1PzZ3jX1zrGov2qyrMB8x3fKCrfxvTU2Tx
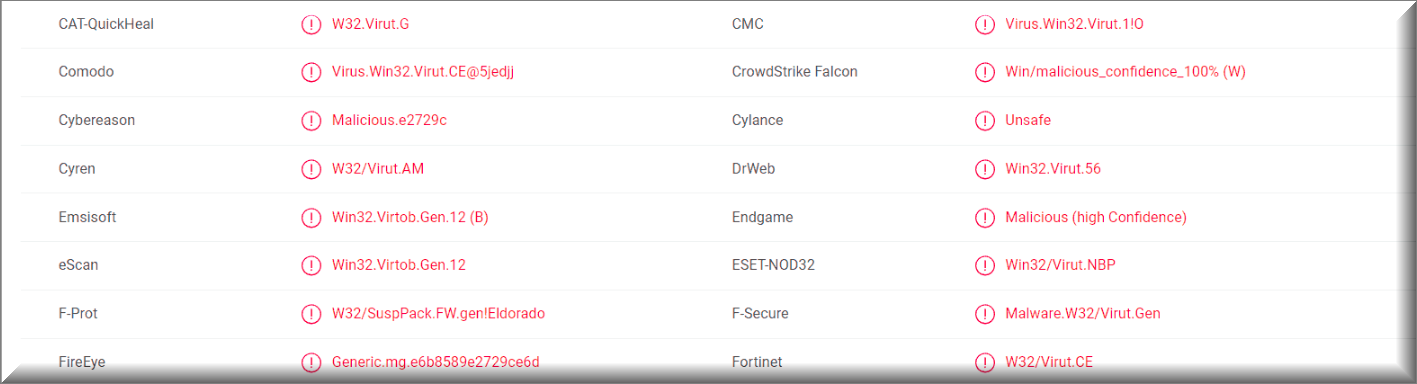
A majority of antivirus programs have detected the virus using 1PzZ3jX1zrGov2qyrMB8x3fKCrfxvTU2Tx Bitcoin Wallet. You can see the attached report from VirusTotal below:
Some of our readers reported an email that they have received, with the following message:
Subject: There is an overdue payment under your name. Please, settle your debts ASAP.
Hi!
Sadly, there are some bad news that you are about to hear.
About few months ago I have gained a full access to all devices used by you for internet browsing.
Shortly after, I started recording all internet activities done by you.Below is the sequence of events of how that happened:
Earlier I purchased from hackers a unique access to diversified email accounts (at the moment, it is really easy to do using internet).
As you can see, I managed to log in to your email account without breaking a sweat: ([Recipient’s [email protected]).Within one week afterwards, I installed a Trojan virus in your Operating Systems available on all devices that you utilize for logging in your email.
To be frank, it was somewhat a very easy task (since you were kind enough to open some of links provided in your inbox emails).
I know, you may be thinking now that I’m a genius.With help of that useful software, I am now able to gain access to all the controllers located in your devices (e.g., video camera, keyboard, microphone and others).
As result, managed to download all your photos, personal data, history of web browsing and other info to my servers without any problems.
Moreover, I now have access to all accounts in your messengers, social networks, emails, contacts list, chat history – you name it.
My Trojan virus continues refreshing its signatures in a non-stop manner (because it is operated by driver), hence it remains undetected by any antivirus software installed in your PC or device.So, I guess now you finally understand the reason why I could never be caught until this very letter…
During the process of your personal info compilation, I could not help but notice that you are a huge admirer and regular guest of websites with adult content.
You endure a lot of pleasure while checking out porn websites, watching nasty porn movies and reaching breathtaking orgasms.
Let me be frank with you, it was really hard to resist from recording some of those naughty solo scenes with you in main role and compiling them in special videos that expose your masturbation sessions, which end with you cumming.In case if you still have doubts, all I need is to click my mouse and all those nasty videos with you will be shared to friends, colleagues, and relatives of yours.
Moreover, nothing stops me from uploading all that hot content online, so all public can watch it too.
I sincerely hope, you would really not prefer that to happen, keeping in mind all the dirty things you like to watch, (you certainly know what I mean) it will completely ruin your reputation.However, don’t worry, there is still a way to resolve this:
You need to carry out a $1450 USD transfer to my wallet (equivalent amount in bitcoins depending on exchange rate at the moment of funds transfer), hence upon receiving the transaction, I will proceed with deleting all the filthy videos with you in main role.
Afterwards, we can forget about this unpleasant accident. Furthermore, I guarantee that all the malicious software will also be erased from your devices and accounts.
Mark my words, I never lie.That is a great bargain with a low price, I assure you, because I have spent a lot of effort while recording and tracking down all your activities and dirty deeds during a long period of time.
In case if you have no idea how to buy and transfer bitcoins – feel free to check the related info on the internet.Here is my bitcoin wallet for your reference: [*link removed*]
From now on, you have only 48 hours and countdown has started once you opened this very email (in other words, 2 days).
The following list contains things you should definitely abstain from doing or even attempting:
> Abstain from trying to reply this email (since the email is generated inside your inbox alongside with return address).
> Abstain from trying to call or report to police or any other security
> services. In addition, it’s a bad idea if you want to share it with
> your friends,
hoping they would help. If I happen to find out (knowing my awesome skills, it can be done effortlessly, because I have all your devices and accounts under my control and unceasing observation) – kinky videos of yours will be share to public the same day.
> Abstain from trying to look for me – that would not lead anywhere either. Cryptocurrency transactions are absolutely anonymous and cannot be tracked.
> Abstain from reinstalling your OS on devices or throwing them away.
> That would not solve the problem as well,
since all your personal videos are already uploaded and stored at remote servers.Things you may be confused about:
> That your funds transfer won’t be delivered to me.
Chill, I can track down any transactions right away, so upon funds transfer I will receive a notification as well, since I still control your devices (my trojan virus has ability of controlling all processes remotely, just like TeamViewer).
> That I am going to share your dirty videos after receiving money transfer from you.
Here you need to trust me, because there is absolutely no point to still bother you after receiving money.
Moreover, if I really wanted all those videos would be available to public long time ago!I believe we can still handle this situation on fair terms!
Here is my last advice to you… in future you better ensure you stay away from this kind of situations!
My advice – don’t forget to regularly update your passwords to feel completely secure.
There are many different kinds of Trojan Horse viruses – some target your system data, some try to spy on you, some seek to steal sensitive info from your computer and online accounts and some might even be used to silently download other harmful programs the likes of Ransomware and Rootkits on the infected computer. Here, however, we will be focusing on a specific type of e-mail Trojans that are used in phishing e-mail campaigns, which have recently become quite widespread and currently there are a lot of users who have fallen victims to these threats. One example of such a phishing e-mail Trojan Horse virus is 1PzZ3jX1zrGov2qyrMB8x3fKCrfxvTU2Tx, which will be the main topic of this article. If you have recently noticed some obscure e-mails in your inbox that claim you need to pay a certain amount of BitCoins or something bad would happen, then you likely have 17YJKh4TNBDrgFKfbjbQHCGEmZH8uvFoVp, “Drive by exploit” or “Save Yourself” inside your computer. In order to increase the chances of the scam being successful and make their e-mails be more threatening, the criminals behind this scheme usually claim that your PC has been hacked and that if you do not pay, something bad will happen to the machine. In their e-mails, the scammers might claim that some sensitive information about the user has been acquired by them and that it would be made publicly available online in order to scare the user into paying. This is somewhat similar to the way Ransomware cryptoviruses try to intimidate users into sending money to the hackers by claiming that the user’s files would stay locked if the money isn’t paid. However, the difference here is that the scammers are only bluffing and they don’t actually have any actual leverage over you.
Some more words about 1PzZ3jX1zrGov2qyrMB8x3fKCrfxvTU2Tx
The problem with having this Trojan which might potentially be inside your computer isn’t solely related to the phishing e-mails you are likely to receive if the infection has reached you. A more experienced and discerning user would easily spot the scam and ignore and delete the phishing letter. However, since the Trojan is still in the PC and because this type of malware is actually highly versatile, the malicious program might still be used to carry out some other insidious and harmful task inside the targeted machine. We already mentioned some of the common uses of a typical Trojan Horse virus at the start of this article. Note that some Trojans could get remotely repurposed to do something different from their initial task after they have already attacked a certain computer. This means that even if you do not fall for the e-mail scam, your PC and your virtual security and privacy are still not going to be safe if the malware doesn’t get removed. The sooner you ensure that all malicious data has been removed from your computer, the less time the malware would have to do some other nasty thing to your computer. Therefore, we advise you to act quickly and use the guide from this page and/or the removal tool attached to it and get rid of 1PzZ3jX1zrGov2qyrMB8x3fKCrfxvTU2Tx ASAP!
SUMMARY:
| Name | 1PzZ3jX1zrGov2qyrMB8x3fKCrfxvTU2Tx |
| Type | Trojan |
| Detection Tool | Some threats reinstall themselves if you don't delete their core files. We recommend downloading SpyHunter to remove harmful programs for you. This may save you hours and ensure you don't harm your system by deleting the wrong files. |
Remove 1PzZ3jX1zrGov2qyrMB8x3fKCrfxvTU2Tx Bitcoin Email Virus
You are dealing with a malware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to clean up and reset your browser to its original settings without the malware returning. You can find the removal guide here.
For mobile devices refer to these guides instead: Android, iPhone



Leave a Comment