2conv
In the event that your Chrome, Firefox, Explorer or another favorite browser of yours has been invaded by a program called 2conv, there is no need to panic. Despite that they are not programs that can steal data, nor do they cheat us, applications like 2conv can accidentally redirect us to pages that do it.
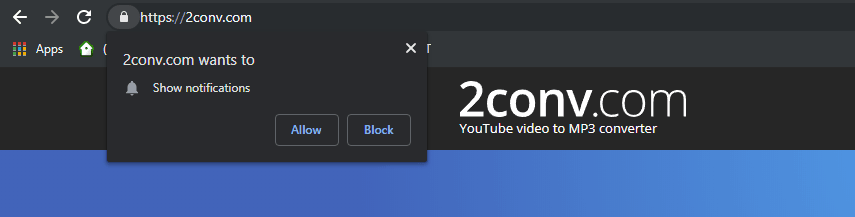
The 2conv Virus will try to trick you into subscribing to its Push notifications, do not allow it unless you want to be spammed with Pop-up ads
On this page, you will learn how to safely uninstall this annoying program and remove it from the system without facing any negative consequences. 2conv Virus is a common source of browsing disturbance for a lot of web users since this is a program that belongs to the Browser Hijacker category. It is typical for this kind of software to place some changes in the settings of your browsers’ homepage or your default search engine by replacing them without your permission, or by constantly displaying different sponsored ads, banners, pop-ups and redirect links. Therefore, it is not surprising that a lot of web users may mistake the Browser Hijacker representatives for viruses and even compare them to nasty malicious programs such as Trojans or Ransomware. To your relief, however, this is not the case – programs like 2conv, Y2mate.com or The Goodcaster are nothing more than aggressive online advertising tools that use methods like pay-per-click to promote certain sponsored websites, products or services on your screen. They are not capable of corrupting anything inside your system nor are they interested in stealing your data or blackmailing you. Yet, the way these programs advertise their sponsored ads, banners, pop-ups, and promotional messages can be very annoying. Therefore, a lot of people who end up with a piece such as 2conv on their computer prefer to uninstall it and to permanently remove its ads and browser changes.
2conv.com
The 2conv.com virus harmful effects is limited to just spamming the screen with promotional messages. Most Browser Hijackers like the 2conv.com virus are very annoying and can significantly hinder the functioning of the computer and the browser they have integrated with.
For instance, the messages that those programs constantly display may contain a redirect link to websites that may be insecure. Or the pop-ups that constantly appear on our screen may contain misleading offers that may trick us into clicking on something unreliable, which could eventually lead to an infection with a real virus, a Ransomware or some other form of malware. That’s why, basically, a system where there is a browser hijacker could be indirectly exposed to dangerous security threats if the users happen to interact with something questionable.
Fortunately, it is relatively easy to uninstall a Browser Hijacker and to remove all of its ads. All you have to do is to follow a set of manual instructions or simply use a professional removal tool that can deal with the unwanted program automatically. Of course, once you deal with it, it is important to prevent being hijacked again. Therefore, it is important to know how to keep programs like 2conv Virus away. This type of software is usually introduced in the operating system by downloading free programs and specifically free software download managers. In most cases, they go unnoticed by the users who blindly press the “next” button when running the installation without paying close attention to small text, advanced/custom settings and checkmarks that usually acquire the permission to be installed alongside the main software by default.
SUMMARY:
| Name | 2conv |
| Type | Browser Hijacker |
| Detection Tool |
Remove 2conv Pop-up Virus
You are dealing with a malware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to clean up and reset your browser to its original settings without the malware returning.
You can find the removal guide here.
For mobile devices refer to these guides instead: Android, iPhone

Leave a Comment