Contebrew
Contebrew is a Trojan horse virus that seeks to compromise different computers and to launch malicious activities in their background. The criminals behind Contebrew can use it for espionage, theft of personal data, banking fraud and more.
In this article, we will discuss the features of this Trojan infection and the possible methods that you can use to remove it. Contebrew is a new addition to the Trojan horse family and has recently affected many PC users. Some of them have asked our “How to remove” team for assistance in dealing with the threat, thus, we came up with this article and the removal guide at the end of this page.
If you have been infected with Contebrew , we advise you to carefully read the information that follows and check the removal instructions in the guide. Also, don’t forget to run a full scan of your computer with the professional removal tool on this page or some other reliable antimalware tool that you trust in order to detect and delete the infection quickly and safely.
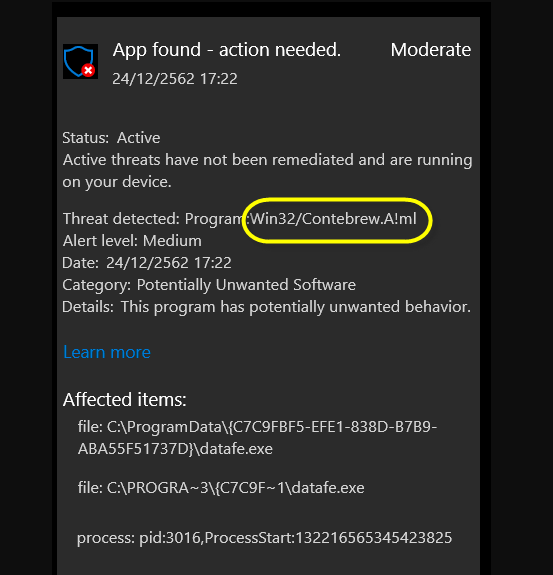
The most challenging thing when dealing with Trojans is their detection. These threats generally don’t show visible symptoms of their presence in the system, thus, web users can rarely detect them without the help of professional software. What is more, viruses like Contebrew can camouflage as regular system files and can mimic normal system processes when they operate in order to hide in the computer for longer and to make it harder to locate and remove them.
People who don’t know how to recognize the Trojan-related files may even delete vital system files and corrupt their OS in an attempt to remove the Trojan. That’s why it is not advisable to experiment with your malware-removal skills if you are not a professional. A much safer solution is to simply use a professional removal tool and avoid the risk of involuntarily corrupting your computer.
The Contebrew Virus
Normally, while it operate the Contebrew virus don’t show any red flags. Yet, if you are observant, there are some potential symptoms that may help you identify the presence of an infection like the Contebrew virus in your system.
For instance, be on the watch for frequent Blue Screen of Death (BSoD) crashes, programs freezing and unusual system errors. These may sometimes be linked to potentially malicious activity in the background of the system. Trojans may sometimes corrupt different files, including vital OS files or personal data that is stored on the hard drives. They may also make modifications in the system’s settings without asking for approval from the users. That’s why any unauthorized changes in the computer’s configurations, as well as your programs should also be carefully checked as they may be caused by hackers who remotely access the system through a Trojan.
As you can see, infections like Contebrew can be extremely dangerous because they can make numerous unauthorized changes to the system, exploit its resources and destroy any data stored there. What’s more, these threats can invite other viruses inside the computer, especially Ransomware and Spyware, which can cause even more damage.
That’s why it is important to remove the Trojan from your device before it manages to cause irreparable harm. The easiest way to do that is by running a full system check with a reliable antivirus or antimalware tool (like the one that you will find below). If you are still worried that even after you’ve scanned the computer the malware may still be hiding somewhere, make sure that you complete the steps in the Contebrew removal guide that we prepared for you.
SUMMARY:
| Name | Contebrew |
| Type | Trojan |
| Detection Tool |
Remove Contebrew Virus Trojan
You are dealing with a malware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to clean up and reset your browser to its original settings without the malware returning. You can find the removal guide here.
For mobile devices refer to these guides instead: Android, iPhone

Leave a Comment