Kkll
Kkll is malicious piece of code that locks all of your valuable files and then asks you to pay ransom for them. In order to restrict access to the victims’ files Kkll applies data encryption and changes the file extensions to its own.
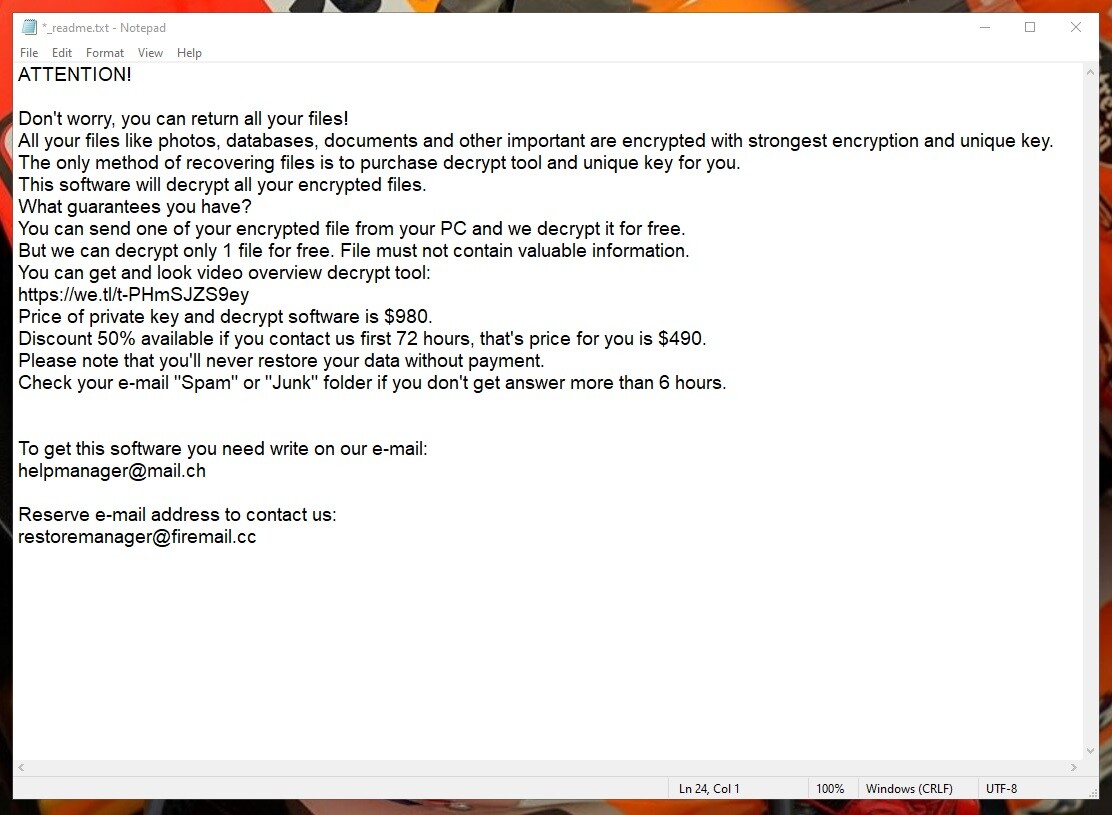
The Kkll Virus Ransom note
If you are among the latest victims of Kkll, on this page you will find important information about this devastating computer infection and the methods that you can use to remove it. What you should know right from the start is that Kkll is a ransomware cryptovirus and, in order to deal with it in the best possible way, you will need to make informed decisions as to what to do next.
In terms of its harmfulness, ransomware is a type of malicious software that typically seeks to restrict access to either your computer’s screen or the information that you store on it with the idea of asking a ransom in exchange for restoring the access. Viruses of this type normally do nothing else to harm or corrupt the system. That’s why, if you don’t keep any files of particular importance on the infected computer, the attack of Kkll won’t be at all problematic for you. All you will need to do is to remove the malware-related files from the system which is very doable with the help of a professional removal tool or a manual removal guide like the one that you can find below.
The Kkll virus
The Kkll virus is malicious software that targets and locks valuable user data in order to blackmail the owners for a ransom. The Kkll virus applies a complex encryption to a list of valuable files and then displays an intimidating ransom-demanding notice on the victim’s screen.
If you have already detected such a notice on your screen, this means that Kkll has managed to lock the files it targets on your computer, and that you can’t access those files anymore. The hackers behind the ransomware viruses like Kkll, Nlah and Pezi usually offer a potential path back to these files – a specially generated decryption key which is in their possession. To obtain this key, however, you would be required to transfer a fixed amount of money to their cryptocurrency account within a given deadline. If you refuse to do so, you will have to embrace the fact that your files will remain encrypted for good. This is because it is mainly by using the corresponding decryption key that the encrypted files can be accessed again. However, it’s a completely different story if the hackers would really send it to you should you really send them the ransom money. The individuals who run Kkll are, before all, cyber criminals that cannot be trusted. Thus, it is not a good idea to go straight with the ransom payment without having tried any other alternatives.
The Kkll file encryption
The Kkll file encryption is the method by which this virus encrypts files to ensure that no one can access them. The Kkll file encryption is a stealthy process that runs without visible symptoms and can only be reversed with a special decryption key.
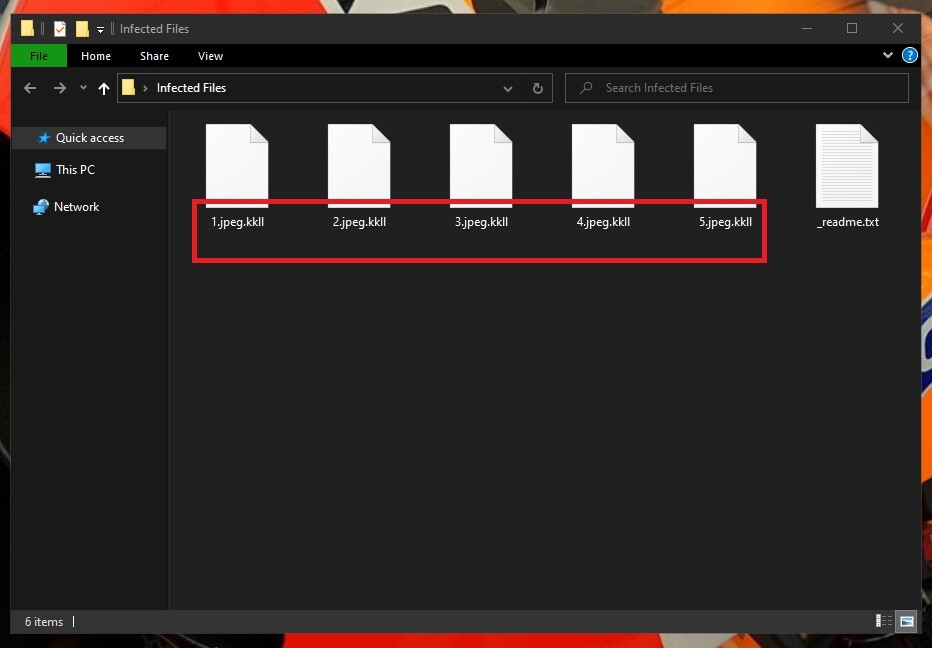
The Kkll Ransomware encrypted files
However, aside from paying a ransom for a mysterious decryption key, there are some other options that may be worth the try. Our recommendation is to first remove Kkll with the help of the instructions in the guide below so that you can have a clean and safe computer. Next, you can move to the second section where our free file-recovery suggestions can be found and tested without interacting with Ransomware hackers.
SUMMARY:
Remove Kkll Ransomware
You are dealing with a ransomware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to decrypt and recover your encrypted files (if it is currently possible). You can find the removal guide here.



Leave a Comment