*Pthh is a variant of Stop/DJVU. Source of claim SH can remove it.
Pthh File
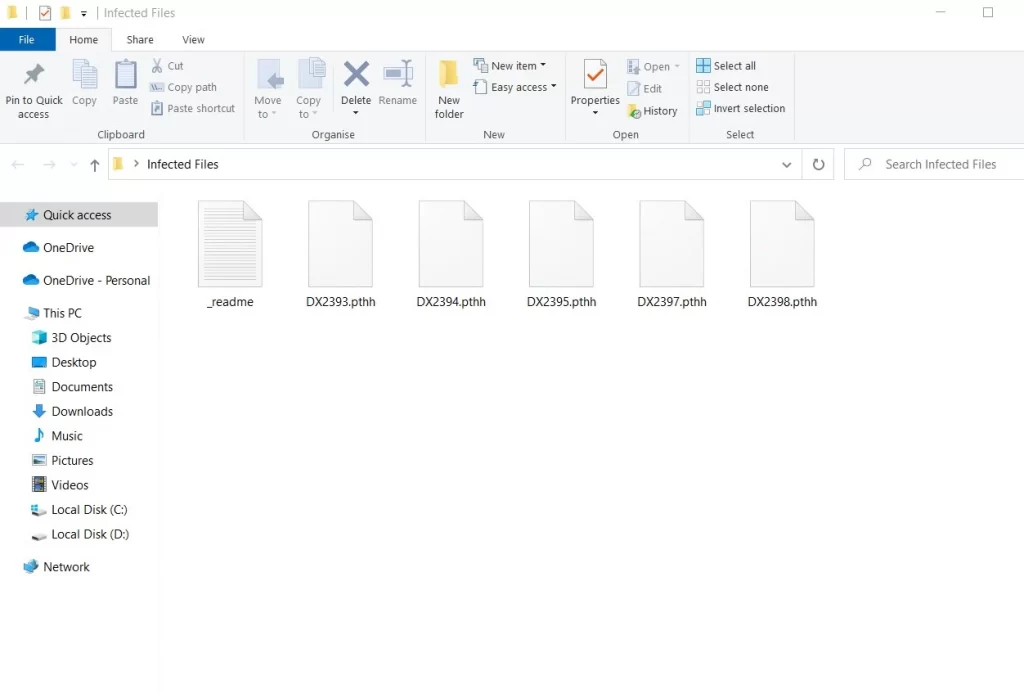
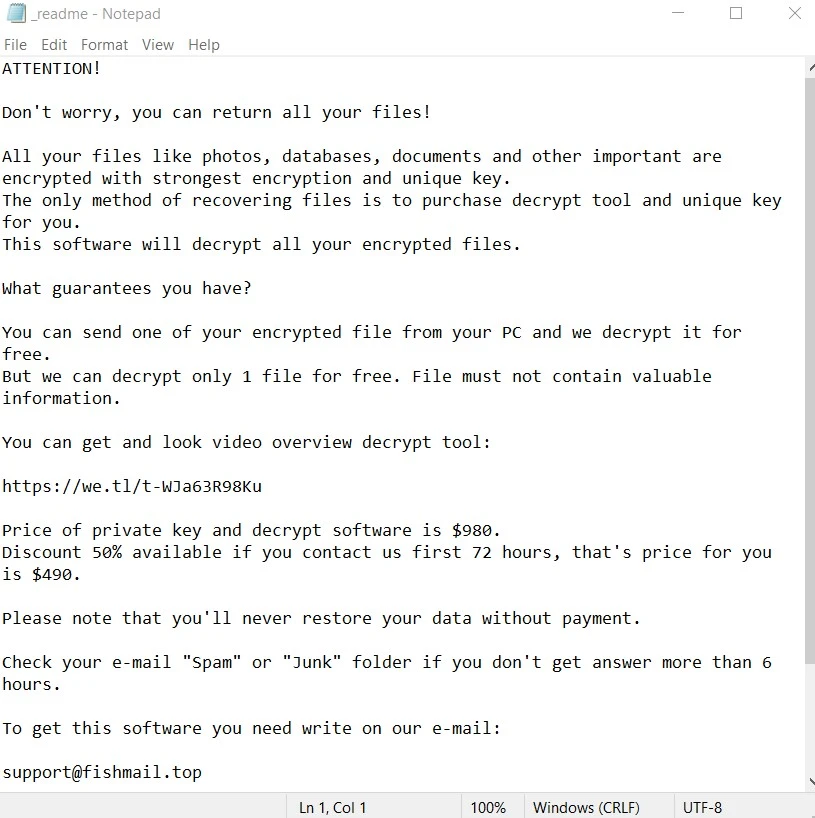
Pthh file is a recently reported ransomware threat, similar to Ttza and Ttrd, that is causing a lot of trouble. One clear indicator of the presence of an Pthh file on your system is the sudden encryption of your data and the change of the file extensions with unrecognizable ones. The ransomware attackers behind this threat often leave a ransom note on your desktop, demanding payment for decryption. If you’re unable to open files or applications and receive error messages indicating corruption or inaccessibility, it’s a red flag. Sluggish computer performance or unusual spikes in CPU usage could also suggest ransomware activity. So, keep an eye out for any changes to your desktop wallpaper or unfamiliar icons on your desktop. By promptly identifying these signs, you can mitigate the impact of a ransomware attack.
Decrypting Pthh ransomware files can be a complex process, but there are methods available in some cases. Some cybersecurity professionals may succeed in developing decryption tools that can unlock files encrypted by certain ransomware strains. These tools typically exploit weaknesses or vulnerabilities in the ransomware’s encryption algorithms in order to reverse their code. However, it’s essential to understand that not all ransomware strains have known decryption methods, and the effectiveness of these tools can vary. For this reason, it is of utmost importance to detect the correct variant of the ransomware that has attacked you and to seek solutions that are specific to it.
How to remove Pthh ransomware virus and restore the files?
Removing Pthh ransomware from your personal computer and recovering encrypted files can be a complex process. In case of an attack, disconnecting the infected computer from the network to prevent further damage and isolating the ransomware is highly recommended. It’s crucial not to pay the ransom, as it doesn’t guarantee file restoration and may cause more harm than good. Seeking professional help from cybersecurity experts or reliable self-help solutions may help you find decryption tools for your specific ransomware strain. For ransomware removal, employ trusted antivirus and anti-malware software to scan and eliminate the malware.
Pthh Virus
The Pthh virus can infiltrate personal computers through various entry points, with phishing emails being a prominent one. Cybercriminals often craft convincing emails with malicious links or attachments, tricking users into clicking and installing the Pthh virus without knowing it. Downloading software or files from unverified sources, like peer-to-peer networks or dubious websites, is another common entry point. You should also keep an eye for outdated software and operating systems with unpatched security vulnerabilities as they are also targets for ransomware attacks. Additionally, weak or reused passwords can be exploited to gain unauthorized access to your computer, opening the door for ransomware infections.
Pthh
Discovering that your personal files are encrypted by Pthh can be distressing, but it’s imperative not to consider paying the ransom, as such an action is full of uncertainty and only supports the criminals behind the malware. A much better course of action is to report the incident to law enforcement agencies, and seek expert guidance from cybersecurity professionals or reliable self-help guides in ransomware recovery as they may possess the necessary decryption tools. If you have clean and up-to-date backups of your encrypted files, you can use them to minimize the data loss. Aside from that it is important to think about mitigating future risks of attacks by keeping your software updated, installing reputable antivirus software, and educating yourself and your family about effective ransomware prevention measures.
.Pthh
Paying the ransom to recover your .Pthh data should be a last resort and is generally not advisable for several reasons. Firstly, there’s no guarantee that the cybercriminals will honor their end of the bargain and provide a working .Pthh decryption key. Secondly, paying the ransom financially supports criminal activities and perpetuates the ransomware cycle, leading to more attacks on other victims. Additionally, paying the ransom may not remove your device from the attacker’s radar; they may view you as a potential target for future extortion. So, instead of resorting to payment, explore alternative options like reporting the incident to law enforcement, seeking professional assistance, and focusing on preventive measures such as robust backups and cybersecurity practices to protect your data from ransomware threats.
Pthh Extension
Preventing the Pthh extension from being attached to your most valuable requires following several key best practices. You can start by ensuring your operating system and software are consistently updated, as these updates often contain essential security patches. Regularly back up your critical files to an offline or external location to safeguard your data. Exercise caution when dealing with email attachments and links, especially in unsolicited or suspicious emails. Install and maintain up-to-date antivirus and anti-malware software to provide an additional layer of protection against ransomware threats such as the Pthh extension. And lastly, stay informed about the evolving ransomware landscape to recognize and evade potential threats effectively.
Pthh Ransomware
The Pthh ransomware attack on personal devices can not only lead to valuable data loss, but may also escalate to other cybercrimes such as financial or identity theft. The ransomware is often just the initial phase, as the cybercriminals who operate it may exploit the compromised system to steal personal information, such as financial data and login credentials. This stolen data can be used for identity theft, leading to financial fraud and reputation damage. Paying a ransom to cybercriminals can have lasting consequences as well, as it fuels their criminal activities and encourages them to continue targeting victims. Besides, you might end up on a list of individuals who are willing to pay, making you a recurrent target for future Pthh ransomware attacks.
What is Pthh File?
Securing your personal files and photos from becoming useless Pthh files involves several key practices. Regularly back up your data to an offline or external storage device to ensure you can recover your files in case of an attack. Use strong, unique passwords for your accounts, and consider employing a trusted password manager for added security. Exercise caution when dealing with email attachments and links, especially from unknown senders, as phishing emails are a common vector for ransomware. Keeping your operating system and software up to date is crucial, as these updates often include vital security patches that can deter Pthh file attacks. Antivirus programs also play a crucial role by detecting and blocking ransomware threats before they can compromise your system.
SUMMARY:
| Name | Pthh |
| Type | Ransomware |
| Detection Tool |
*Pthh is a variant of Stop/DJVU. Source of claim SH can remove it.
Important points to consider before attempting the Pthh removal
There are a couple of important things you need to take into consideration before you start preforming the removal steps.
- First and foremost, if you haven’t done this already, now is the moment to disconnect any external drives, USB sticks, phones, or tablets from the infected computer in order to stop the virus from encrypting whatever files are stored in them.
- Next, consider disconnecting your PC from the Internet and opening this guide on another device. The reason for this is to prevent Pthh from connecting to its creators’ servers and receiving new instructions from them.
- Thirdly, even though it is not advisable to pay the hackers the demanded ransom sum, if this is your only remaining option, and you’ve decided to go for it, then we recommend not deleting the virus yet. Instead, it’ generally better to postpone the removal for after you’ve paid the ransom and hopefully received the private key for your files. Of course, after that, you still need to delete Pthh.
- Last, but not least, note that it is possible that the virus may have automatically removed itself from your computer to prevent anyone from reverse-engineering the decryption key. That said, even there are no visible Ransomware symptoms, completing the guide is still strongly advised just to be sure that the virus is truly gone.
How to remove the Pthh virus
To remove Pthh, you can either use a reliable anti-malware program to automatically erase the virus or complete the following manual steps:
- First, look in Control Panel > Uninstall a Program for any program that may have caused the infection and perform its uninstallation.
- Also ensure there aren’t any rogue processes that are still active on the computer by using the Processes section of the Task Manager.
- Thirdly, you must clean the AppData, LocalAppData, Temp, WinDir, and LocalAppData folders from malicious files.
- Lastly, see if any unauthorized changes have been made to the Hosts file, the Tasks Scheduler, and the Registry, and override such changes.
To ensure that each step is completed correctly, it’s strongly advised that you take the necessary time to read the more detailed description that we’ve shared below before you start the removal process.
Detailed steps for removing Pthh
Step 1
If the virus has entered your PC through another program that has served as a malware-carrier, then you need to open the Start Menu, type Uninstall a Program, and hit Enter to see a list of all programs installed on your PC. In that list, look for anything that has been installed around the time of the Ransomware infection and if you find a program that could be related to the attack by Pthh, select its entry in the list, click the Uninstall option that will appear at the top, and then perform whatever uninstallation steps show on your screen. Be sure to carefully read the removal settings (if there are any) so as to use the ones that would ensure full removal of the unwanted/malicious program.

If you are currently unable to delete the program for whatever reason, simply continue with the guide and once you are finished with all the other steps, try the uninstallation again.
Step 2
WARNING! READ CAREFULLY BEFORE PROCEEDING!
*Pthh is a variant of Stop/DJVU. Source of claim SH can remove it.
Now, to make sure that there aren’t any Pthh processes running in the background, type Task Manager in the Start Menu, press Enter, and look for any suspicious items in the Processes tab. If you see a process that has the same or a similar name as any program you may have tried to uninstall in Step 1, right-click the process, Open the File Location, then return to the Task Manager, right-click again on the rogue process, and click the End option. Then go to the folder you just opened and delete everything that’s in it.


You must also look for other processes with unusual names, especially if they have suspiciously-high memory and CPU usage. To see if any such processes are truly harmful, look up their names and also scan the contents of their location folders with the help of the powerful free malware scanner shown below.

Again, if a rogue process is found in your Task Manager, you need to quit it and delete the location folders where its files are stored.
Step 3
If Pthh is still in the system, it may attempt to restart any of its processes that you may have managed to stop, so, to make sure it doesn’t succeed in doing so, boot your computer into Safe Mode by following the steps from the linked page.
Step 4
*Pthh is a variant of Stop/DJVU. Source of claim SH can remove it.
Now you must make sure that no malware data is left on your computer, but you must first “unhide” the hidden files and folders on your PC. To do that, search for Folder Options in the Start Menu, open the first icon from the results, click its View tab, and check the Show hidden files, folders, and drives setting, after which click on OK.

Now open the Start Menu again, type %AppData%, and press the Enter key. Sort the files that are stored in the folder that appears on your screen according to their creation date, and then delete everything after Pthh entered your PC. Once you do this, the same thing must be done with three other folders: %LocalAppData%, %WinDir%, and %ProgramData%.
Next, you should visit the %Temp% folder and there you must delete everything that’s stored in it. To do this quickly and easily, press Ctrl + A, then press Del, and click on OK – this will delete every file and folder in Temp.


Step 5
For this step, first search for Task Scheduler in the search box of the Start Menu, and once you open the Task Scheduler app, click its Task Scheduler Library folder in the top left. Next, look at the Task listed in the center of the window and delete the pens you think maybe malicious or that you are not familiar with by right-clicking them and selecting Delete.

After that, if you are on Windows 10, open the Task Manager and click on Startup. If you are on Windows 7, type msconfig in the Start Menu, press Enter, and open the Startup tab in the System Configuration window. Now, look at the listed items, disable the ones you deem suspicious and untrusted, and click OK.

Now open the drive where your OS is installed – on most computers, that’s the C: drive – and go to the following folder: Windows/System32/drivers/etc. In that folder, double-click the file named Hosts, choose Notepad as a program to open the file with, and then look at the text in the file. If anything is written past the two “Localhost” lines at the end of the file, copy whatever text might be there and send it in the comments section. Soon, a member of our team will let you know if that text is from the malware and if you need to delete it from Hosts.

Step 6
For step 6, you must first press Winkey + R, then type regedit.exe in the small search box that pops up, and hit Enter. When asked if you are sure you want to start the program and give it permission to make changes to your system, click Yes. When the program (Registry Editor) opens, go to its Edit menu and, in it, click on Find. Now is the Registry Editor Find box to search for Pthh and then delete whatever may be found. Always make sure to repeat the search after every item that you may delete to check if there aren’t any other rogue items left in the Registry. We also recommend searching for items related to the program from Step 1 and deleting them as well.

The final thing you must do in the Registry is to go to the locations shown below, to look for strangely-named items in them, and to tell us about anything suspicious you may find there. By “suspicious”, we mean any items with names that look like randomly-arranged sequences of numbers and letters, similar to something like this “0239ur0390932ru0923ie0932i”.
- HKEY_CURRENT_USER > Software
- HKEY_CURRENT_USER > Software > Microsoft > Windows > CurrentVersion > Run
- HKEY_CURRENT_USER > Software > Microsoft > Internet Explorer > Main
How to decrypt Pthh Virus files
To decrypt Pthh Virus files, you can use a specialized decryptor tool to reverse-engineer the decryption key for your locked files. However, to be able to decrypt Pthh Virus files in this way, you will need to find several original versions of encrypted files.
If you can find accessible original versions of a couple of the files that the virus has encrypted, you can use the following steps to try to get a decryption key for the rest of your files – the process of doing so is free, and it involves the use of a specialized decryptor tool.
- First, find several pairs of files as we mentioned and then download the decryptor tool available on this page.
- Right-click on the downloaded file and select Run as Administrator.

- Click Yes when you are required to give your Admin permission to start the program.
- Agree to the Terms and Conditions for using the program.
- Now select the Browse buttons in the program’s window, navigate to the one of the file pairs, and select the corresponding files.

- If you can find a notepad file of the ransom note, use the browse button in the Ransom Note section to navigate to it and use it for finding the key.
- Click Start and wait as the decryptor tries to find a key for your files. If it gives you an error message, try using another pair of files (this is why it’s recommended to have several pairs at your disposal).
- If a key is found, browse to the directory where there are encrypted files and use the tool to decrypt them. If the program skips any files, it means that means they require a different key that is unknown to the program.

Thanks