*Mlza is a variant of Stop/DJVU. Source of claim SH can remove it.
Mlza File
A Mlza file encryption is the digital equivalent of putting your files in a vault and throwing away the key. It’s a malicious process that takes your precious data and transforms it into an unreadable format. When ransomware infects your system, it selects specific files to target—typically ones you’d really miss, like personal photos, work documents, or financial records. It then employs a complex Mlza file encryption algorithm that shuffles the content of these files into an indecipherable code. Think of it as turning your favorite song into a chaotic mix of notes. To make matters worse, the ransomware attackers send you a ransom note, demanding payment in cryptocurrency for the decryption key. Until you pay that ransom or find a way to defeat the encryption, your files remain in lockdown.
How to decrypt Mlza ransomware files?
Decrypting files encrypted by the Mlza ransomware can be a daunting task, and it’s not recommended to attempt it without expert guidance. Your best course of action is to reach out to cybersecurity professionals or reliable manual removal guides, as they may offer access to decryption tools or solutions. Attempting to decrypt files without the right tools and expertise can lead to permanent data loss. While there’s no one-size-fits-all approach, some ransomware strains do have decryption tools available, thanks to the efforts of security researchers. Check trustworthy sources like cybersecurity blogs or the official websites of law enforcement agencies for any potential solutions. Above all, avoid paying the ransom, as it’s risky and supports criminal activities.
How to remove Mlza ransomware virus and restore the files?
To remove the Mlza ransomware virus and restore your files, you can seek professional assistance from cybersecurity experts or use a trusted step-by-step removal guide that may have access to decryption tools or methods tailored for the Mlza ransomware. Attempting to remove the ransomware without proper instructions is risky, as it can result in further damage to your system. For file restoration, use clean and up-to-date backups of your data, ensuring they are free from malware. Avoid paying the ransom, as it’s discouraged due to the risks involved and the fact that there’s no guarantee of recovering your files.
Mlza Virus
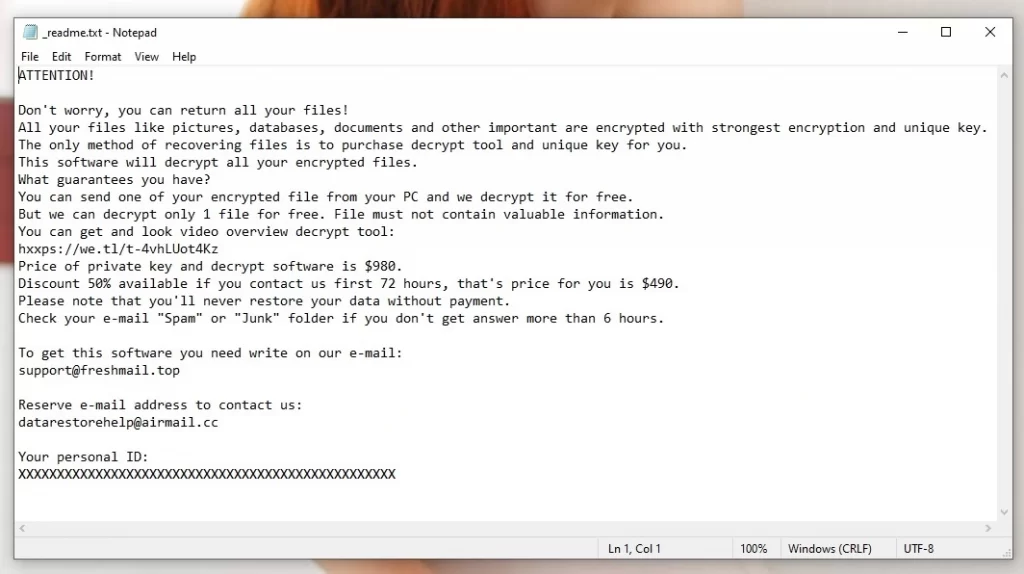
When the Mlza virus encrypts your files, it is basically placing them in a digital straitjacket. Your once-accessible documents, photos, and other data are now wrapped in an intricate encryption that renders them utterly unreadable. Trying to open one of these encrypted files is like attempting to solve a puzzle without any clues. To make matters worse, the attackers behind the Mlza virus often taunt you with a ransom note on your screen, demanding payment for the decryption key. Until you comply with their demands and pay the ransom, your files remain effectively locked away, inaccessible, and beyond your control. This situation leaves victims feeling helpless and facing a difficult decision: pay the ransom and hope for the best, or seek professional help to recover their data without giving in to the attackers’ demands.
Mlza
Discovering your files encrypted by Mlza can be distressing, but a methodical response is essential in order to handle the situation. It’s vital not to grab the idea of paying the ransom, as it comes with a number of risks and only supports the criminal activity. Instead, what we suggest is to promptly report the incident to law enforcement agencies, as this can aid in the investigation and tracking of cybercriminals and seek assistance from cybersecurity professionals with expertise in ransomware recovery—they may possess the necessary decryption tools and ransomware-removal guides. If you have clean and up-to-date backups, you can utilize them to restore your system. Lastly, to mitigate future risks, keep your software updated, implement strong password policies, install reputable antivirus software, and educate yourself on ransomware prevention.
.Mlza
If you are curious to learn if it is possible to decrypt ransomware-encrypted files without paying the ransom, you should know that there may be some options, but nothing is guaranteed, and the process requires some precautions. In some instances, cybersecurity experts have successfully deciphered the encryption used by specific ransomware strains, leading to the development of free decryption tools that may work for your case too. However, you should exercise caution when searching for decryption tools online. Not all tools are safe; some may be malicious. Stick to downloading decryption tools from trusted sources, to minimize the risk of further harm. Additionally, having clean backups of your data is a reliable method for recovery.
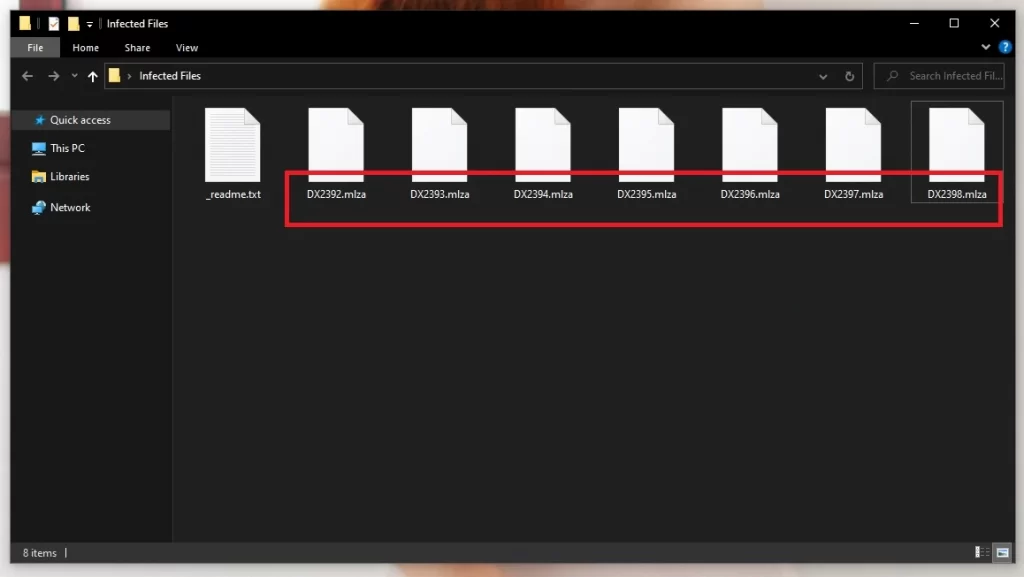
Mlza Extension
Ransomware often operates silently, but there are potential warning signs before it encrypts your files. For instance, you can look out for sudden computer slowdowns or unusual system behavior, as the ransomware may use a significant portion of your resources. Be cautious of suspicious emails, especially those with unexpected attachments or links, as they can be the entry point for ransomware infections like Ttza and Ttrd. Once your files are encrypted, you’ll notice changes in their file extensions, such as the Mlza encryption, and they’ll become inaccessible. Typically, after applying the Mlza encryption to all files that are targeted, the ransomware displays a ransom note on your screen, and demands payment for the decryption key.
Mlza Ransomware
The Mlza Ransomware attackers typically demand payment for decryption keys in cryptocurrency, such as Bitcoin, because it offers a level of anonymity. They provide victims with detailed instructions on how to acquire the required cryptocurrency and send it to a specified wallet address. Once the payment is made, victims are instructed to provide proof of payment to the attackers. After verification, the Mlza ransomware attackers are supposed to release the decryption key. However, paying the ransom is fraught with risks, including the possibility of not receiving the key or being targeted again in the future. Therefore, a more prudent approach is to recover your files from clean and unaffected backups, which is a safer and more reliable method.
What is Mlza File?
Ransomware is an equal-opportunity encryptor – it doesn’t discriminate when it comes to file types. This malicious software is designed to target a broad spectrum of files and turn them into Mlza files, ranging from everyday documents and images to more specialized data formats used by software applications. Whether it’s your cherished family photos, critical business documents, or specific files used by software programs, ransomware can lock them all behind an encryption wall. This means that practically any file that you store on your computer can become a Mlza file, that is encoded and inaccessible.
SUMMARY:
| Name | Mlza |
| Type | Ransomware |
| Detection Tool |
*Mlza is a variant of Stop/DJVU. Source of claim SH can remove it.
Mlza Ransomware Removal

Save this page to your browser’s bookmarks for easy access to the Mlza removal instructions.
Following the bookmarking of the Mlza removal guide, you will need to restart your computer in Safe Mode. Please go to this URL for detailed instructions on how to restart your computer in Safe Mode.
When the computer restarts, type msconfig into the Windows search box at the bottom of the Start menu and press Enter.
The System Configuration window will appear next. Disable anything Mlza may have added to the list by unchecking its checkmark in the Startup tab. After you’ve finished configuring the startup items, click OK to exit.


WARNING! READ CAREFULLY BEFORE PROCEEDING!
*Mlza is a variant of Stop/DJVU. Source of claim SH can remove it.
A number of damaging activities begin as soon as the ransomware infection is activated. If you believe Mlza’s behavior is linked to a specific Task Manager process, the next step is to locate and terminate that process.
To access the Task Manager, simply press CTRL, SHIFT, and ESC on your keyboard. Select the Processes tab, carefully search for a process that is dangerous or linked to the ransomware, right-click on it and select Open File Location from the context menu.

After that, scan the files associated with that process for malware using the free virus scanner provided below:

It is vital that any potentially hazardous files detected by the scanner be removed as quickly as possible, but in order to do so, you must first end the corresponding process that is currently running in Task Manager.
To end a dangerous process, right-click it and select the “End Process” option from the quick menu.
![]()
If your computer has been infected with malware like Mlza, the Hosts file could be one of the places where dangerous alterations appear. As a result, we recommend that you open and thoroughly inspect your Hosts file, looking for changes under Localhost in the text to ensure that everything is in working order.
To do so, press the Windows Key and R at the same time on the keyboard to open a Run dialog box, and paste the following command into it:
notepad %windir%/system32/Drivers/etc/hosts
When you click OK, the following file should appear on your screen:

If you notice any IP addresses that look questionable, as shown in the image above, please let us know by leaving a comment after this guide. We’ll look into the IPs that look suspicious and give you some recommendations.

*Mlza is a variant of Stop/DJVU. Source of claim SH can remove it.
Dangerous files are frequently introduced to your computer’s Registry as a result of a ransomware infection. What’s more crucial is that you search the Registry for malicious entries and delete anything you think is linked to the infection.
Type Regedit in the Windows search field and press Enter to open the Registry Editor. Then, by clicking CTRL and F at the same time, open the Editor’s Find dialog box and type the ransomware’s name in it. Then, to see whether any entries with that name exist, click the Find Next button and start a search. Because the malware could be linked to anything found in the search results, it’s better to get rid of it.
Attention! Regular users may cause major damage to the system if they don’t know which files to delete from the registry. For this reason, a professional removal program should be used to remove any threats and hazardous files from the system and the registry.
After you’re sure the Registry is clean, you can close it and use the Windows search field to manually search for harmful items in the following five places:
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
Type each of the following lines into the search area (including the percent sign) and click Enter to access them. After that, in each of them, search for new files or folders with unusual names.
If you notice anything questionable, remove it immediately. Select and delete all temporary files stored in Temp. This action will delete any temporary files created by the malware.

How to Decrypt Mlza files
Victims may need to use a variety of tools and methods in order to decrypt Ransomware-encrypted data. The first thing that you need to do if you have been infected is to make sure you know which variant of ransomware has encrypted your data. Look at the file extensions that have been applied to the encrypted files to figure this out.
New Djvu Ransomware
STOP Djvu ransomware is the most recent Djvu ransomware variant that is actively attempting to infect systems all around the world. The .Mlza suffix is added at the end of all files encrypted by this ransomware variant. The only chance to decode STOP Djvu-encoded files right now is if they were encrypted with an offline key. To assist you with decrypting your data, we’ve included a link to a decryptor tool that you might find useful:
https://www.emsisoft.com/ransomware-decryption-tools/stop-djvu
To save the STOPDjvu.exe file to your computer, open the URL and click the Download button in the top right corner of the window.
Select Run as an administrator and then press the Yes button to open the file. After reading the license agreement and the brief instructions for use, you may begin the decrypting process by clicking on the Decrypt button. To be maximum accurate, we should note that this decryptor does not support decryption of files encrypted with unknown offline keys or online encryption, so please keep this in mind.
A professional anti-virus tool or a sophisticated online virus scanner can be used to eliminate Mlza and other malware from your computer. If you have any questions or concerns while completing the steps in this guide, please do not hesitate to write to us in the comments.

Hi there
.MLZA ransomware
What will decrypte my files
Hi Coenrad,
did you check the decryptor in Step 5 ?
I wish to know too! I had atack on 10. October.
How can I be sure that it will works with .mlza files?
Hi Nesko
if you are encrypted with an offline key it will decrypt your files, but if you are infected with an online key, decryption is impossible.
Excuse me, i can’t decrypt my files because of this: “The underlying connection was closed: an unexpected error occurred while sending”
Do you know how to fix this problem ?
Hi Rachid,
What were you doing to receive that message? What program showed you this error?