Hi.ru may expose your browser to redirects, ads, and persistent unwanted components. Install SpyHunter Pro to scan for risks, remove related threats, and enable real-time protection.
*Source of claim SH can remove it. Trial w/Credit card; image is for illustration; full terms.
Hi.ru
Hi.ru is a browser hijacker which is known for the continuous stream of pop up ads it will display on your computer. While the Hi.ru Virus is in your system, it will redirect your browser searches during each browsing session so it can show banners, pop-up ads and messages.
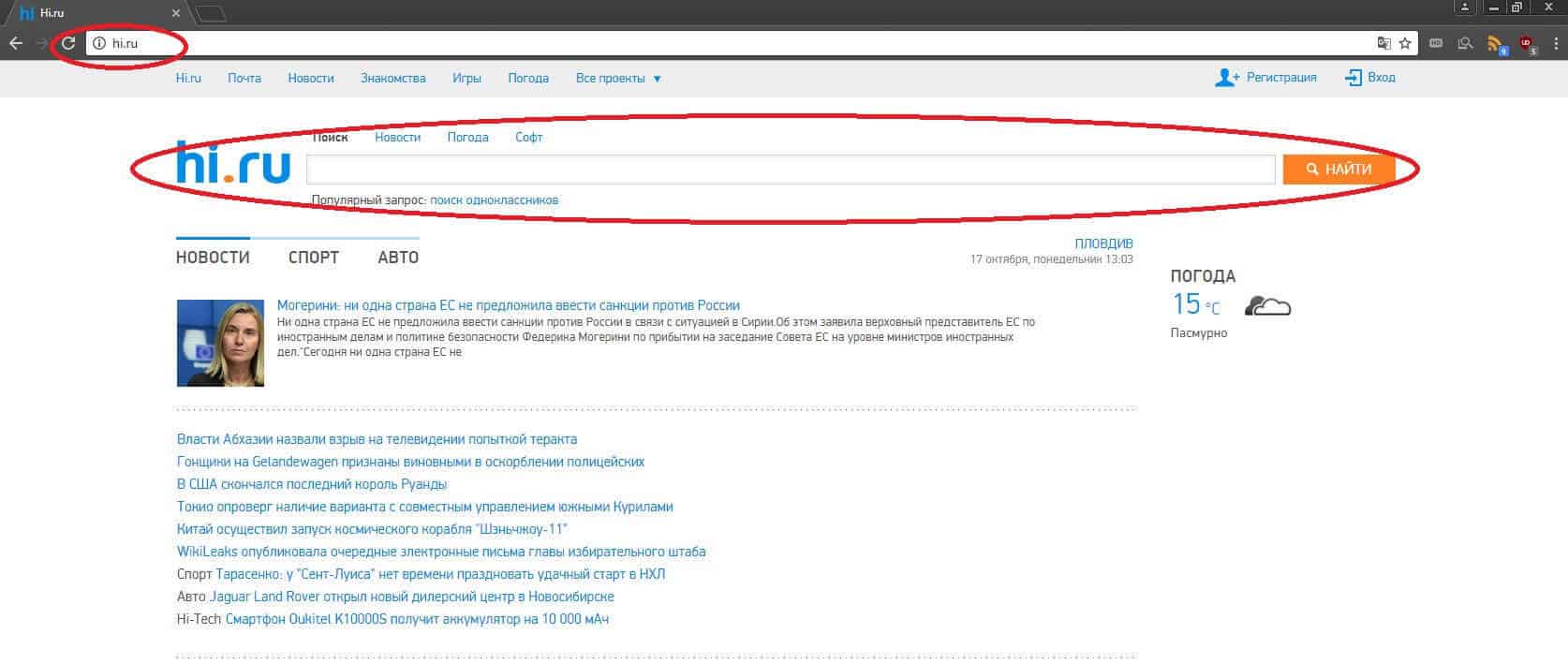
What could be more annoying than a browser hijacker that applies some sudden changes to your Chrome or Firefox browser settings? It is surely a disturbing experience. A new homepage and replaced search engine, a constant flow of search redirects, ads and pop-ups all over the screen – all this could be a result of the activity of such a program, and the one that we will discuss this time is called Hi.ru. If you are having a firsthand experience with this software, then here you may find some useful information about it and the possible ways to uninstall it. In the next lines, you are going to read about the its distribution and level of harmfulness as well as the effective steps you can take in order to remove it completely from your system.
A typical example of a potentially unwanted program is the Segurazo Antivirus.
Hi.ru is a type of ad-generating software which is specialized in hijacking your browser and manipulating it in order to display a huge amount of ads, banners, pop-ups, new tabs and all sorts of sponsored web pages and online advertisements. By doing this, the program ensures that the affected user is exposed to as many advertisements as possible and has no option but to click on them. Usually, the clicks are exactly what this software is created for, since they generate revenue for the developers through the famous Pay-Per-Click scheme. This is the reason why browser hijackers are so intrusive in their attempts to display different pages and popping notifications – they have simply been programmed this way. However, the ad-displaying activity may really be a great source of irritation to certain users, therefore some of them may wish to uninstall the program from their machines.
The good thing about browser hijackers is that they are not harmful. It is true that sometimes they may generate way too many advertisements and aggressively impose some undesired changes to your browser settings, which may cause a significant online disturbance, but they are far away from threats like viruses, Trojans, Ransomware or other malicious infections. Programs like this have no malicious abilities typical for the malware, nor can they destroy your system if you keep them there. However, there are some annoying side effects that may be caused due to Hi.ru’s activities on your computer. Apart from messing with your homepage and search engine, this browser hijacker may redirect most of your searches to various promotional websites full of nagging ads, pop-ups and banners. It may also track your online activity in its attempts to match its advertisements with your searches. This is something that some users may find disturbing, especially when it is not really clear where the collected data may go later. Another reason to consider removing the browser hijacker is the significant slowdown it may cause to your browser and your system. It may take forever for the affected browser to load the pages you want and it is not uncommon that you may land on some unknown web locations or insecure websites.
To have ended up with a browser hijacker on your computer, you have probably downloaded and installed it along with some other software. This is a common distribution method known as software bundle where such ad-generating components and other bloatware is included in software installers of mostly free or new and attractive programs. You may come across such bundles if you often download software from freeware platforms, torrent sites, some direct downloads from the web, different installation managers or even spam emails. Sometimes even paid software, games installers or new applications may contain some additional software like Hi.ru, the aim of which is to get installed too and generate income through the Pay-Per-Click scheme. Something very useful that you may wish to know is how to prevent such additional software from getting installed. For that, you are advised to click on the so-called “advanced”, or in some cases “custom” installation option, when running the setup of a new program on your computer. This will open a menu where you can see and manually disable any programs you may not wish to have installed. Skipping that, however, may result in installing the whole bundle “as is” and eventually ending up with some browser hijacker like Hi.ru or in some rare cases even virus threats like Trojans or Ransomware.
Removing the browser hijacker is not that tricky if you closely follow the instructions below. The removal guide we’ve prepared contains all the steps that will help you find and delete the hijacker. However, it is a good idea to double check your system with the professional Hi.ru removal tool before deleting anything, because there is a chance you might inadvertently delete some system files, especially if you have not cleaned your system this way before. So, check it out and let us know about the outcome in the comments below.
SUMMARY:
Hi.ru Virus Removal
You are dealing with a malware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to clean up and reset your browser to its original settings without the malware returning.
You can find the removal guide here.
For mobile devices refer to these guides instead: Android , iPhone


Leave a Reply