Zobm
Zobm is a cryptovirus aimed at blackmailing its victims for their money. To do this, Zobm renders the users’ files inaccessible through encryption and demands a ransom payment to provide a decryption key.
The Zobm Ransomware will start encrypting your files the moment after infiltrating your system.
What you need to know about such types of malware is that they will most likely run the file-encryption process in the background of the system without showing visible symptoms. Then, they will ask the victims whose data has been encrypted to pay a certain amount of money as a ransom. You will normally be informed about the attack after the file-encryption process has completed. That will happen via a ransom-requesting pop-up on your screen.
If you have been infected by Zobm and you are wondering how to remove it, you can find all the essential details about this Ransomware in the passages below. Ideally, you will be able to figure out a solution to your problem with the help of the instructions in the removal guide at the end of the article.
The Zobm virus
The Zobm virus is an infection of the Ransomware type that uses advanced encryption to prevent users from accessing their digital files. After the encryption code has been placed, the Zobm virus demands a ransom to be paid by the victims who want to receive a decryption key.
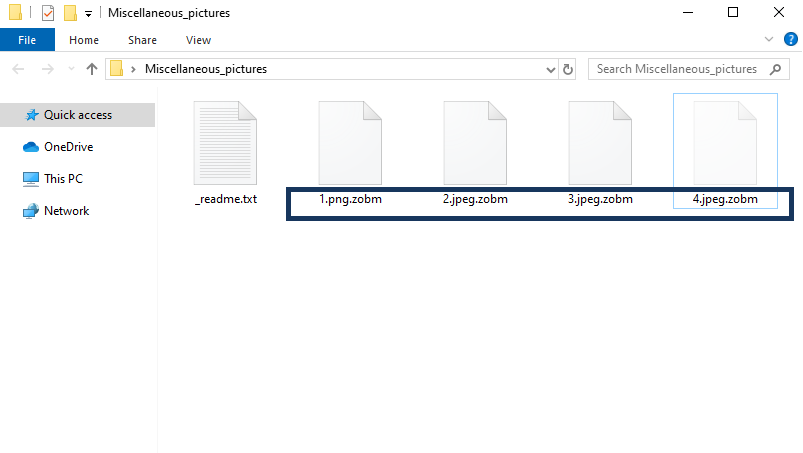
Ransomware versions like Zobm can target different file formats stored on your computer, make encrypted copies of them and then remove the original files leaving only the locked-up copies on the system. If the users want to restore their files and convert them back to normal, they would be prompted to make a payment to the hackers who stay behind the infection.
There is still no universal solution that can help the victims of Ransomware deal with such a situation. All that can be done is to consider each individual case and explore various options that could potentially help remove the Ransomware and restore some of the encrypted data. For instance, you can try our Removal Guide which is located at the end of this page. You could also ask for advice from a security expert of your choice. You could also try to install specialized software that could potentially handle the Ransomware’s attack. However, you have to be extremely careful with this since some hackers provide fake Ransomware-removal or Ransomware-decryptor tools and after downloading them on your device, you may end up dealing with two viruses. Therefore, what we suggest you do is select a reliable removal guide or removal software that will not trigger any additional problems. We have both of these down below.
The Zobm file encryption
The Zobm file encryption is an advanced crypto code that prevents digital files from being opened by any program. If a user wants to remove the Zobm file encryption, he is requested to pay a ransom in exchange for a decryption key.
All things considered, when it comes to Ransomware, prevention remains your best option. Simple tips like carefully selecting the content you are downloading on your device and staying away from sketchy web ads, redirect links, spam messages, and emails from unknown senders can greatly reduce the risk of catching an infection like Zobm. We also recommend that you install a reliable security program with Ransomware-protection features. No less important is the creation of backup copies of any digital information that is of any significant importance to you and storing it on external drives or on clouds.
SUMMARY:
| Name | Zobm |
| Type | Ransomware |
| Detection Tool |
Remove Zobm Ransomware
You are dealing with a ransomware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to decrypt and recover your encrypted files (if it is currently possible).
You can find the removal guide here.

Leave a Comment