*Source of claim SH can remove it.
Winlogson
This page aims to help you remove Winlogson virus. Our removal instructions work for every version of Windows.
We are sure that whatever your level of computer literacy and however long you have been using a PC for work or leisure, you are bound to have heard about a virus type known as Trojans. These are the most infamous pieces of malware and zillions of new variants are being released onto the public each year. One of the latest Trojan horse viruses is called Winlogson Malware and it has been infecting a number of computers across the globe. We have received complaints about it from some of our readers as well and that it precisely why we have created the current article. In it we will aim to provide you and the other victims of Winlogson Malware with the most basic information about this malware. In addition, we will give you some advice on how to prevent infections of this type in the future. But more importantly, we have also designed a detailed removal guide to help you remove Winlogson Malware from your system once and for all. Users, who would prefer to have a program handle this business for them, can also make use of our professional removal tool – also located below on this page.
What Trojans do
Have you ever wondered why Trojan horses are perhaps the only virus type you’ve heard of? This is the case for most web users and the reason is because Trojans happen to be the most common virus type out there. Three in every four malware infections are actually caused by Trojan horses. And the reason why viruses like Winlogson and Altruistics are this popular with hackers is because they can be programmed for a very wide range of purposes. It’s, in fact, impossible to even say what Winlogson may exactly be up to on your particular machine. The thing is that the hackers can remotely set to do just about anything.
As an example of what ‘anything’ entails, we will name some of the most common usages of this malware type. Number one on the list would probably be theft. Trojans are masters of stealing information from their victims and they employ a variety of tactics to achieve this. For example, they can keep track of your keystrokes and, thus, gain access to virtually everything you type with the help of your keyboard. This includes logins, passwords, emails, financial and personal details, etc. Alternatively, Trojans can also destroy information. This can be done by singling out specific files or just crashing your system and wiping it clean of any data at all.
Other possibilities include spying on their victims. Trojan horse viruses have the capability to act as the eyes and ears of the cybercriminals behind them on your PC. As such, they can tap into your webcam or hack your microphone, or why not both even? In addition, a virus like Winlogson can even share your screen with the hackers and use the same keystroke logging methods mentioned above to see exactly what you do and write on your computer. Throw in the fact that they can easily also track your location and you have the perfect recipe for disaster: harassment, stalking and physical crimes of all sorts could follow. Besides this, your PC can also be made to send out spam or infect other computers with malware. Furthermore, Trojans are also often used to act as backdoors for other viruses, most commonly ransomware.
… and the list goes on and on. For this reason it’s very important that you detect viruses like Winlogson quickly after they have made their way into your system and see to their timely removal. There’s no telling what kind of damage they may cause and it’s best not to wait long enough to find out. But wouldn’t it be even better to have prevented the attack in the first place? This could have been done, for example, if you had regularly updated your antivirus program, as well as your OS. Outdated software of any kind often forms a vulnerability and makes your PC more susceptible to external threats. In addition, avoiding potential malware transmitters will also go a long way. These are mainly spam emails and contaminated or insecure web locations. Be cautious and critical towards the content you are about to interact with and if you have reason to not fully trust it – it’s best to not interact with it at all.
| Name | Winlogson.exe |
| Type | Trojan |
| Danger Level | High (Trojans are often used as a backdoor for Ransomware) |
| Detection Tool |
*Source of claim SH can remove it.
Remove Winlogson Virus
If you have a Windows virus, continue with the guide below.
If you have a Mac virus, please use our How to remove Ads on Mac guide.
If you have an Android virus, please use our Android Malware Removal guide.
If you have an iPhone virus, please use our iPhone Virus Removal guide
Infected users should do all they can to get rid of the Winlogson Trojan once they they realize they have been compromised. If you’re one of the unfortunate ones who doesn’t know where to begin, here are some simple instructions:
1. Click on the Start menu button and go to Control Panel >>> Programs and Features>>>Uninstall a Program.
2. Next, spend some time searching your computer for Winlogson and other unknown or suspicious-looking apps that have been installed without your knowledge or consent. If you need additional information to determine whether or not an application is harmful to your PC, pay attention to the name and manufacturer and do some research on them online.
3. When you’re finished, click the Uninstall button at the top of the window to remove Winlogson and any other potentially harmful apps.
Uninstalling the software may result in a pop-up warning like the one below:

Make sure you choose NO and complete the uninstallation process.
By following these instructions, you should be able to eliminate most of the threat from your computer. But remember that Trojans like Winlogson tend to place helper components and harmful files in different places across your computer’s system. This strategy helps the malware by making them more persistent and enabling it to complete the malicious agenda it has been assigned. As a result, we strongly recommend that you do not stop here but instead follow the more detailed manual Winlogson removal instructions provided below.

Restarting your computer numerous times over the course of this removal guide will be necessary if you are to remove all Winlogson-related files and components. That’s why, before you begin, we recommend that you save this page as a bookmark in your browser so you can easily return to it and complete all the steps. Or, try opening the tutorial on another device like your smartphone or tablet if you prefer that option.
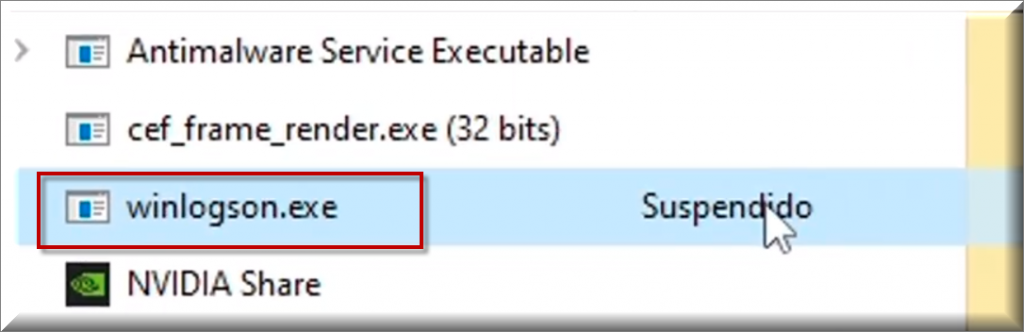
Now that you have bookmarked these instructions, the infected computer should be restarted in Safe Mode (click this link for details on how to do that). While in Safe Mode, you’ll be able to readily identify any suspicious behavior on your computer, as well as keep just the most critical processes and apps running.

WARNING! READ CAREFULLY BEFORE PROCEEDING!
*Source of claim SH can remove it.
Click on the Start menu button in Safe Mode, then type msconfig in the search area and press enter to launch System Configuration.
Next, select the Startup tab to see what programs are set to start running on startup:

If you notice a startup item with an odd name or an “Unknown” Manufacturer and you think that item is connected to Winlogson, click its checkbox to deactivate it. Then click OK to save your changes when you are finished.

*Source of claim SH can remove it.
When a computer is infected with Winlogson, one of the locations where malicious alterations are often seen is the Hosts file. The next step requires you to paste the following text into your Start menu search field and then hit Enter:
notepad %windir%/system32/Drivers/etc/hosts
Scroll through the content in the Hosts file until you find Localhost. If you’ve been hacked, you’ll see that under Localhost there are lots of IP addresses that appear suspicious:

Copy any questionable IPs from your file and post them in the comments. We’ll have a look at them and give you some advice on what to do next.

After you’ve uninstalled any malicious programs, disabled any risky startup entries and background processes, and checked your hosts file for hacking indicators, start your Registry Editor (CTRL+R, then type regedit and press Enter) and look for items that Winlogson has added to the registry.
Once the Editor has opened, use CTRL and F to find the Trojan’s name by typing it in the Find dialog box. After that, click Find Next and go through the results, removing anything you are sure that belongs to the infection or matches the Trojan’s name. Pay attention to any file or folder on your computer with a strange name that cannot be attributed to any genuine software currently running on your machine.
You can also use the left panel of the Registry Editor to manually check the content of each of these three locations:
- HKEY_CURRENT_USER—-Software—–Random Directory.
- HKEY_CURRENT_USER—-Software—Microsoft—-Windows—CurrentVersion—Run– Random.
- HKEY_CURRENT_USER—-Software—Microsoft—Internet Explorer—-Main—- Random.
If you’re not sure whether a file or a folder is connected to the infection, don’t delete it or make any changes to the registry on your own since you might seriously damage your operating system. Instead, use the free online virus scanner or the professional Winlogson removal software, links to both of which can be found on this page.

Leave a Comment