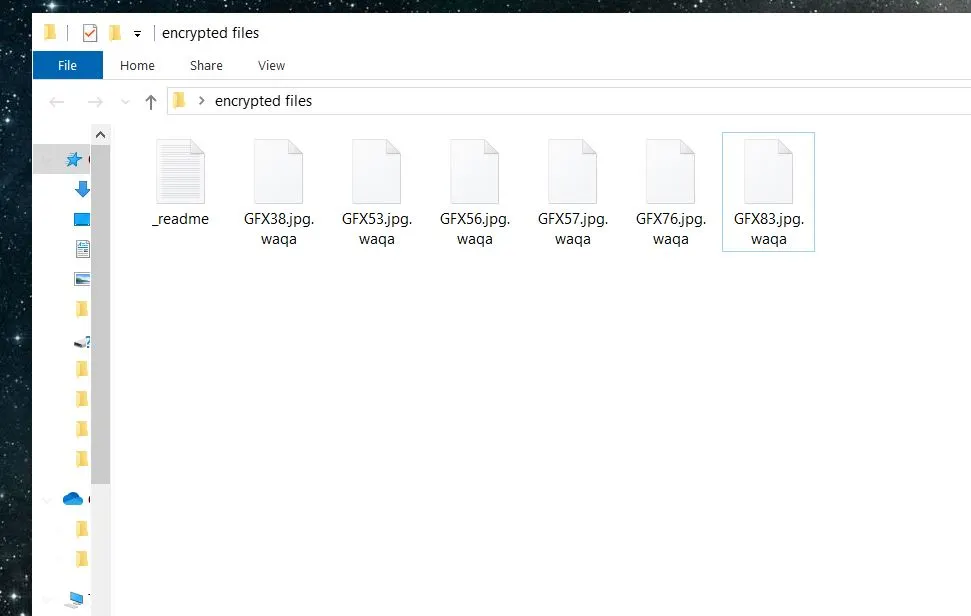
The .waqa virus is a menacing breed of malware known as ransomware. It belongs to a special category of advanced ransomware that belongs to the DJVU family tree. Other recent threats from this malware family are the Vehu Virus and the Vepi Virus. This pernicious software encrypts user files to make them unavailable and then the hackers ask for a ransom payment to release the locked data.
Waqa and other DJVU threats enter systems through deceptive links, pirated programs, and disguised email attachments, among other methods. The virus operates in silence and adds the .waqa extension at the end of the file names once it completes the encryption. The victims find themselves cornered with a payment demand but uncertainty if that would get them the files restored.
Our goal in this post is to get you more familiar with Waqa and, if you are among its victims, talk you through your available options and provide any assistance that we can.
What Does Waqa Do to Your files?
The Waqa ransomware initiates a complex and stealthy process that targets the victim’s files for encryption as soon as it lands in the system. This malware first scans the computer’s directories for specific file types – text documents, images, and databases are among the most frequent targets. Waqa will identify the targeted files and then employ a sophisticated encryption algorithm – AES or a similar cipher – that locks the data. This process transforms each file into an unreadable format that no program can open. The .waqa extension at the end (it’s added behind the regular file extension) shows that the file is no longer accessible.
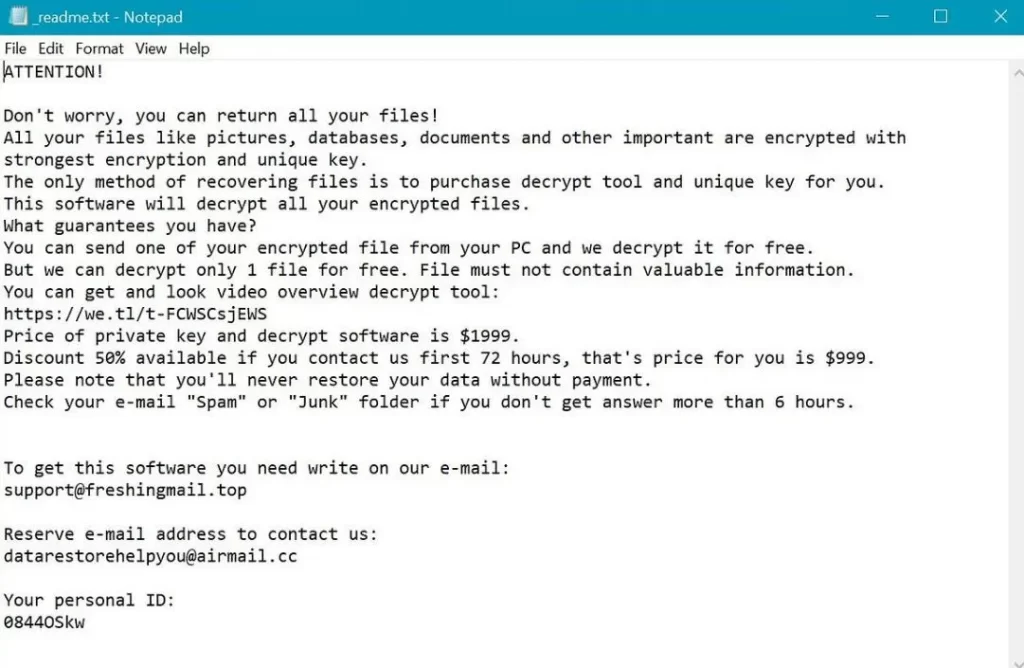
This encryption method uses a unique encryption key that gets generated on the attacker’s server which means that no one else can access it. The key to unlock the files is not stored on the victim’s computer so self-recovery is nearly impossible without external assistance. The strength of this encryption is in its specificity – each victim’s key is different, so it’s very difficult to create a universal decryption tool.
The encrypted state essentially locks out the user from their own data. The obvious end goal is to coerce the victims to pay a ransom that’s almost always required in crypto to maintain the anonymity of the attackers. The combination of strong encryption, unique keys, and anonymous payment demands makes .waqa a particularly problematic and resilient threat.
What to Do if Waqa Has Your Files?
You have several possible courses of action if Waqa ransomware has ensnared your files, but know that none of the options is ideal. The first thing many consider is to go for the ransom. This approach might seem like a straightforward way to regain access to your data but it’s probably the worst one. You have no guarantee the attackers will actually provide a decryption key after payment. The only certain thing is that your payment will encourage them to continue with their blackmailing schemes.
An alternative is to seek a decryption tool online. Cybersecurity experts work all the time to develop free decryptors for different ransomware variants and then make them public for anyone to use. This option is ideal because it will restore access to your data and you won’t have to pay anything to the criminals. The problem is that Waqa is a very new threat so could be months before it receives a decryptor (if it ever does).
Another sensible option is to restore files from backups. This is the safest and most reliable method but is only available to people who regularly back up their data and keep the backups separate from the network to avoid infection. This method doesn’t cost anything and means you won’t have to contact the hackers, but is only viable if such foresight was practiced before the attack.
You must also remember that the virus must first be removed from your PC before you attempt to restore anything from backups or decrypt the files with a free decryptor tool. We can show you how to delete Waqa from your system in the guide below this article.
How Did Waqa Infect You?
The .waqa ransomware uses various distribution vectors that exploit vulnerabilities within system defenses and also in user behavior patterns. One common technique is phishing messages – emails or other online messages disguised as legitimate communications from trusted sources. They contain malicious attachments or links that deploy the ransomware if you click on them.
Another prevalent method is called malvertising. This is when cybercriminals inject malicious code into online ads and the ransomware gets downloaded when the user clicks the advert. This method is not as common because legitimate sites strictly monitor the ads they allow to appear on them.
Exploit kits represent a more passive but equally dangerous vector. These kits scan for vulnerabilities in software on a user’s computer like outdated applications or unpatched systems they use the security holes to inject the ransomware. The automated nature of exploit kits allows them to infect machines en masse without any user interaction, other than visiting a compromised website.
Ransomware operators also leverage downloadable software and fake updates. They disguise malware as a necessary security patch or desirable software and thus persuade the user to allow the rogue program onto their machines.
Each of these methods shows the opportunistic nature of ransomware campaigns, which exploit everyday activities and the inherent trust users place in digital communications and websites.
The Waqa Ransomware – Conclusion and Tips
The Waqa ransomware exemplifies the sophisticated and insidious nature of modern cyber threats. It is essential to maintain robust cybersecurity practices to guard against such attacks from now on.
You must always be cautious with email attachments and links even when you know the sender. Keep your programs and OS to ensure that the latest vulnerabilities are patched. Use a reputable antivirus (preferably with verified ransomware detection capabilities) and configure for automatic scans. It’s also critical to establish a routine for backing up important data to external drives or cloud storage.
SUMMARY:
| Name | Waqa |
| Type | Ransomware |
| Detection Tool |
Remove Waqa Ransomware

Next, since Waqa may run a number of malicious processes as a background, it is best if you run only the most essential system processes and apps in order to be able to easily spot the malicious ones. For this, we advise you to reboot the infected PC in Safe Mode (use the free instructions from the link) and then get back to this removal guide by clicking on its bookmark.

WARNING! READ CAREFULLY BEFORE PROCEEDING!
With the infected computer launched in Safe Mode, click on the Start menu button and type msconfig in the search bar. Then open the result and a System Configuration window will open:

If you detect anything suspicious, research it online and, based on the information you collect, decide whether you need to disable it.
To disable a suspicious startup entry, remove its checkmark from the related checkbox and click OK.
Next, head to the Windows Task Manager (CTRL + SHIFT + ESC) and select the Processes Tab. Similarly to what you did in the Startup tab, search the list of processes for suspicious entries. Keep in mind that Waqa may hide its malicious processes under different names that may mimic the names of legitimate processes. If you detect an entry that looks suspicious, (uses a lot of CPU and Memory without any particular reason, has an odd name, etc.) here is how to check it:
- right-click on the process in question
- select Open File Location


- end the processes in question if one or more of its files get flagged as dangerous.

A typical location where a ransomware like Waqa may make unauthorized changes is the Hosts file of the infected computer. To check it, you need to copy the line below in the Start menu search bar and press Enter:
notepad %windir%/system32/Drivers/etc/hosts
The Hosts file will open in Notepad.
Search for Localhost in the text, and if you find it, check if any virus creator IP addresses have been added there. The image below can give you an idea of how should those IPs look like.

If you detect nothing suspicious in your Hosts file, just close it down. If something disturbing catches your attention, though, don’t rush to delete it. Better write to us in the comments with a copy of what is bothering you.

In case of a ransomware infection, you may need to clean the Registry from malicious entries that the virus has added there. To do that, type Regedit in the Start menu search bar and press Enter.
This will launch the Registry Editor on your screen. Next, press CTRL and F together and type the Name of the virus that has infected you and start a search. If any entries show up in the results, they most likely are linked to the ransomware and need to be removed from the Registry.
NB!!! A serious system damage may occur if you delete entries nor elated to the ransomware from your registry. To avoid the risk of OS corruption, please use a professional removal tool to clean your registry from malicious files.
Next, close the Registry Editor once you are sure the Registry is clean from malicious entries and click on the Start menu button. In the search field, type each of the lines below one by one and open the result:
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
In case you detect entries with odd names consisting random characters, or entries that have been added close to the time you got infected with Waqa , they most likely need to be removed.
You also need to remove all the files in the Temp folder, as these are temporary files that could be related to the ransomware.

How to Decrypt Waqa files
Once Waqa is gone from your PC and you are sure your system is secure, we recommend checking the file-recovery suggestions that can be found here.
You can also click the next link and then follow the instructions below it to attempt to decrypt your files using a free decryptor tool from Emisoft.
https://www.emsisoft.com/ransomware-decryption-tools/stop-djvu
- Download the Decryptor: Click the ‘Download’ button at the top of this page to save the STOPDjvu.exe decryptor onto your computer.
- Launch the Tool: After downloading, right-click on the file and select “Run as Administrator” to start the decryptor.
- Initiate Decrypting Process: Follow the on-screen instructions to read the license agreement and complete the setup. The decryption should start immediately after setup.
- Check Encryption Type: Note that if your files were encrypted with an unknown offline key or online, the decryptor might not successfully decode them.
- Ensure Malware Removal: Before starting the decryption, ensure the ransomware is completely removed from your system. Use specialized anti-virus software to scan your computer. We recommend using the anti-virus software available on our site. You can also use a free online virus scanner to check individual files for safety.
- Seek Help if Needed: If you encounter any issues or have questions about the process, post your concerns in the comments section below. A member of our team will respond to assist you shortly.

Leave a Comment