Wpad.dat
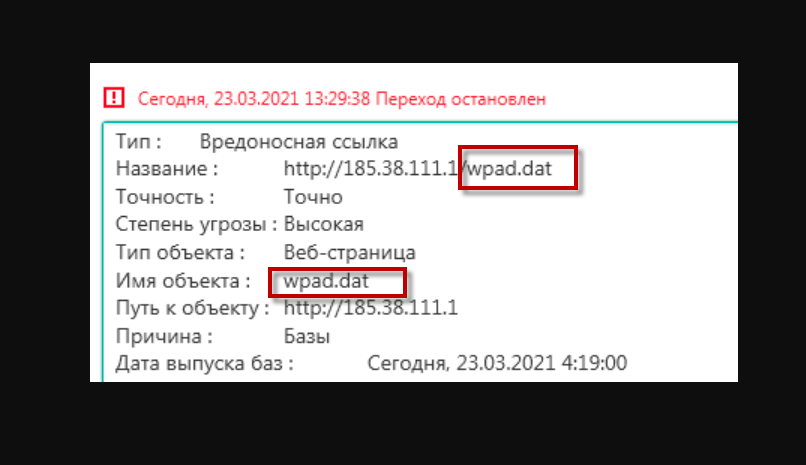
If you landed on this page, then you most probably have been infected with Wpad.dat Virus – a nasty Trojan horse, which has recently been reported as one of the latest online threats. Security experts classify Trojans as one of the most harmful types of malware one could encounter, therefore being infected with Wpad.dat Virus, you should really remove it from your machine as soon as possible.
The Wpad.dat Virus
But what exactly can this Trojan do and how to effectively clean your system from it? This is what we are going to cover here, so make sure you read the information below to gain a better understanding of this malware. Then, you can proceed to the special removal guide we have prepared so you can get rid of the infection.
The Wpad.dat Virus
Trojan horses are fearful online threats and so is the Wpad.dat Virus – one of the latest representatives of this malicious family. It has been created by criminal hackers, who can use it to perform almost unlimited destructive deeds to the users and their machines. The Wpad.dat Virus can usually infect you if you click on some fake ads like the intrusive pop-ups and banners you come across, torrents, shareware platforms, videos, illegal software, spam emails, and attachments.
What makes it different than the rest of the online threats and computer viruses is it’s the way it invades your PC and then harms it. A Trojan horse like this one usually tries to remain unnoticed for as long as possible. This means that there is a great chance that you may not realize that such a threat has compromised your machine until the very end where their computer has already been damaged. That’s why, most security experts, including our team, would advise you to use good antivirus software to detect such threats on time. Make it a habit of scanning your system frequently. Also, ensure that you are getting the latest updates and virus definitions. This will help your antivirus identify even the latest Trojans and harmful threats.
What can happen to your machine if you’ve been infected with Wpad.dat Virus?
Frankly speaking, no one can tell you exactly what kind of damage a Trojan horse can do. This is one of its most frightening aspects. A threat like Wpad.dat Virus could be used by the hackers for a number of malicious activities. Here, we will point out just some of the most common harmful actions to give you an idea about the capabilities of the threat on your machine.
- Changes to your Wpad.dat configuration settings – lan and otherwise.
- Severe system destruction and malfunction. The criminals may use the Trojan to create chaos on your PC, crash your system, take control over it or turn it into a bot. This way, they can easily involve it into some illegal activities like the virus and spam distribution or use its resources for their criminal deeds.
- Data and identity theft. With the help of a Trojan, the hackers may easily compromise your entire machine and all the information on it. This way, they can have access to personal information, sensitive details about you, your family, your health condition, work, projects and various personal details. They may also gain access to your online accounts and profiles, steal your identity and commit various crimes on your behalf. Isn’t this quite frightening?
- Keylogging and money theft. The Trojan can also be used to help hackers to record everything you type on your keyboard and then easily steal your credit or debit card numbers, your passwords and online banking details.
- Spying on you. A threat like Wpad.dat Virus could heavily compromise your personal life and privacy as well. The hackers may use it to spy on your professional or personal life with the idea to collect some private or confidential data, abuse you physically and mentally or blackmail you.
- Infecting you with other viruses. A very popular way to deliver another virus or a threat like Ransomware on the user’s machine is a Trojan horse. Due to its tricky nature, a threat like Wpad.dat Virus can help any malware easily sneak inside the PC undetected.
- The hackers may just have fun with your compromised PC. You never know how sick the mind of the criminal hackers is. Sometimes, they may simply want to entertain themselves by formatting your disks, deleting your data, destroying certain files, making modifications to your system or cracking the entire PC.
These are just some of the nasty things that may happen, and there are surely even more dreadful things that a Trojan could be used for. However, even this would be enough for you to understand the harmfulness of the infection and take immediate action to remove it. The guide below can help you do that, so you just make sure you closely follow the instructions to effectively get rid of the infection.
SUMMARY:
| Name | Wpad.dat Virus |
| Type | Trojan |
| Detection Tool |
Remove Wpad.dat Virus
You are dealing with a malware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to clean up and reset your browser to its original settings without the malware returning.
You can find the removal guide here.
For mobile devices refer to these guides instead: Android, iPhone

Leave a Comment