The “You got recorded” Email
The “You got recorded” email is a spoof scam that relies on the users being scared. Its goal is to make you believe you are infected while at the same time the “you got recorded” email is the product of nothing more but a hacked database.
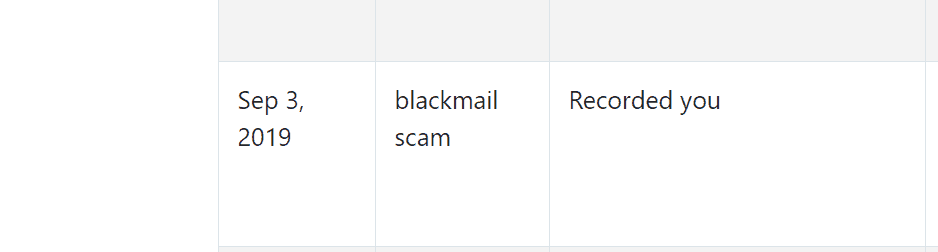
An example of a scam submitted with the “you got recorded” email.
A malicious Trojan Horse designed to perform various harmful activities on the user’s computer has recently been reported to our “How to remove” team. The threat goes under the name of “You got recorded” and is rapidly spreading across the web with the help of different legitimate-looking transmitters. A specific characteristic of most new Trojans is their ability to mimic completely legitimate files, ads, emails and messages and to easily mislead the web users about their real purpose and nature. In many cases, once such threats find their way inside the computer, they mimic regular system processes and hide deep in the OS without showing any symptoms of their presence. For this reason, we advise the users who think that they might have been infected with “You got recorded” to check their computer by scanning the entire system with a trusted security software tool and remove anything that is detected as a threat. Otherwise, if not detected and removed on time, the Trojan can work undisturbed and monitor your Internet activity, steal your personal information, and do many other nasty things. With this in mind, in the next lines, we have prepared a detailed removal guide with step-by-step removal instructions, as well as a professional scanner for quick and effective Trojan elimination.
How dangerous can a Trojan like “You got recorded” be?
Most users are unaware of the damage that Trojan Horses such as “You got recorded” may cause. However, it is important to mention that these threats are some of the most unpredictable forms of malware because they can be programmed to perform different harmful activities, one after the other. On top of that, thanks to using camouflage, the Trojans rarely show any visible symptoms while operating and it may take weeks or even months in some cases for the victims to realize that they have been compromised. After infecting the system without the users’ knowledge, those threats hide in the background and launch various activities that are considered extremely malicious. According to computer specialists, the infection can put your security at a serious risk by doing some of the following:
- Exploiting your system’s resources for illegal cryptocurrency mining or spam distribution;
- Recording your keystrokes and mouse movements with the goal of obtaining login and password credentials;
- Providing access to the infected system to the hackers and allowing them to install more malicious software in your computer.
- Turning the computer into a bot and using it for distribution of viruses, spam, and malware like Ransomware or Spyware.
This is just to give you an idea of what could possibly happen if you have a Trojan like “You got recorded” on your computer. However, the harmful abilities of this malware are not limited to the activities above, which means that you may also experience another form of attack, which may not be mentioned here.
Remove “You got recorded” as soon as possible.
With all that we said above, we believe that it is clear why it is important to quickly detect and eliminate the infection from the system. To help you with this uneasy task, below we have prepared a detailed Removal Guide with manual instructions and a professional removal tool for an in-depth system check.
SUMMARY:
| Name | “You got recorded” |
| Type | Trojan |
| Detection Tool |
Remove “You got recorded”
Search Marquis is a high-profile hijacker – you might want to see if you’re not infected with it as well.
You can find the removal guide here.

Leave a Comment