This page aims to help you remove .Nakw for free. Our instructions also cover how any .nakw file can be recovered.
.Nakw
.Nakw is a cryptovirus designed to extort money from its victims. To do that, .Nakw encrypts the victim’s files, making them inaccessible, and demands a ransom payment to decrypt them.
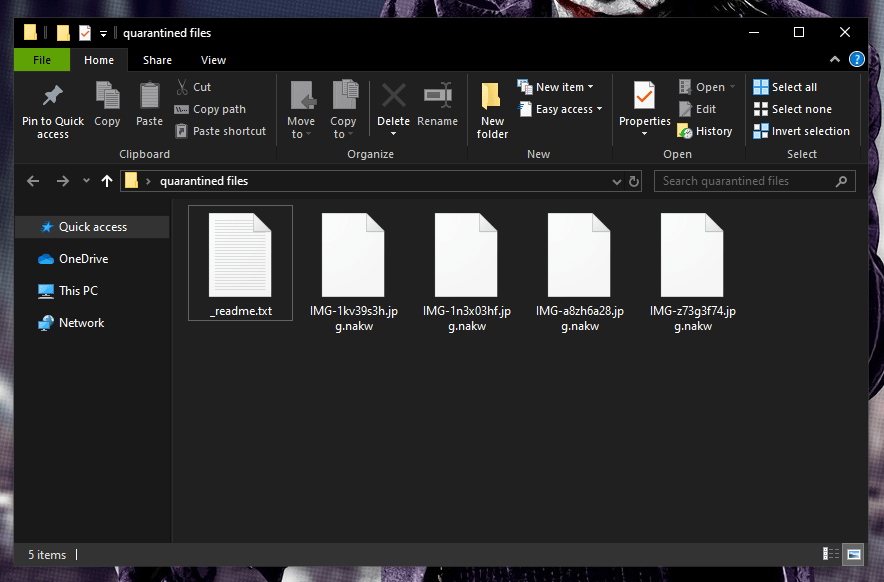
Once the .Nakw Virus has infected your computer it will stealthily encrypt your files.
In case your computer has been infected with .Nakw, .Derp or .Coot and your most needed files have been encrypted, we have prepared a special removal guide to help you remove this infection and deal with its consequences. We have also included a few steps through which we will try to help you get the encrypted files back. Please note that some of the files may not be restored, but it will certainly be worth trying out some alternative methods before resorting to the ransom payment that .Nakw requires. That’s why we suggest that you first read through the following article where you will find the most important information about the threat you are facing. This will help you defend your computer from similar Ransomware viruses in the future and will also provide you with a clear understanding of the malware that took your data hostage.
The .Nakw virus
The .Nakw virus is a ransomware infection that encrypts user files and generates a decryption key for them. The attackers behind the .Nakw virus keep the corresponding decryption key in secret and demand a ransom for it.
.Nakw is a Ransomware program that infiltrates one’s device and encrypts certain files stored on it, making them unreadable for any existing program. This ensures that the victims cannot view or open the encrypted documents without purchasing the special decryption key from the hackers behind the infection. The reason Ransomware is so common and feared is that it is almost impossible to break the encryption it applies without the corresponding decryption key. Besides, the cryptovirus itself is notoriously stealthy and the encryption process it initiates in most cases runs without any detectable symptoms.
The techniques used by hackers to spread Ransomware are many. Therefore, there are many ways in which you may get infected with .Nakw. The so-called malvertisements are probably the most popular method of distribution since these are advertisements that have either been created by cyber criminals who have injected them with malware or have been hacked and loaded with the malicious payload secretly. When you click on one such malvertisement, it will either redirect you to a dangerous website or install a virus directly onto your system. With this in mind, it is a good idea to ignore any pop-ups, banners, or other forms of aggressive online advertising materials because, if they have been compromised, you won’t have any way to tell the difference before it’s too late.
Other popular methods of Ransomware distribution may involve the use of spam emails, malicious attachments, cracked software installers, or Trojan Horse infections. The purpose of the latter is to weaken the security of your system and secretly inject the malicious file-encrypting code.
The .Nakw file encryption
The .Nakw file encryption is the final phase of the Ransomware’s attack. Once the .Nakw file encryption has been applied to your files, a ransom-demanding message will appear on the screen.
The file encryption is a method used by the creators of the Ransomware to block the access to your data. In general, the file encryption process is not malicious and does not corrupt your information. It simply locks it up and makes it accessible only through the use of a special decryption key. Precisely that key is in the center of the blackmailing scheme. The hackers require a ransom in order to give it to you and threaten that if you don’t pay, you will never be able to unlock your files again. The removal guide below, however, contains alternative file-recovery methods, which may help you avoid the ransom payment. In order to give them a try, though, you first need to remove .Nakw from your system. This will ensure that the files you manage to recover will not get encrypted again and your system will be safe for normal use.
SUMMARY:
| Name | .Nakw |
| Type | Ransomware |
| Detection Tool |
.Nakw Ransomware Removal
You are dealing with a ransomware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to decrypt and recover your encrypted files (if it is currently possible).
You can find the removal guide here.

Leave a Comment