This page aims to help you remove Werfault.exe Virus. Our removal instructions work for every version of Windows.
The authentic Werfault.exe file is a Microsoft Windows system process and is safe. Very often, however, the creators of malicious programs such as viruses, worms and Trojans quite deliberately give their processes the same file name to avoid detection. If Werfault.exe is located in a subfolder of the user’s profile folder, the security rating is 84% unsafe.
What is a Trojan horse and why is it so fearful?
Nowadays, the online space is full of threats of different types. Some of the most tricky and most dangerous, however, are the Trojans. These malicious pieces of software are responsible for more than seventy percent of all the infections that happen through the Internet according to some recent statistics, so the chance of encountering one is very big. The key to the successful infection rate of the Trojans lies in the stealthy distribution and infection methods they use. Basically, viruses like Werfault.exe try to mislead you about their real purpose and goal, making you believe you are interacting with some interesting and harmless content or installing a useful app. This way, they can easily enter the system and get down to their criminal business without your knowledge. The damage the Trojans can cause can be very serious and, in some cases, even irreparable. That’s why, the sooner you scan your system and remove the infection, the greater the chances of saving yourself from some really unpleasant consequences are.
What is the possible harm that Werfault.exe may cause?
If we have to be very honest, we cannot tell you what exactly Werfault.exe may cause and this is the most dangerous thing about this Trojan. Its criminal creators may program it for a number of illegal tasks. For instance, they can set it to delete certain files from your PC, format your disks or make changes to your software. They may also use it to track down all of your activity and secretly collect information about you, your work, your online profiles and your personal life and use this information to harass and blackmail you. Also, they can gain access to your accounts by stealing your passwords and login credentials. As a result, you may end up with your money or identity stolen, your credit or debit cards drained and your machine totally compromised. The hackers may gain control over the PC, modify, replace, and install whatever they want and employ the system’s resources for shady deeds like cryptocurrency mining, spam, and Ransomware distribution or some other botnet-related activity. And these are just some of the terrible consequences you may face if you have a threat like Werfault.exe on your computer.
What are the sources of the Trojan infection?
The possible sources of Trojan infections are, unfortunately, as many as the possible malicious uses of such viruses. It is very difficult to say in what form the infection could appear because the hackers tend to camouflage the virus in seemingly harmless forms of content such as executables, images, videos or audio files. They may spread Werfault.exe or Msedge.exe via Torrents, spam emails, and attachments, social shares, free download packages, software installers, infected web pages, fake ads, misleading links and many more. The key to staying safe is to be cautious while surfing the web space and protect your computer with reliable antivirus software.
Can prevention keep threats like Werfault.exe away from my PC?
If we have to give you one piece of advice about Trojans and their preventing attacks from them, we would first suggest you make your system safe by updating it to the latest security patches. Many users neglect that but malicious pieces like Werfault.exe can sneak undetected by exploiting system vulnerabilities. That’s why it is extremely important to have your OS duly updated to keep it as safe as possible. Using a reliable antivirus tool and running regular scans is the next important thing. Of course, you have to be careful when surfing the Internet and keep away from anything that may be potentially malicious, so don’t get tempted to click on every pop-up, link or blinking box that appears on your screen. You may land on infected web locations this way and no one might be able to save you then.
Is it possible to remove Werfault.exe effectively?
Fortunately, removing Werfault.exe is a possible task. However, it requires all of your attention. That’s why we suggest you carefully proceed with the instructions in the Removal Guide below and use them in combination with the professional Werfault.exe removal tool we have suggested here for optimal results.
SUMMARY:
| Name | WerFault.exe |
| Type | Trojan |
| Danger Level | High (Trojans are often used as a backdoor for Ransomware) |
| Symptoms | This infection may lack any particular symptoms, which makes it very difficult to detect. |
| Distribution Method | Torrents, spam emails, and attachments, social shares, free download packages, software installers, infected web pages, fake ads, misleading links |
| Detection Tool |
Remove WerFault.exe Virus

Some of the steps will likely require you to exit the page. Bookmark it for later reference.
Reboot in Safe Mode (use this guide if you don’t know how to do it).

WARNING! READ CAREFULLY BEFORE PROCEEDING!
Press CTRL + SHIFT + ESC at the same time and go to the Processes Tab. Try to determine which processes are dangerous.

Right click on each of them and select Open File Location. Then scan the files with our free online virus scanner:

After you open their folder, end the processes that are infected, then delete their folders.
Note: If you are sure something is part of the infection – delete it, even if the scanner doesn’t flag it. No anti-virus program can detect all infections.

Hold together the Start Key and R. Type appwiz.cpl –> OK.

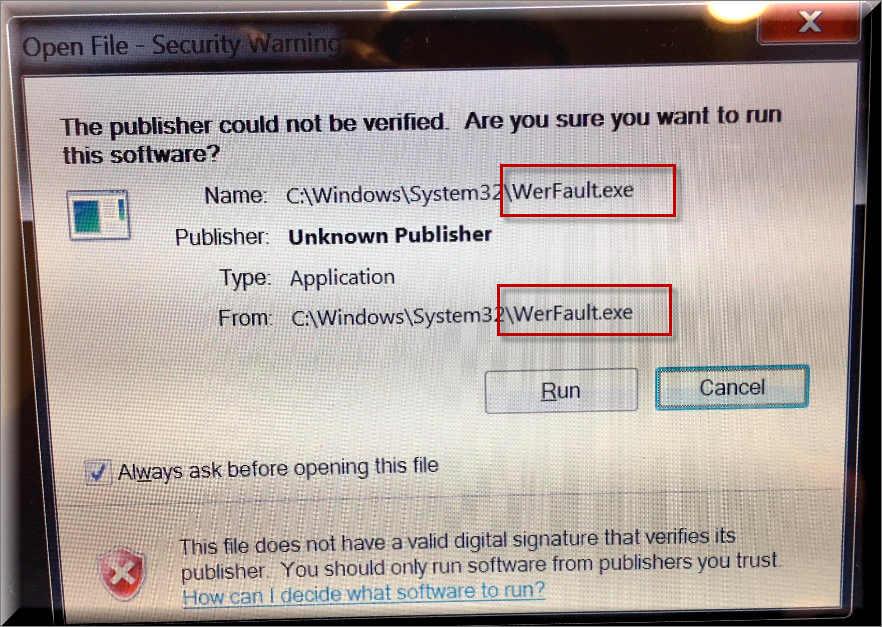
You are now in the Control Panel. Look for suspicious entries. Uninstall it/them. If you see a screen like this when you click Uninstall, choose NO:


Type msconfig in the search field and hit enter. A window will pop-up:

Startup —> Uncheck entries that have “Unknown” as Manufacturer or otherwise look suspicious.
- Remember this step – if you have reason to believe a bigger threat (like ransomware) is on your PC, check everything here.
Hold the Start Key and R – copy + paste the following and click OK:
notepad %windir%/system32/Drivers/etc/hosts
A new file will open. If you are hacked, there will be a bunch of other IPs connected to you at the bottom. Look at the image below:

If there are suspicious IPs below “Localhost” – write to us in the comments.

Type Regedit in the windows search field and press Enter.
Once inside, press CTRL and F together and type the virus’s Name. Right click and delete any entries you find with a similar name. If they don’t show up this way, go manually to these directories and delete/uninstall them:
- HKEY_CURRENT_USER—-Software—–Random Directory. It could be any one of them – ask us if you can’t discern which ones are malicious.
HKEY_CURRENT_USER—-Software—Microsoft—-Windows—CurrentVersion—Run– Random
HKEY_CURRENT_USER—-Software—Microsoft—Internet Explorer—-Main—- Random
If the guide doesn’t help, download the anti-virus program we recommended or try our free online virus scanner. Also, you can always ask us in the comments for help!

Leave a Comment