*Mlrd is a variant of Stop/DJVU. Source of claim SH can remove it.
Mlrd File
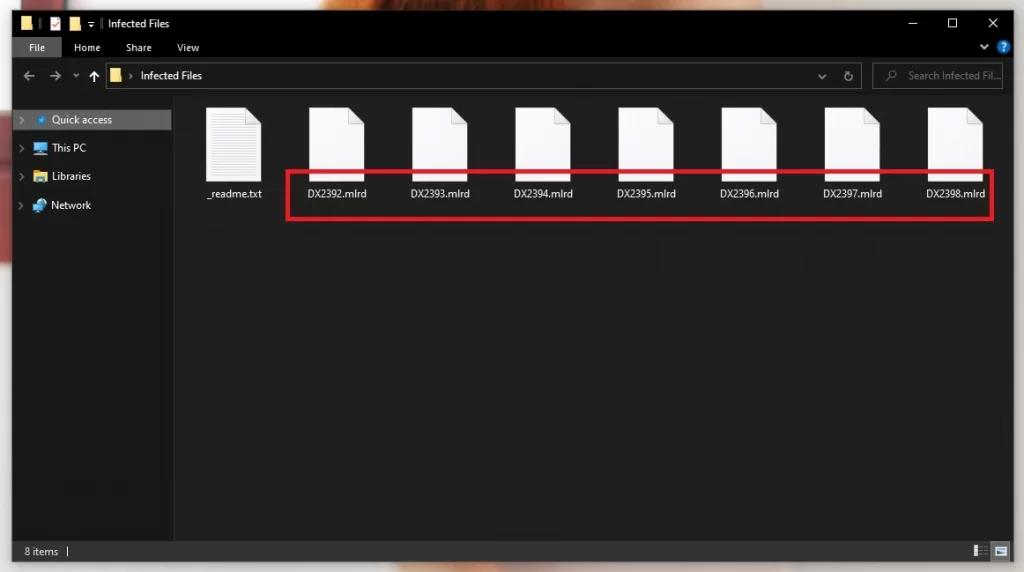
A Mlrd file is a hallmark of the devastating repercussions associated with the infection of the notorious ransomware virus of the same name. This malware variant permeates a computer system, utilizing a strong encryption algorithm to modify users’ data, turning them into a Mlrd file, an inaccessible version of the original. Victims then find their precious data locked behind an almost impervious encryption wall, with a unique extension signaling the dominion of the ransomware over the files. While the process is reversible technically, it demands a decryption key held by the attackers, and obtaining it usually involves succumbing to their monetary demands, a path fraught with uncertainty and potential deceit.
How to decrypt Mlrd ransomware files?
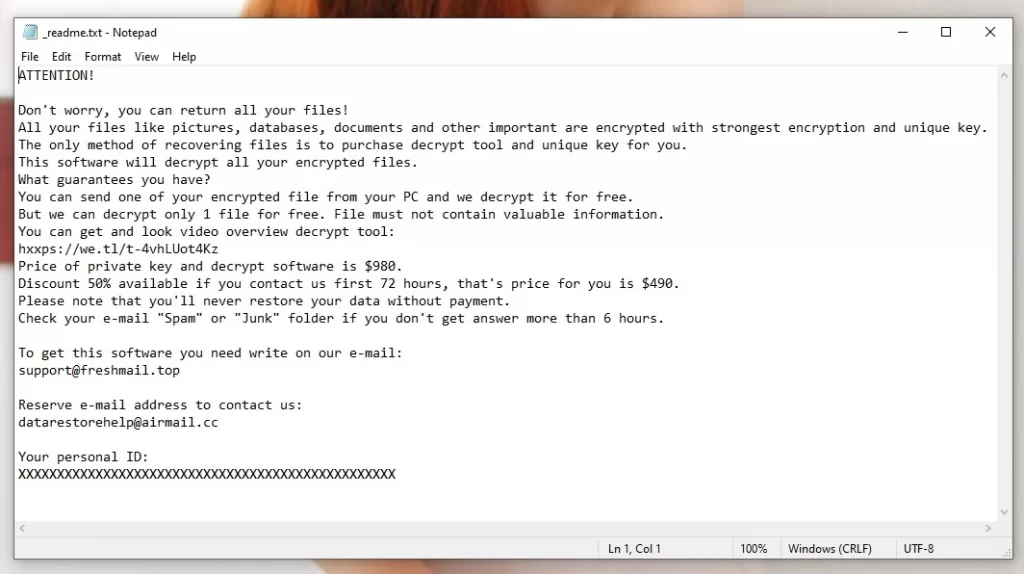
To unlock files encrypted by Mlrd ransomware, one has two options: acquiring the exclusive private key held by the attackers – necessitating a ransom payment — or opting for complementary alternative solutions, such as the one detailed at the bottom of this page. Although both pathways carry no assurance of file retrieval, the second option is considerably more secure, sparing you the risk of financial loss.
How to remove the Mlrd ransomware virus and restore the files?
Eradicating the Mlrd ransomware and retrieving your files necessitates a two-step process: initially, adhere to our removal instruction presented here, followed by utilizing the file recovery resource recommended at the conclusion of the guide.
Mlrd Virus
The Mlrd virus is ransomware that introduces itself into users’ systems, encrypting files and demanding a ransom, ostensibly in exchange for decryption. Like other similar threats, such as Ttza and Ttrd, this form of malware has a singular goal: to coerce victims into paying a ransom, leveraging their desperation to retrieve their encrypted files. What sets the Mlrd virus apart is its ruthless efficiency in encrypting files, creating a scenario of despair and urgency. While facing an attack from this ransomware, it is advised to explore all available recovery options before even considering meeting the attackers’ ransom demands, as payment does not guarantee the restoration of the encrypted files.
Mlrd
The Mlrd ransomware uses various distribution tactics to invade users’ systems, including spear-phishing emails, exploiting software vulnerabilities, and drive-by downloads from compromised websites. As a strategy to prevent the onset of an attack form this ransomware, users should maintain updated antivirus solutions and be vigilant about the digital platforms they interact with. Furthermore, adopting safe browsing practices, such as avoiding clicking on unverified links and being skeptical of unsolicited emails, can be significant preventative steps. It is imperative to foster a culture of cybersecurity consciousness to protect oneself from the detrimental effects of a Mlrd ransomware attack.
.Mlrd
The .Mlrd extension signals the cruel grip of this ransomware on your files. Once affixed to your documents, it denotes that they have been encrypted and are no longer accessible in their original form. Despite the grim circumstances, a glimmer of hope resides in potential recovery methods like utilizing backup resources or consulting a cybersecurity specialist for assistance. Even though there exist initiatives to develop decryption tools for various ransomwares, it remains a hard truth that the recovery of files marked with the .Mlrd extension is laden with uncertainties, with no guaranteed path to full data restoration, emphasizing the critical role of preventive measures.
Mlrd Extension
Files bearing the Mlrd extension have fallen under the control of the ransomware. Though not damaged, these files have been altered to a state where regular access is denied, forcing users into a corner of desperation. It is important to understand that payment of the demanded ransom should stand as a final recourse, owing to the unpredictability surrounding the recovery of the files post payment. Before considering the ransom route, victims should pursue all other alternatives for recovering files with the Mlrd extension, including seeking the assistance of professionals with expertise in dealing with ransomware issues to attempt restoring the data without succumbing to the perpetrators’ demands.
Mlrd Ransomware
The infiltration of Mlrd ransomware into computer systems can be attributed to a variety of tactics, including spam emails harboring malicious attachments and the exploitation of software vulnerabilities. Recognizing potential signs of infection early on, such as sudden system slowdowns or erratic file behavior, can facilitate preventive action, potentially thwarting the encryption process. Immediate countermeasures, such as disconnecting external drives and other devices, can mitigate the extent of the damage. Furthermore, fostering a vigilant approach towards email interactions and maintaining updated anti-malware tools can be instrumental in safeguarding against the Mlrd Ransomware or other similar threats.
What is Mlrd file?
A Mlrd file, delineated by this ransomware’s unique extension, is essentially a hostage in the digital world, where users’ critical files are encrypted and held at ransom by the ransomware. This kind of file alteration does not destroy the data but locks it behind a formidable encryption wall, making it inaccessible. Recovering a Mlrd file is a complex process involving a myriad of challenges, with the decryption key primarily held by the cyber criminals orchestrating the attack. Sadly, there is no guaranteed method of reclaiming such files, painting a scenario where prevention emerges as the most potent strategy to counter this cyber threat.
SUMMARY:
| Name | Mlrd |
| Type | Ransomware |
| Detection Tool |
*Mlrd is a variant of Stop/DJVU. Source of claim SH can remove it.
Mlrd Ransomware Removal

As a first step, be sure to save these Mlrd removal instructions to your browser’s bookmarks. In this way, you won’t have to search for the Mlrd removal guide after the system restarts that follow.
A Safe Mode restart will let you see what programs are currently running in the background of the system and will hopefully make it easier to detect and deal with Mlrd and its malicious processes. That’s why, we recommend you to restart the system with the help of the instructions from the link and then get back to the guide and proceed to step two.

WARNING! READ CAREFULLY BEFORE PROCEEDING!
*Mlrd is a variant of Stop/DJVU. Source of claim SH can remove it.
The second step involves launching the Task Manager by hitting CTRL, SHIFT, and ESC at the same time on your keyboard. In the Task Manager, look at the Processes tab to find out what processes are using up a lot of system resources. Right-click on any process that looks suspicious and select Open File Location from the context menu that comes on the screen to check the files linked with it.

All files connected with that process should then be scanned for harmful code using a powerful scanner. This guide includes a link to a free virus scanner that you may use for that purpose.

Before deleting the files the scanner has flagged as dangerous, go to the Task Manager, right-click on the suspicious process and choose End Process from the context menu to stop it from running. After that, go to the File Location folder and delete the dangers that the scanner has detected.
![]()
The Hosts file on a computer is a common target that may be modified by an attacker after the system has been hacked. Therefore, the next step is to manually check the file for IP addresses that may be troublesome (like those on the image below). You may access the Hosts file on your computer by simultaneously hitting the Windows key and R and pasting the following command into the box labeled Run:
notepad %windir%/system32/Drivers/etc/hosts
After that, search for “Localhost” in the text of the file and look for any weird IP addresses. Please use the comment box given below if you see anything suspicious about the IPs that you discover. In case we determine that the IP addresses you’ve detected are malicious, we will come back to you with some advice on how to proceed.

Using the Windows Search bar, enter “msconfig” then press Enter. This step will open the “System Configuration” window on your screen. Start-up-related items are listed in this window under the “startup” tab. Take a look at the items listed there and, if needed, remove any checkmarks from the items you think are linked to the ransomware. This will disable them and stop them from starting the next time the system restarts. Click “OK” to save your changes after that.


*Mlrd is a variant of Stop/DJVU. Source of claim SH can remove it.
More and more malicious programs are secretly adding harmful entries to the computer’s registry in order to avoid detection and continue to function for as long as possible after being installed on the machine. Therefore, in this step, you need to use the Registry Editor to find and delete any files linked with Mlrd that were installed on your computer without your knowledge. This will help you to fully remove the traces of the ransomware from your computer. To do that, in the Windows search bar, type regedit, and then click the Enter key on your keyboard to open the Registry Editor.
Pressing CTRL and F at the same time will allow you to search for files that may be related to the malware. Entering the name of the threat in the Find box that appears will help you search for it. Choose the Find Next button from the Find box to begin searching for malicious files.
Attention! Please be cautious while removing any files that appear in the search results! The risk of accidentally deleting non-malicious registry files should be considered before attempting to manually remove the registry files connected with the infection. In case you need help, an antivirus software (such as the one on this page) is your best bet when it comes to protecting your computer from potentially hazardous apps and dangerous registry entries.
Ransomware files may be stored in the following five computer locations. That’s why, we recommend you go through each of them and carefully check them for any unusual or recently added files. To do that, you’ll need to use the Windows Search bar and type in each of the following search phrases:
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
Look for files that may contain harmful code, but don’t make any changes or remove anything unless you’re confident in your actions. To delete any temporary files in your computer’s Temp directory, hold down the CTRL and A keys and then hit the Delete key on your keyboard.

How to Decrypt Mlrd files
Trying to decode ransomware-encrypted data is difficult for non-ransomware experts. Decryption methods might vary based on the variant of ransomware that was used to encrypt the data, making it more difficult to get it back. Ransomware variants may be identified by looking at the file extensions that are appended to the encrypted files.
Before you begin the process of data recovery, however, you must first do a thorough check of your computer using an anti-virus program (like the one offered on our website). It’s safe to look at the file recovery solutions available to you only after you’ve conducted a complete virus scan and found none.
Next Djvu Ransomware
A new variant of ransomware known as STOP Djvu ransomware is a source of disturbance for a lot of users and security experts globally. This malware often adds the extension .Mlrd at the end of the encrypted files. The good news is that decryptors like the one below may be able to help you retrieve your encrypted data in the event that you’ve been affected by this threat:
https://www.emsisoft.com/ransomware-decryption-tools/stop-djvu
To begin decrypting the files, you must first run the STOPDjvu.exe program that has been downloaded to your computer. Upon downloading the file, choose “Run as Administrator” and then press the “Yes” button to proceed. Read the license agreement, together with any accompanying instructions, thoroughly. The program may not be able to decrypt data encrypted using unknown offline keys or online encryption techniques, so be aware of that.
Our website has anti-virus software that can help you remove the Mlrd ransomware if you’re having problems with that. Alternatively, you may use our free online virus scanner to do a manual scan on any files you suspect may be dangerous.

The issue is how to Decrypt the Decrypt files ? already remove virus but still are encrypted
Hi Godfrey Genes Mrina,
did you use the decryptor in Step 5 ? It will tell you if you are encrypted by offline or online key. If your files are encrypted by an online key, i am afraid that decryption is impossible.