*Source of claim SH can remove it
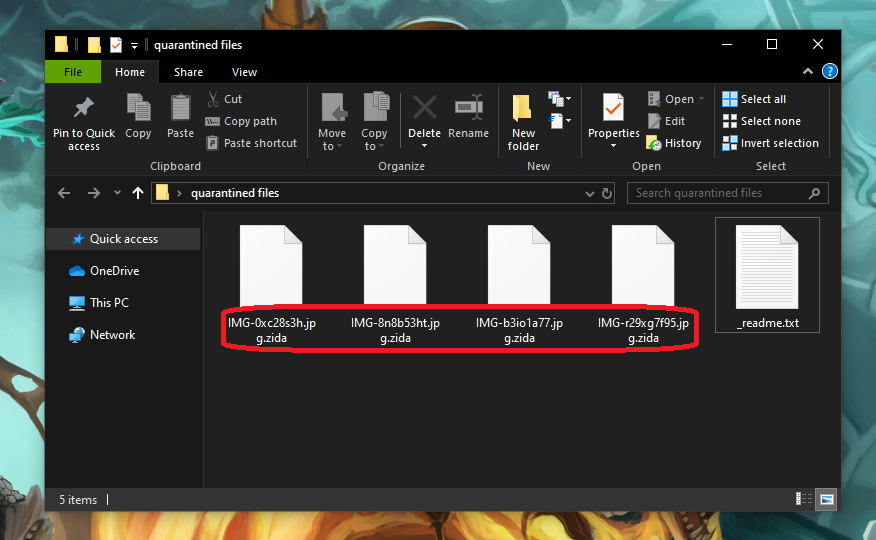
.Zida
.Zida is a ransomware-based piece of software that aims to encrypt digital files without the owner’s knowledge. After secretly applying its encryption code, .Zida generates a notification on the infected computer’s screen and blackmails the victim for a ransom.
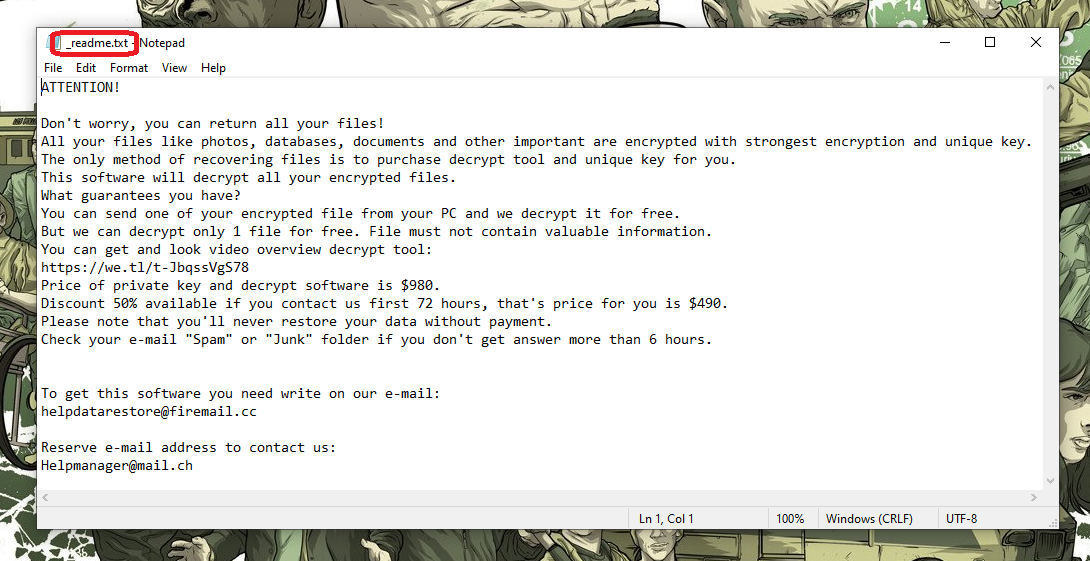
The programs that function in this way are generally known as ransomware cryptoviruses, because they are all specialized in encrypting data and blackmailing their victims for money. The .Zida Virus is a new representative of the ransomware family that acts in the same way and encrypts digital files without notice. The hackers behind it demand from the victims a fixed amount of money as a ransom for the decryption of their files. Typically, a .txt file, a pop-up or an on-screen banner is used to notify the users about the ransom demands, the deadline and the money transfer instructions. The victims who want to retrieve their files are normally advised by the hackers to adhere to the deadline and make the transaction without delay.
It is important not to jump into this, though, despite that the hackers behind the .Zida Virus are likely to promise you the sun and moon while trying to convince you to pay the money they are asking. The reason is the criminals simply can’t be trusted and even if you fulfill all of their demands, there is no guarantee that they will provide you with any of the file-recovery solutions that they may initially promise you. This is why we suggest that you first explore some other alternatives, such as those published in the removal guide below. And an even better idea is to concentrate your efforts on how to remove the ransomware so you can have a clean computer to restore your information on rather than pay some anonymous online crooks money.
The .Zida virus
The .Zida virus is an online cryptovirus used for extortion. The .Zida virus causes harm by encrypting personal or professional files and restricting access to them so that it can seek a ransom for their decryption.
This ransomware usually sneaks into the device with the aid of a Trojan horse or through security vulnerabilities that are unknown to the user. The fact that it does not show any visible symptoms or red flags while it is operating makes it very difficult to spot it. Furthermore, the method of encryption used by .Zida, Zwer, Moba does not cause real file damage, and so virtually nothing is able to cause an anti-virus response. This allows the malware to stay under the radar of the security program and to fulfill its mission without interruption.
The .Zida file encryption
The .Zida file encryption is a stealthy process that runs unapproved by the user and converts digital files into unreadable data bits. In some instances, however, the .Zida file encryption process may lead to a major system slowdown and an increased RAM and CPU usage.
Sadly, once the encryption cycle has come to an end, the victims have few options to reverse the code applied to the targeted files. Many users with personal backups will still recover from the attack quite quickly – only the malware has to be removed from the system and so that the copies of their files can be used. If you don’t have backups, you can try different alternative solutions, like the ones you will find below. Hopefully, you will have some success with them and can avoid the ransom payment.
SUMMARY:
| Name | .Zida |
| Type | Ransomware |
| Detection Tool |
*Source of claim SH can remove it
.Zida Virus Removal
You are dealing with a ransomware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to decrypt and recover your encrypted files (if it is currently possible).
You can find the removal guide here.

Leave a Comment