This page aims to help you uninstall Win Tonic Malware. Our removal instructions work for every version of Windows.
In the following article, you will be introduced to a program called Win Tonic that a number of users and security researchers have regarded as unwanted. If you currently have Win Tonic but want to have it removed, we can help you uninstall it from your system – a separate guide regarding that will be presented to you at the bottom of the article.
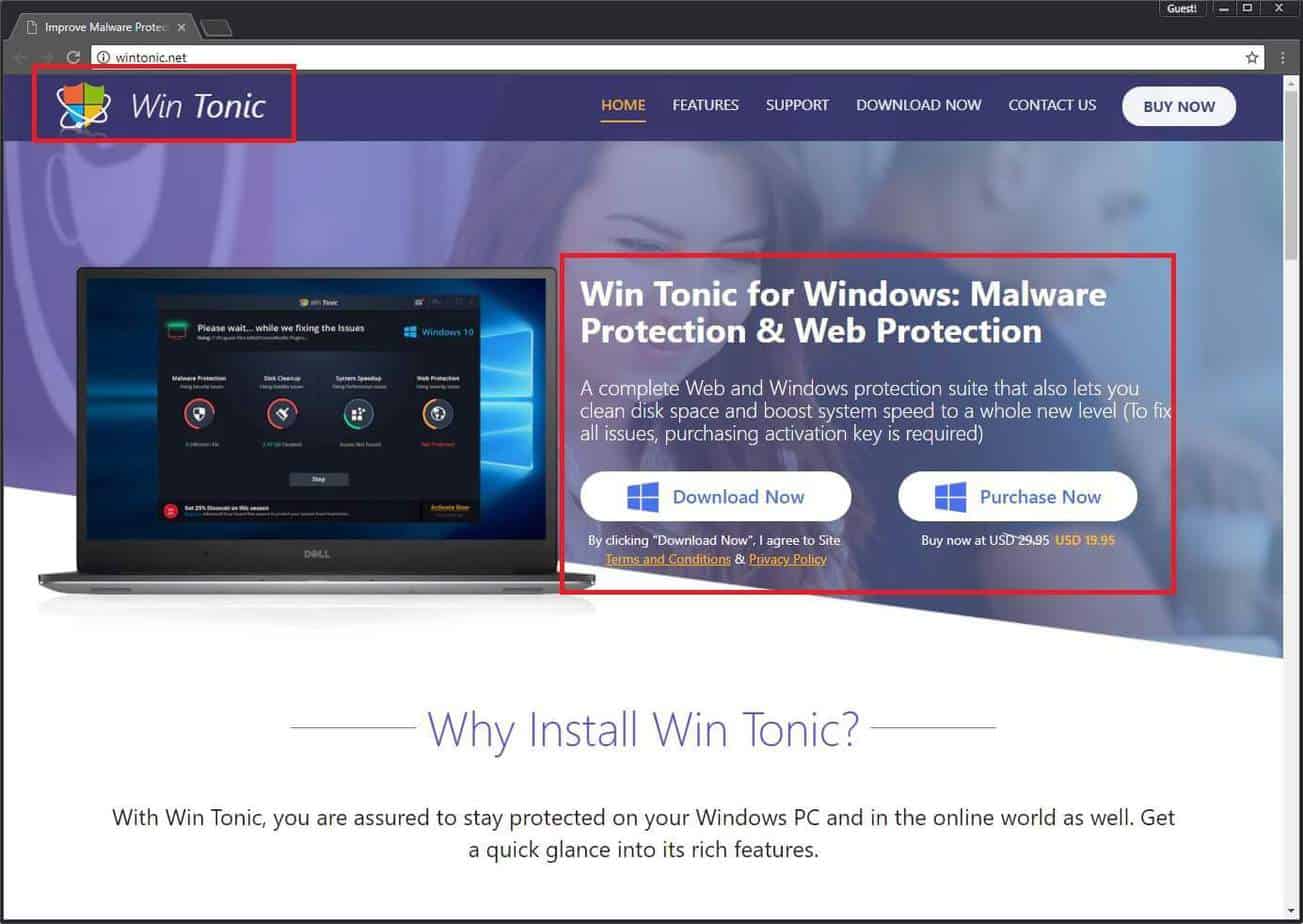
Pretty much everybody wants their computer to run faster and smoother, to be cleaner and to have no errors or issues of any sort. There are programs out there that can help users achieve that. However, there are also many software developers that seek to exploit people’s desire for a more optimized system. This is what has lead to the development of many “system optimizers” – programs that seemingly offer you to improve the performance of your computer and clean it off anything unwanted. However, a notorious trait of many of such software tools is that they tend to show false positives when scanning your PC. Oftentimes, such a program might “detect” some issue on your computer and tell you that the problem needs to be taken care of when in reality there’s nothing wrong with your computer. On this page, we will review one system optimizer tool called Win Tonic that has been reported by several cyber-security experts to have this same tendency of showing false or exaggerated results to the users and then prompting them to make a purchase for the program’s license.
About Win Tonic
As we already mentioned, Win Tonic is a legitimate optimizer tool that is supposed to boost and enhance the performance of the computer by cleaning redundant data and registry keys. On paper, this should indeed improve the way your computer works. However, in many instances with such programs, the improvement is barely noticeable if there’s any improvement at all. On the flip side, it has been reported that Win Tonic tends to show fake positive results when it scans the computer. One thing to mention here is that you could download the application for free but that way there would be only a limited number of features that you could use the main one being the scanner. Once you use that scanner, it is likely that even if there aren’t any problems with your PC the program will show you that something needs improvement. This is when you would get prompted to buy the full version in order to resolve the detected issues. However, since there might not be any issues whatsoever, it is likely that you wouldn’t even need the full version of Win Tonic (or the free one for that matter). Unfortunately, this is how many such optimizer tools function and many users fall for the exaggerated (or fake) warnings and buy the license for the software. This is the main reason why those programs are oftentimes regarded as PUPs (potentially unwanted programs) and why users typically want to have them removed. As we said above, we can help you with the removal of Win Tonic – just follow the instructions below and meticulously complete all of the steps. Once you are done, there should be nothing left from the PUP on your PC. In case you need extra help, feel free to contact use through the comments section – we will make sure to get back to you once we see your request.
Avoiding unwanted software
Potentially unwanted programs are all over the Internet and it is easy to get one such program installed on your computer without even realizing it. Win Tonic has an official site from where users could download it but it is also possible that other distribution methods are also employed to distribute such software. One example are the so-called file bundles – the unwanted software is put inside the installer file of some other software (normally some free program). Since most users normally choose the Quick setup configuration when installing anything, any added/bundled software gets installed by default alongside the main program of the bundle. However, you can prevent this from happening to you as long as you remember to opt for the expanded setup settings – Advanced/Manual/Custom is how they are normally labeled. From there, you would have more control over the installation process and you will be able to leave out any of the bundled applications that you consider to be unwanted on your computer. Note that there are also many other methods for distributing unwanted software – spam messages, malvertising, pirated downloads, etc. so make sure that you always stay careful when on the Internet so as to avoid interaction with any web content that might get you some undesirable or maybe even hazardous software.
SUMMARY:
Uninstall Win Tonic Malware
You are dealing with a malware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to clean up and reset your browser to its original settings without the malware returning.
You can find the removal guide here.

Leave a Reply