Woody RAT
Woody RAT is a very dangerous Trojan horse infection that can attack your computer without your knowledge and can lead to serious issues with your system, your data and your privacy. Threats like Woody RAT typically try to hide deep in the infected machine in order to freely initiate different malicious activities mostly aimed at weakening its security.
Woody RAT may create security holes and disable the existing security programs in order to avoid being removed and also make backdoor for additional malware like ransomware and spyware. In addition, the Trojan may mess with the system’s resources and exploit them for criminal purposes, in this way causing the OS to become unresponsive and crash or freeze. Such malware may also delete important files that you store on your hard drives and corrupt your software, thus making it unusable.
How to safely remove Woody RAT and all of its traces from your system
Dealing with Trojan-based infections can oftentimes be very challenging. This is because, unlike most of the other pieces of malware, these threats rarely show any visible symptoms of their presence and typically hide deep in the system by mimicking normal system files and processes. That’s why, in order to detect and remove Woody RAT and all the files associated with it, you may need to go through different removal steps and to navigate to various system locations until you reach the actual malware-related data. In order to help you with this task, below we have created a detailed removal guide that you can use.
Additionally, we have included a professional removal tool in it that can scan your entire PC for hidden malware. The manual removal process, however, may require you to have some technical experience because if you delete something unrelated to the malware by mistake, you may end up corrupting your OS. That’s why it is better to use the steps in a combination with the automatic removal tool as it can detect the actual malicious files and help you delete them.
You may not be able to perform any task smoothly on your computer if a threat of this type is hidden inside the system. That’s why the sooner you remove Woody RAT, the better. Unfortunately, like most Trojans like Altruistics, Weather Zero, this one can sneak inside your PC without any symptoms and the carriers of the infection could be all sorts of commonly encountered forms of web content. The largest number of contaminations usually happens as a result of users clicking on spam messages and infected email attachments.
However, more often than not, threats like this one also spread through infected software installers, free bundles, torrents, free download links, “you won a prize” messages, suspicious websites and more. That’s why you have to be very careful with the content you interact with and stick to safe web locations as much as possible. Fake ads and misleading links could also be carriers of a Trojan like Woody RAT and for this reason, it is advisable to avoid clicking on everything that pops up on your screen and to only visit sites of reputed developers if you want to download and install something.
SUMMARY:
| Name | Woody RAT |
| Type | Trojan |
| Danger Level | High (Trojans are often used as a backdoor for Ransomware) |
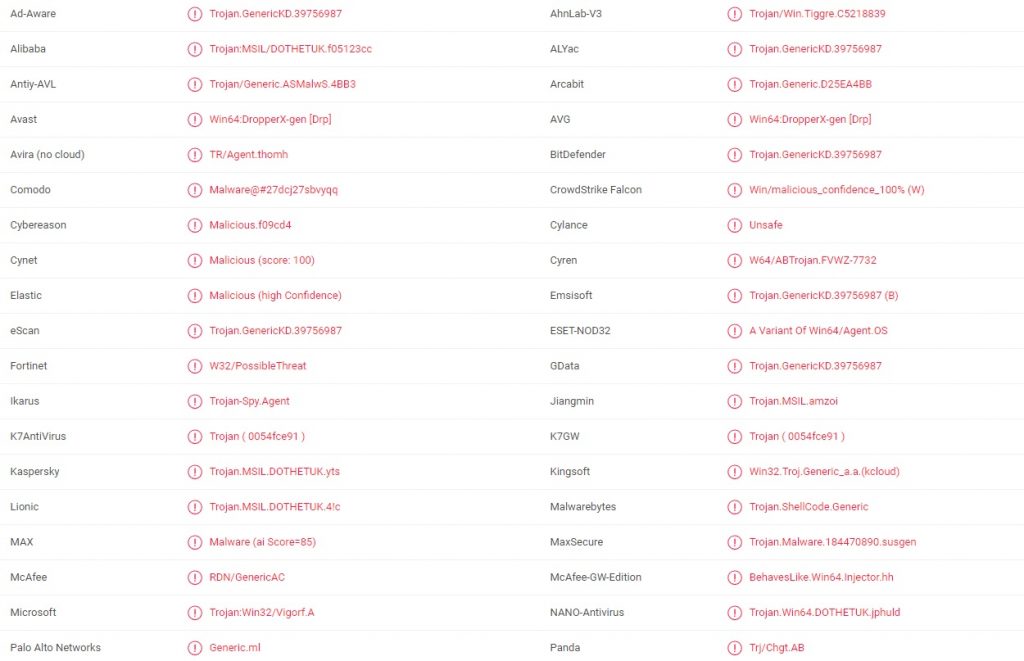
| Detection Tool |
Remove Woody RAT Malware
If you have a Windows virus, continue with the guide below.
If you have a Mac virus, please use our How to remove Ads on Mac guide.
If you have an Android virus, please use our Android Malware Removal guide.
If you have an iPhone virus, please use our iPhone Virus Removal guide

Some of the steps will likely require you to exit the page. Bookmark it for later reference.
Reboot in Safe Mode (use this guide if you don’t know how to do it).

WARNING! READ CAREFULLY BEFORE PROCEEDING!
Press CTRL + SHIFT + ESC at the same time and go to the Processes Tab. Try to determine which processes are dangerous.

Right click on each of them and select Open File Location. Then scan the files with our free online virus scanner:

After you open their folder, end the processes that are infected, then delete their folders.
Note: If you are sure something is part of the infection – delete it, even if the scanner doesn’t flag it. No anti-virus program can detect all infections.

Hold together the Start Key and R. Type appwiz.cpl –> OK.

You are now in the Control Panel. Look for suspicious entries. Uninstall it/them. If you see a screen like this when you click Uninstall, choose NO:


Type msconfig in the search field and hit enter. A window will pop-up:

Startup —> Uncheck entries that have “Unknown” as Manufacturer or otherwise look suspicious.
- Remember this step – if you have reason to believe a bigger threat (like ransomware) is on your PC, check everything here.
Hold the Start Key and R – copy + paste the following and click OK:
notepad %windir%/system32/Drivers/etc/hosts
A new file will open. If you are hacked, there will be a bunch of other IPs connected to you at the bottom. Look at the image below:

If there are suspicious IPs below “Localhost” – write to us in the comments.

Type Regedit in the windows search field and press Enter.
Once inside, press CTRL and F together and type the virus’s Name. Right click and delete any entries you find with a similar name. If they don’t show up this way, go manually to these directories and delete/uninstall them:
- HKEY_CURRENT_USER—-Software—–Random Directory. It could be any one of them – ask us if you can’t discern which ones are malicious.
HKEY_CURRENT_USER—-Software—Microsoft—-Windows—CurrentVersion—Run– Random
HKEY_CURRENT_USER—-Software—Microsoft—Internet Explorer—-Main—- Random
If the guide doesn’t help, download the anti-virus program we recommended or try our free online virus scanner. Also, you can always ask us in the comments for help!

Leave a Comment