This page aims to help you remove [email protected]. Our removal instructions work for every version of Windows.
[email protected]
[email protected] is another example of an email sextortion attempt. The perpetrators behind [email protected] imply they have personal information or videos of the affected user and demand payments in cryptocurrency not to release it.
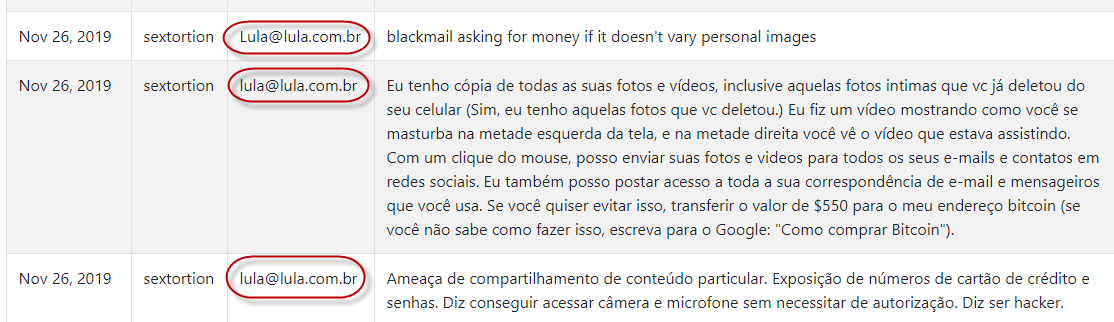
[email protected] hacker scam complaints
In the case of [email protected] hacker scam you are dealing with a complicated sextortion scam similar to Recorded You Email, Save Yourself Email ,Drive-by exploit and Bitcoin Blackmail Email Scam. While these are all scams it is entirely possible that you have a malware inside your device that cause such emails to appear inside your email inbox.
The Trojans Horses are terrible threats and it would be hard to find a virus more sophisticated than them. In this article, we have decided to provide our readers with some useful information about a new Trojan that has recently infected a number of web users. Its name is [email protected] and some of our readers have already had the misfortune of landing it on their machines. That’s why below you will find a thorough removal guide that contains instructions on how to manually detect and remove [email protected] from your system. There is also professional anti-malware software linked there that you can use to scan your device and remove the virus automatically. But let’s first give you some more information about what to expect from [email protected] and how to protect your system in the future.
Trojan Horses’ destructive abilities
One of the first things people want to know once they discover they’ve got a Trojan on their machine is what kind of damage this malware can do. However, thre’s usually no single answer to this question since these threats tend to be quite versatile.
First of all, the reason such malicious programs are called Trojans is that they invade your machine acting like a harmless file or application. Once inside, they can receive remote commands from the hackers behind them who use them carry out certain malicious deeds. What those deeds can be depends only on the hackers’ intentions.
For example, a virus such as [email protected] could be set to steal data from you. This is a common use for many Trojans and can be achieved using a variety of techniques. The malware can monitor your keystrokes, share your screen with the cyber criminals, or maybe send some files from your computer to the servers of the hackers without your knowledge. With the help of such a Trojan, the hackers can gain access to sensitive information like passwords, login details, personally identifiable information, etc. Another common activity the cybercriminals employ Trojans for is to send out spam or to infect the computer with other viruses. Speaking of this, Trojans are often used to introduce Ransomware into the victims’ system.
Some criminals may set the Trojan to spy on you, which can get pretty ugly. With its help, the hackers can obtain and exploit information related to your location, profession, social and financial status, and more. Most commonly, this data can be gathered by accessing your camera and microphone or by monitoring your keystrokes.
As you can see, the Trojans are really among the most dangerous pieces of malicious software out there and that’s why it’s critical that you delete [email protected] from your machine as quickly as possible. Of course, it is no less important that you learn how to avoid such infections and keep your computer safe. Therefore, we advise you to upgrade your security software and download all recommended system updates. Do not neglect such updates because they patch weaknesses of the OS that can easily be exploited by Trojans and other malware. If you don’t have an antivirus tool on your computer, consider investing in a reliable one. And last but not least, be mindful of your web browsing habits and try to avoid interaction with the most common sources of malware, such as malicious online ads and compromised spam messages.
SUMMARY:
| Name | [email protected] |
| Type | Trojan |
| Detection Tool |
Remove [email protected] Email Hacker Scam
Search Marquis is a high-profile hijacker – you might want to see if you’re not infected with it as well.

Leave a Comment