Drive.bat
Drive.bat is a malicious program from the Trojan horse class that is typically used for data destruction. If Drive.bat has nested inside your computer, it most probably will make your information useless by damaging it.

The Drive.bat Virus
The font.bat virus
The font.bat virus is a file hat is normally registered as a new system driver service named “MsNet”. the font.bat virus typically has a display name of “MsNet Service” and is started automatically during system startup.
If your computer has been infected by the nasty Drive.bat, we are here to help you get rid of it as well as regain access to your files that this virus has hidden from you. However, before checking out our Drive.bat Removal guide, we advise you to read everything that this article has to offer if you want to successfully eliminate the malware without allowing it to cause any more trouble. Bear in mind that this Trojan type of virus is quite devious and tricky to fully eliminate. There aren’t any actual symptoms of the infection and sometimes you might think that you’ve succeeded in removing it when in reality it is still on your PC. It is also known to spread very quickly and without being noticed.
The windows batch file virus
The windows batch file virus is a malicious piece of software that can cause a lot of trouble to your files. Users who have the windows batch file virus will typically detect that their files have changed into shortcuts and out of the blue, there is a presence of a windows batch file on their drive.
As you might have already found out for yourself, the virus targets your USB devices and seemingly removes the files that are on them. Do not be worried though, since your files are merely hidden so that you cannot access them. What usually happens when you have the Drive.bat on your PC is that once you connect a USB device to the computer and try to access its contents, instead of folders and files, you will only see a single shortcut file that has the same icon and/or name as your USB drive. All content that has been on the device has been moved to a hidden folder that you cannot access unless the malware is removed from your computer. Your data normally does not actually get harmed or deleted by the Drive.bat, so as soon as you deal with the infection, things should be back to normal.
Stay away from the shortcut
Under no circumstances should you attempt to open the virus-created shortcut – it will not lead you to your files. Instead, opening the said shortcut would result into the virus spreading throughout your PC (if it hasn’t done that already) and also infecting all other USB devices that you have connected or might connect to. This Drive.bat Virus is known to target all types of USB devices – flash drives, SD cards, external hard-drives, mp3 players, and so on. If you have already double-clicked on it, then you will have to scan your whole system for the virus. Our guide will help you with that. If you strictly follow the steps and complete every single one of them, most of the time the infection should be gone. However, know that Trojan horse viruses like the one that’s currently on your PC can be used as backdoors into your system. Thus, the Drive.bat might also infect your computer with more malware. That is why we also advise you to get a reliable scanner tool – this will help you detect any other malicious software that the Drive.bat might have infected your computer with.
What is “windows cannot find drive.bat” error?
“Windows cannot find drive.bat” is an error that appears when users try to access files that have been modified. The “windows cannot find drive.bat” error could be a sign of a virus infection that has hidden the user’s files.
This particular Trojan seems to be very widely spread and a lot of users have already gotten infected by it. That is why you need to have a good understanding of how it gets onto people’s computers so that you can prevent it from attacking your system again.
- Trojans like “Are you the one in the video”, Wup.exe is often spread via sketchy online ads within websites with shady content. Therefore, make sure that you stay away from any sketchy sites/pages that could potentially be used for spreading the malware. Keep in mind that even though the virus we are currently focusing on is quite nasty, handling it is still manageable in the majority of cases. However, there are other forms of malicious software, such as the infamous Ransomware that can also be distributed via such shady and potentially illegal sites and if you land one of those, there’s a high chance that you’d be unable to deal with it.
- Another extremely common method for spreading Trojan Horses is via spam emails/text messages. Always take a second look at new letters in your inbox before opening them. If anything looks like spam, be sure to delete it without interacting with any of its contents – better safe than sorry!
- A very simple, but also very important piece of advice, is to make sure that files cannot be automatically downloaded on your machine without you giving your permission beforehand. This is done through your browser settings, so make sure to do it.
- One more very effective technique for spreading the Drive.bat is the so-called file-bundling. This is when a piece of software is put inside the installer of another program. Therefore, always make sure to check the setup wizard of programs you are about to install, to see if there is anything added. If there are any added applications, make sure to leave them out if they appear shady and potentially harmful. If you are given the option to use a Custom/Advanced installation menu, make sure to go for that, since this is usually where the added content can be seen.
- Last but not least, never open any obscure files that have gotten on your PC and you do not know what they are, especially if they are executables. If you cannot verify that a file is safe, deleting it is always the best option.
SUMMARY:
| Name | Drive.bat |
| Type | Trojan |
| Detection Tool |
How to Remove The Drive.bat Virus
To remove the Drive.bat Virus, you need to follow a sequence of removal steps. The manual removal guide below contains instructions on how to remove the Drive.bat Virus but you can use a professional removal tool if you want to save your time and efforts.
![]() Preparation
Preparation
Before you start with the actual removal of the Drive.bat Virus, please do this preparation:
- Bookmark this page so you can get back to it because there are steps in this guide that will ask you to exit your browser.
- Reboot your computer in Safe Mode.
![]() Determine the dangerious processes
Determine the dangerious processes
WARNING! READ CAREFULLY BEFORE PROCEEDING!
The actual removal of the Drive.bat Virus starts with detecting its malicious processes in the Task Manager.
Open the Task Manager quickly with the help of the CTRL + SHIFT + ESC key combinations from your keyboard.
Once the Task Manager dialog opens, select the Processes Tab from the tabs that are available.
A list of active processes will appear where you will have to figure out which of them are dangerous or could be linked to the Drive.bat Virus.

Once you detect something that is malicious, right-click on it and then click on Open File Location. Then use our virus scanner to scan the files found in that location.

After you open the processes’ folder and check the files there, go to the Task Manager and terminate the infected processes by right-clicking and choosing the “End process” option. Then delete their folders.
Note: There might be files that may not be flagged by the scanner as threats. However, if you strongly belive that they are linked to the infection don’t leave them on the computer and delete them.
![]() Restore your files and delete the virus’s shortcut.
Restore your files and delete the virus’s shortcut.
With the help of the guidelines in this step, you may restore your files and hopefully delete the shortcut that the Drive.bat Virus has created in your computer. Please consider though, that other viruses might have sneaked inside the system during the time that the Drive.bat Virus has been active and the instructions shown here won’t be able to help you remove them as well. That’s why, to check your system and clean it from any other potential threats, your best option is to use a professional scanner or an automatic malware removal tool such as those that you can find on this page.
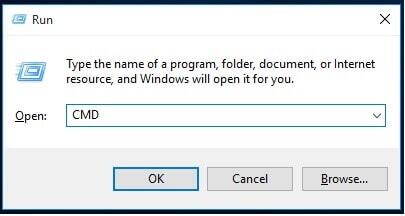
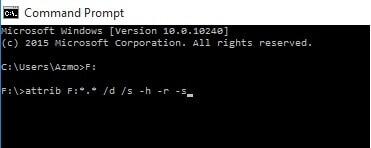
Open the Command Prompt panel by holding the Start and the R keys on your keyboard and typing cmd in the text field of the Run box. Don’t forget to hit the Enter to execute the command.
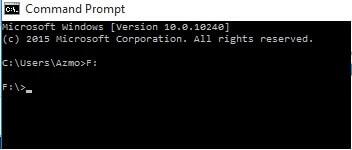
In the Command Prompt panel, find My Computer and see the name that Windows has given to your drive.
In the case that we use as an example it is drive F.
Next, in the Command Prompt window that you opened, type the letter that is corresponding to your drive followed by semi-columns.
In our case it should look like this F:
Next, press the Enter key of your keyboard.
A new window will appear on your screen and it should look like this F:\>
After that, type the following: attrib F:*.* /d /s -h -r -s . (Important! Replace F: with the name of your own drive)
After that, hit the Enter key. Once you are done, all of your files should now be recovered and the Drive.bat should be removed from this drive.
The instructions described above should be applied for all drives that have been affected. Just make sure you change the F letter from our example with the correct letter that corresponds to the drive you are currently cleaning!
- ATTENTION! It is quite possible that you might have been compromised by a virus that might be preparing itself to deliver a ransomware inside your system. Ransomware threats normally aim at encrypting your personal files and demanding money in exchange for a decryption key. Typically, the primary source of such threats is Trojans and the Drive.bat threat gets delivered precisely via Trojans. That’s why it is important not only to remove Drive.bat, but also to check your computer for other malware by using a professional scanner.
Step 3B (This is an optional step in case the instructions above don’t work in your case)
If you can still see the Drive.bat on your drive and the instructions above failed to help you, do the following:
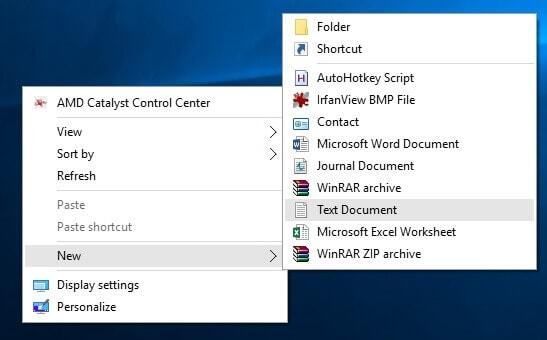
- Create a new .txt file (Right-click with your mouse somewhere on your desktop, then go to New and select Text Document).
- Open the new file via NotePad.
- Next, carefully copy and paste the following instructions in the NotePad file:
@echo off attrib -h -s -r -a /s /d F:*.* attrib -h -s -r -a /s /d F:*.* attrib -h -s -r -a /s /d F:*.* @echo complete - Just as in the example above, F: is just a placeholder! Make sure that you replace F with the appropriate letter for the Drive on your computer!
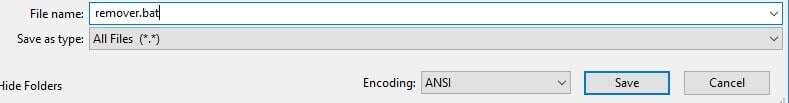
- Next, still in the NotePad, go to Files (upper left), select Save As… and change the save as type to “All files(*.*)” from “Text documents”.
- Rename the file to cleaner.bat and save it on your desktop.
- Next, close NotePad and open the newly created file.
- All Drive.bates from your drive should now be removed and your data should be recovered!
- If you have other drives that have been affected, repeat these instructions, just don’t forget to change the letter of the respective drive.
![]() Remove the virus’s traces
Remove the virus’s traces
To remove the traces of the virus from your system, you still need to dig a little deeper into the settings. For that, open the Run dialog box by pressing the Start Key and R key from your keyboard together. Then, in the Run dialog that pops-up, type appwiz.cpl and hit the Enter button.

This command will lead you to the Control Panel. Once you get there, check for any entries that look suspicious and might be linked to the Drive.bat Virus. It is not necessarily that they have the same name, that’s why you have to carefully check for questionable or unfamiliar items. If you detect any, uninstall it/them. A pop-up like this one may appear when you try to Uninstall the items. If this happens, click “No”.

![]() Remove any Startup entries
Remove any Startup entries
Next, you have to enter the System Configuration settings and remove any Startup entries that might be added by the virus there. In order to do that, type msconfig in the search field and press the Enter button. A window like this one will pop-up on your screen where you will have to tap on the Startup tab:

Once you see the content from the Startup tab, look through the list and remove the checkmark before any entries that have a Manufacturer that is unknown or appear to be questionable.
Attention! If you have a suspicion that your computer might have been hacked or there might be some other malware (like a Ransomware) inside the system, then follow these steps:
Open the Run dialog (Start+R keys) and copy this inside the text box:
notepad %windir%/system32/Drivers/etc/hosts
Hit the Enter button and this will open the Hosts file of your computer. It should look like this:

Head to the “Localhost” section and check if there are some strange IP addresses under that section. Normally, there shouldn’t be any, but if you detect some, then your computer might be hacked. If this is the case, please write to us in the comments below this article so we can advise you further.
![]() Remove the Drive.bat Virus entries from the Registry Editor
Remove the Drive.bat Virus entries from the Registry Editor
You are not done yet with the removal of the Drive.bat Virus before you remove its entries from the Registry Editor. That’s why, in order to eliminate all traces, head to the Register Editor (Type Regedit in the windows search field and hit Enter). Then, when the Register opens, search for the virus by its name (press the CTRL and F buttons on your keyboard and write the name of the threat). Look through the results of the search and delete any entries that have the same or a similar name.
Next, to make sure that there are no infected directories, manually go to the directories below and delete/uninstall their content:
- HKEY_CURRENT_USER>>Software>>*Directory with a strange or suspicious name.
- HKEY_CURRENT_USER>>Software>>Microsoft>>Windows>>CurrentVersion>>Run>>*Directory with a strange or suspicious name.
- HKEY_CURRENT_USER>>Software>>Microsoft>>Internet Explorer>>Main>>*Directory with a strange or suspicious name.
In case the instructions in this guide didn’t work for you, then download a professional anti-virus program (like the one on this page) or contact us in the comments for assistance.


Hi. Thank you. But how will I know if the one listed below the local host are suspicious?
Send the IP’s to us and we will tell you whether you should remove them.
If you complete the guide with all of its steps, strictly following the instructions, there’s a high chance that you’d be able to handle the issue.
Did you complete all steps from our removal guide?
creating the .bat file in step 3 results in access denied also the CMD gives the same results
hi, have this ip´s below localhost
# localhost name resolution is handled within DNS itself.
# 127.0.0.1 localhost
# :: localhost
Addresses: 2607:f8b0:4008:807::200e
200.29.113.17 www. youtube. com
200.29.113.21 www. youtube. com
200.29.113.23 www. youtube. com
200.29.113.18 www. youtube. com
200.29.113.20 www. youtube. com
200.29.113.16 www. youtube. com
200.29.113.27 www. youtube. com
200.29.113.26 www. youtube. com
200.29.113.19 www. youtube. com
200.29.113.24 www. youtube. com
200.29.113.22 www. youtube. com
200.29.113.25 www. youtube. com
The addresses that you’ve send to use should get removed from your Hosts file because they are not supposed to be there.
thanks! 🙂
i love u bro thank you bro
I download the spy hunter antivirus to remove the drive.bat virus but still iybkeeps from coming back.. i tried also to reformat the drive but still coming back.
Didi you try the instructions from our guide?
Hi, recently i just realized that my flash drives were infected with shortcut virus (window batch file kaspersky 2017 something like that ) . I tried format but it keeps come back. When i formatted the drive, all the data was gone but there’s still shortcut when i opened. I already use malwarebytes, smadav, avast and so on but nothings happen. I tried those cmd prompt method and regedit so on but nothing happen. Pls help me get rid this stubborn shit!
What about the Hosts file, did you check there for any suspicious IP entries?
Yeah. I think there’s no other ip address, my ip only .
Did you execute the steps from the guide when in Safe Mode? If not, try using Safe Mode when troubleshooting this virus.
I already deleted the shortcut but there’s system volume information that cannot be delete. I found task host in it but i can’t delete it
Hey mate! I already found the solution. I’d end all the task incl antivirus. It works!!
hey, can you teach me how you do that?
Sure! I just boot my pc to safe mode thrn end all the suspicious task including antivirus task. Next, i just do command prompt thing
I used the run and paste (notepad %windir%/system32/Drivers/etc/hosts) and I found number ip i guess and the word localhost here so what should i do?
Can you send us the IP here so that we will be able to tell you if you need to remove it or if it is okay to leave it there.
Did you try using the instructions from the guide? Did it yield any results?
This file.bat is persistent and whenever i use step 5 and 6 it closes automatically, need help for this virus that hides my files
Are you doing all this in Safe Mode? If not, make sure you first boot into Safe Mode so that the malware cannot interfere.
Came back here just to say “Thank You!”. Most people are having problems, but I think that’s because they aren’t rebooting the system in safe mode and this is crucial. Thank you again.
We are very happy to hear that you’ve managed to deal with the issue with out help, you are most welcome!
Did you complete the guide and if you did, was there anything suspicious in the Hosts file and in the Registry Editor?
Hello! My flash drive was infected with this virus. I tried to delete and followed the steps provided above but it keeps coming back. And now the whole system of my computer was infected. I need help. What should I do? I’m afraid that it may damages all of my files.
Did you find anything suspicious in the Hosts file on your PC or in the Registry Editor?
Help! there are alot of weird things connected under my local host
You should probably delete them manually and then save the file but we still advise you to first send us the IPs that you’ve found there so we can tell you if they really need to be deleted.
Good day… Is it applicable to windows server 2012 R2?
It should be applicable.