.Blm
.Blm is a cyber threat that has been recognized as a ransomware cryptovirus. The creators of .Blm have been using it to secretly encrypt digital files inside the compromised computers and to demand ransom from the victims.
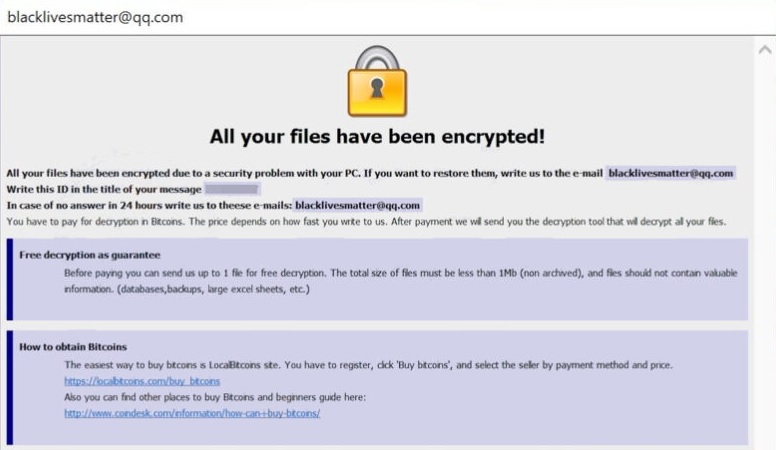
The .Blm Virus will show you this message once your files have been encrypted.
Ransomware is typically designed to either restrict access to the system’s screen or encrypt specific files stored in the computer’s hard drive. This splits the group of ransomware infections in two main subcategorise: ransomware screen-lockers and ransomware cryptoviruses. The threats that operate as screen-lockers and restrict access to the computer’s main screen are deemed the least sophisticated and less troublesome ransomware type. Normally, when the users get infected with these viruses, they are greeted by a full-screen banner or a pop-up message on their screen which prevents them from accessing the icons and the menu and basically stops them from operating with the infected device.
The hackers behind screen-locking ransomware infections typically promise to remove the banner if the victims agree to pay a certain amount of money as a ransom. Fortunately, in most cases, it is not too complicated to get around the screen-locking banner manually, without paying anything.
The case is different for ransomware cryptoviruses, such as .Blm, .Copa and .Lyli though. These viruses are commonly known to be some of the worst form of malware that can compromise your computer. They are very advanced and effective in secretly encrypting highly valuable digital information and keeping it inaccessible without any guarantees about its recovery.
The .Blm virus
The .Blm virus is a typical example of a cryptovirus ransomware that locks a list of valuable user data and does not allow accessing it. Like most viruses in this class, the .Blm virus encryption requires a special key to be decrypted and the victims are requested to pay a ransom for obtaining it.
However, the above-mentioned key is only held by the hacker who is liable for the attack and there is no guarantee that he will really send it to you even if you make the necessary ransom payment. That’s why before you act impulsively, you should ask yourself whether or not a shady and anonymous cyber offender should be trusted with your hard-earned money. The statistics shows that many users simply get tricked to pay the money and never hear from the hackers again, let alone to receive a decryption key.
The .Blm file
The .Blm file is a malicious code that would not show any visible signs of its presence on the computer until all the targeted user data becomes encrypted. This lack of symptoms helps the .Blm file to avoid detection and to complete its agenda without being interrupted.
If .Blm has currently locked your data, you might want to explore some of the alternate options that are available and try them out before transferring the ransom. For that, we have created a guide where we have included some suggestions on file recovery to help you get some of your data back. In addition to that, we also have included manual steps that explain how to remove .Blm and a link to a professional anti-malware tool, which could be helpful in the attempts to remove the cryptovirus from your computer.
SUMMARY:
| Name | .Blm |
| Type | Ransomware |
| Detection Tool |
.Blm Ransomware Removal
You are dealing with a ransomware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to decrypt and recover your encrypted files (if it is currently possible). You can find the removal guide here.

Leave a Comment