Zinda
Zinda is a type of malware that falls into the ransomware cryptovirus category. Zinda applies a sophisticated encryption algorithm to the files stored on its victims’ computers in order to prevent anyone from accessing them. Zinda, thus, gains leverage for the hackers behind it to blackmail the victim users.
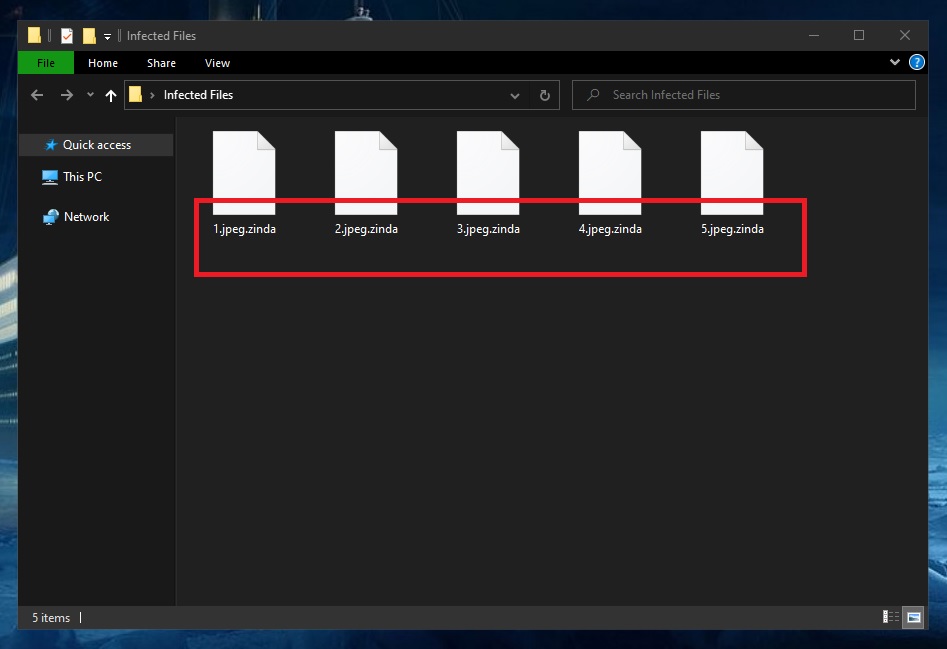
The Zinda ransomware encrypted files
This is an age-old extortion scheme in which the cybercriminals hope to make money at the expense of innocent and unsuspecting users. They deny them access to their (often very important) information and then promise to restore said access in exchange for a rather hefty amount of money. Access is typically restored with the help of a so-called decryption key, which is unique in every instance of infection. And that is where things can often go south, which is why opting for the ransom payment will not always guarantee a successful solution to this problem.
For this reason, we generally recommend trying to explore alternative file recovery options. In fact, after you have followed the instructions in the removal guide we have compiled for you just below the current post, you will find a list of such alternatives. But we cannot stress enough how important it is to first delete Zinda from your system. Failing to do this will only result in the subsequent encryption of whatever other files you manage to restore and/or new ones that you create on your PC.
The Zinda Ransomware
The Zinda ransomware is highly sophisticated malware that will oftentimes run completely unnoticed. In most cases the Zinda will not even provoke a response from your antivirus system.
This is, in part, what makes ransomware variants (.Zida, Moba) as dangerous as they are. However, sometimes users do stand a chance at detecting such viruses while they are still at work. This may occur as a result of a noticeable slowdown of the computer, which may prompt the affected user to check the Task Manager. In such instances, the ransomware virus will be visible as an unfamiliar process consuming the most system resources (i.e. RAM and CPU). Should this ever happen, you will have to immediately shutdown your computer to stop the virus in its tracks and prevent it from encrypting any more files.
But all of the above just goes to show how ineffective we are at handling ransomware attacks after they take place. It is way better to take the necessary precautions and disarm an attack beforehand. This can be done by regularly backing up your most important data and storing copies of it on a separate drive or cloud service.
The Zinda file distribution
Hackers generally rely on spam messages for the Zinda file distribution. In these cases, the Zinda file is usually included in an attachment or it may be downloaded after you click on an enclosed link.
In addition, Trojan horse viruses are often employed as backdoors in order to allow ransomware variants into the attacked computers. Therefore, it may be a good idea to run a system scan after you’ve deleted Zinda, just to be sure there’s no other malware on your PC.
SUMMARY:
| Name | Zinda |
| Type | Ransomware |
| Detection Tool |
Remove Zinda Ransomware
You are dealing with a ransomware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to decrypt and recover your encrypted files (if it is currently possible).
You can find the removal guide here.

Leave a Comment