*Ghsd is a variant of Stop/DJVU. Source of claim SH can remove it.
Ghsd
Ghsd falls into the cryptovirus subcategory of ransomware, which is undoubtedly one of the worst and one of the most advanced forms of malware and is usually quite difficult to handle. The way Ghsd works is it first infiltrates your machine, scans the hard drives and locates all personal data files that belong to certain file formats and encrypts them.
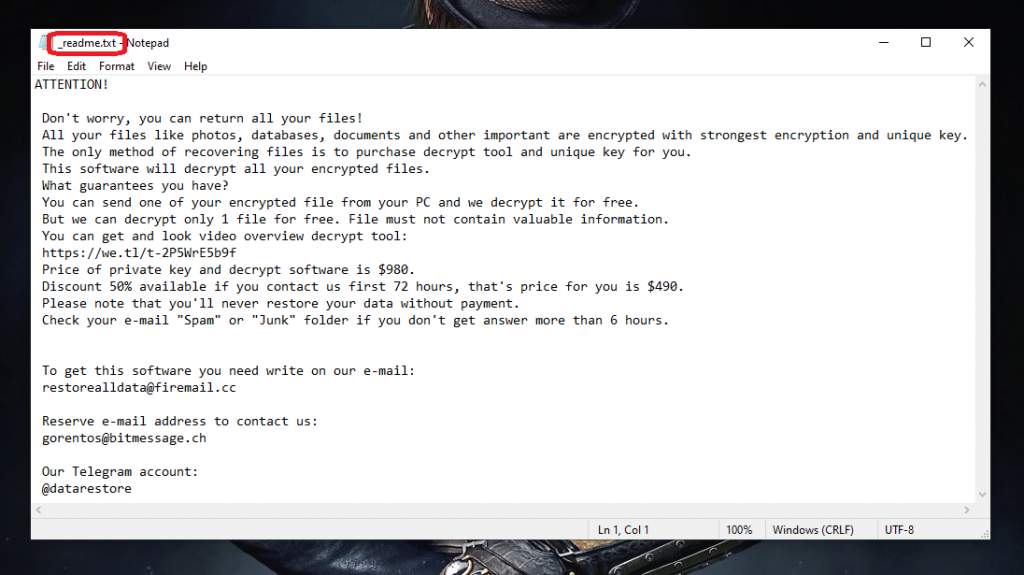
Usually the targeted file formats are ones that are commonly used by the users such as different text document formats, images, spreadsheets, videos, audio files and so on and so forth. Once all targeted files have been accounted for, the malicious cryptovirus goes on to encrypt all of them. The purpose of the encryption isn’t to harm the files in any way but to make them inaccessible for the user of the PC.
The idea is that once the user realizes that their data has been locked by the ransomware, they’d be forced to pay for the release of the files by making a ransom payment to the hackers who, in turn, promise to send the decryption key for the sealed files to the victim. A big problem here is that there can’t be any guarantees that this is how things would always go down should the malware victim pay the money. For all the user knows, they could get tricked into paying and then receive no decryption key for their files meaning that the money would have been utterly wasted.
This is one of the main concerns that security researchers have in mind when they advise the victims of ransomware should normally try to deal with the cryptovirus in some other way different from paying the money. Of course, there are also many instances where the hackers do indeed keep their promises and send the details needed for the unlocking of the files after the money has been received. Nonetheless, if there’s a way to remove the malware and recover the files without paying anything, one would understandably go for that option instead of sending their money to some anonymous Internet crooks.
The Ghsd virus
The Ghsd virus is one of the more recently released ransomware representatives. Therefore, the encryption used by the Ghsd virus is significantly more complex than that of earlier variants.
We already told you that paying the demanded ransom is not the best course of action as it won’t really guarantee that you’d actually retrieve your locked-up data. However, sadly, neither would trying any of the available alternatives. We understand that this might sound rather grim and we absolutely do not mean to discourage you. It is pretty much always better to try out all available alternative solutions and possible methods of dealing with a virus like Ghsd, Dkrf, Eiur or Lloo that do not include paying the ransom. However, we also do not wish to lie to you by telling you that what we offer as potential solutions would work in all cases.
Still, though, trying out the guide on this page will most likely help you remove the virus and should, at the very least, make your computer safe and clean once again so that any new files won’t also get encrypted by the Ghsd cryptovirus.
The .Ghsd file encryption
Once you remove the infection, the already locked files are likely to remain that way since the Ghsd file encryption doesn’t normally go away after the malware is removed. That is why there are separate steps you need to take in order to restore your data from the Ghsd file encryption.

As we said above, we can’t make any promises but trying the suggested solutions won’t cost you anything and so you will at least not be risking your money in the process of trying to recover your data.
Ransomware threats, though not the most commonly encountered undesirable programs, don’t seem to be going anywhere in the near future so you must at least learn how to stay away from them. The most important thing here is to be cautious with your online activities. If you see a shady-looking ad or you receive some suspicious spam-like e-mail or if some obscure download request pops up on your screen while browsing, be sure to avoid them as those are all common sources of unwanted and potentially hazardous programs. Something that can really help you against ransomware in particular is backing up the important files that are on your PC and placing their copies on safe locations that aren’t connected to your machine.
SUMMARY:
| Name | Ghsd |
| Type | Ransomware |
| Detection Tool |
*Ghsd is a variant of Stop/DJVU. Source of claim SH can remove it.
Remove Ghsd Ransomware

Following the steps in this removal guide to the letter is the most effective way to remove the Ghsd ransomware from your computer. As a first step, disable your computer’s Internet connection. This will prevent any malicious software that might be in the system from contacting its servers. Unplugging any USB and external storage devices connected to the infected PC is also recommended.
Restarting in Safe Mode is the next step that we suggest. If you need help with that, please follow the instructions provided in this link. After the system reboots, please return to this page and finish the remaining steps of the guide. Bookmarking this page in your browser will allow you to immediately access it after a system restart.

WARNING! READ CAREFULLY BEFORE PROCEEDING!
*Ghsd is a variant of Stop/DJVU. Source of claim SH can remove it.
Task Manager must be accessed as a next step. Use the Windows search bar to start the Task Manager by typing “task manager” and pressing Enter. Next, click on the Processes tab and sort the running processes by memory and CPU use. It is essential to scan the files associated with any processes that you think are related to the danger. In order to view these files, all you have to do is right-click on the suspicious process and choose Open File Location from the context menu.

To begin scanning, just drag & drop the contents of the folder into the scanner below:

If the scanner detects hazardous files on your machine, right-click the process and choose “End Process” first. After ending the suspicious process, remove all files marked as threats from the location where danger has been discovered.

Next, use the Windows key + R key combination to open a new Run window on the screen, and paste the following command in it, then press Enter:
notepad %windir%/system32/Drivers/etc/hosts
Once you do that, a new window with a file named Hosts will open on the screen. Look for Localhost in the file’s content. Please let us know if you discover any strange IP addresses under “Localhost” and we will reply to you on what to do if any of your IP addresses turn out to be harmful.

Ghsd files might also be found in System Configuration. To open System Configuration, type msconfig in the Windows search bar and press Enter. Check the “Startup” tab for suspicious items to see whether they are set to start automatically when the system boots.
Uncheck the boxes next to the startup items that are related to the malicious software. If you have any questions about the trustworthiness of a startup item, do some research on the internet beforehand in order to collect more information.

![]()
*Ghsd is a variant of Stop/DJVU. Source of claim SH can remove it.
The ability of ransomware to silently inject new malicious files into the system registry allows it to remain undetected for long periods of time. That’s why, if you want to get rid of Ghsd permanently, searching the registry for dangerous files is strongly recommended. To do that, type “Regedit” in the Windows search bar and hit Enter on your keyboard.
Using CTRL and F, you may save time and search the Registry Editor for malicious files more easily. Enter the name of the ransomware in the Find box and click on the Find Next button to begin the removal process.
Attention! Ransomware registry files may need computer skill and experience to delete. It’s important to make sure that no other registry entries are deleted throughout this operation. So, if you’re not certain that you can remove the infection on your own, using a virus removal program like the one on our site is highly recommended.
Files associated with the ransomware may be located in the following locations on an infected PC:
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
To access them, copy and paste them one by one in the Windows search bar and click Enter. After that, look for files and folders with random or strange-looking names (strange characters, symbols and numbers). You should not make any changes or removals to these files or directories unless you know for sure that they are linked to the infection. When you visit Temp, it might be a good idea to delete all temporary files stored there, as it’s probable that some of these temporary files may be related to the infection.
![]()
How to Decrypt Ghsd files
A Ransomware infection may be tough to cope with even for the most seasoned computer experts. That’s why, if you don’t have the necessary skills, it is best to rely on trusted software or a skillful professional rather than risking damaging your system even further. After running a comprehensive system check to ensure that your machine is clear of malware, you may safely proceed to any file-decryption methods that are available.
In order to determine which variant of ransomware has infected your computer, our first recommendation is to identify the encrypted files’ file extensions.
New Djvu Ransomware
STOP Djvu is a ransomware variant that has recently infected a large number of computers worldwide. The .Ghsd file extension is usually a sign that the file has been encrypted with this particular ransomware. A decryption application like the one provided at the following website may be able to help you recover some of your lost data if you’ve made sure your machine is virus-free:
https://www.emsisoft.com/ransomware-decryption-tools/stop-djvu
Before decrypting your files, however, make sure to read the decryptor’s license agreement and any other included instructions. It is important to note that this decryptor does not guarantee that all your files will be recovered, especially if they have been encoded using an unknown offline key or online encryption.
Use anti-virus software if the manual removal methods on this page aren’t sufficient to eliminate Ghsd entirely. Our free online virus scanner, may help you do a manual scan if you’re concerned about a particular file. If you have any questions or concerns about this guide’s removal instructions, please leave a comment below.

Leave a Comment