Iforgot.apple.com
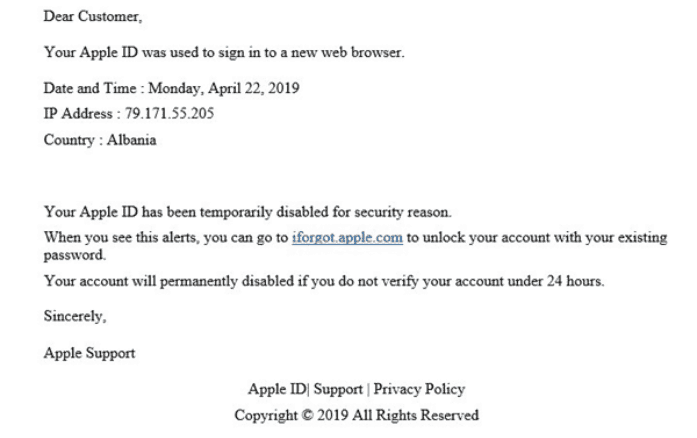
There are signs suggesting that it is a scam. Apple would address users by their name rather than with a phrase “Dear Customer”.Apple will never ever send you an email stating your account has been lockedApple will never threaten to disable an account permanently, for any reason.
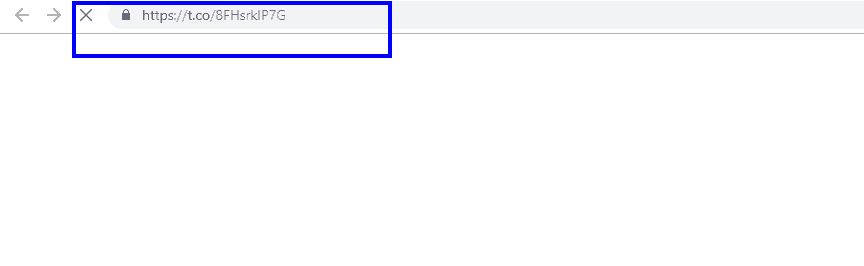
While the iforgot.apple.com website is legit, the actual url underlying that link in the email does not take you there. It takes you to: https: // t.co / 8FHsrklP7G, which is definitely not an Apple website.
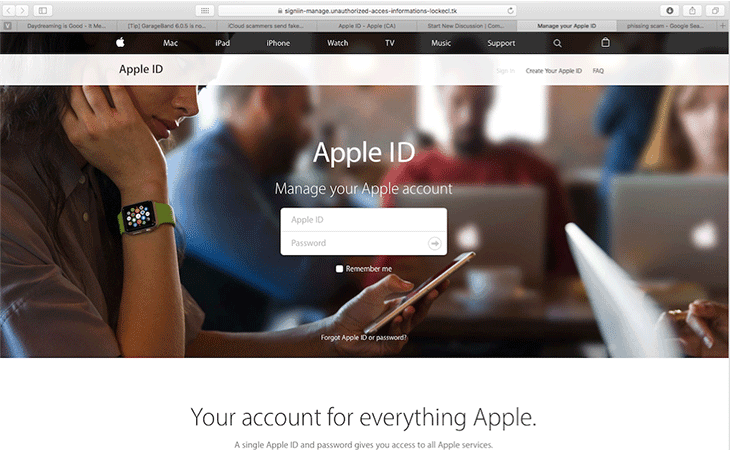
Iforgot.apple.com is simply text pointing to a URL of a fake Apple ID management website used to steal account credentials.
The site Iforgot.apple.com is legitimate if you visit it manually, but links to it or other websites can easily be forged.That link doesn’t point to Apple’s servers; in addition, if an Apple ID is locked or disabled, the owner will be told when they try logging into it instead of through email.The site is legitimate if you visit it manually, but links to it or other websites can easily be forged.
If you want your computer to be safe and if you want to decrease the likelihood of encountering Ransomware cryptoviruses, Trojans and other similar dangerous threats, then you must make sure that your browser stays clean and that it doesn’t have any questionable components in it. This may actually sound rather simple and easy to achieve – simply do not add any sketch add-ons to the browser and everything should be fine, right? In theory, yes, in practice, things can be a bit different. What we mean by that is there are many, many software pieces out there that may not be inherently harmful but could still lead to certain security issues. Such are the infamous browser hijackers like “Apple Care”, “Your Computer Is Locked”, “Apple Security Trojan Warning” with their ability to cause automatic ads generation and page-redirects, to alter the search engine service, the toolbar buttons and the homepage of popular browsers Google Chrome, Mozilla Firefox and Safari. Though these activities may not sound like much and though some users may not be all that disturbed by them, it’s important to know that the hackers on the Internet always seek to exploit even the slightest weakness in their victims’ systems. The presence of a hijacker in the main browser of the computer, for example, could be such a weakness in a way. The main problem here is the potential for the display of unsafe ads on your screen if a hijacker is present in the browser. Now, we need to point out that the hijacker apps themselves aren’t normally intended to cause harm – their goal is different and is mainly related to the generation of revenue through online advertising. Even so, the fact that there is a software component inside your browser which doesn’t really obey your commands and instead does only what its creators want it to is enough of a reason for you to want to have the offending application uninstalled.
Dealing with Iforgot.apple.com Scam
The article on this page has been written because of the recent reports about a software piece named Iforgot.apple.com Scam. According to what the users who have it in their machines say and also according to our own research, this app has most of the traits typical for a browser hijacker which is why it should be categorized as one. If you are among the many with Iforgot.apple.com Scam inside their browsers, you likely want to learn more about what methods you can use to remove this software. As we already mentioned, the presence of such an app in the system can be a potential security hazard due to the unknown sources of the ads and the page-redirects initiated by this software. You cannot know if a given advert isn’t actually linked to a site with Ransomware, Trojan Horse or Spyware infections in it. And, of course, there’s no need to mention that the sheer annoyance and obstructiveness of the ads and the changes in the browser is also a valid reason why most users would like to have Iforgot.apple.com Scam uninstalled. Therefore, without further ado, we will now give you our Iforgot.apple.com Scam removal guide:
SUMMARY:
| Name | Iforgot.apple.com |
| Type | Browser Hijacker |
| Danger Level | Medium (nowhere near threats like Ransomware, but still a security risk) |
| Symptoms | Sudden redirects to obscure pages and changes in the browser’s homepage and/or search engine. |
| Distribution Method | The hijackers like Iforgot.apple.com Scam normally rely on software bundles to get distributed. |
| Detection Tool |
Remove Iforgot.apple.com Email Scam
![]()
The first thing you need to do is to Quit Safari (if it is opened). If you have trouble closing it normally, you may need to Force Quit Safari:
You can choose the Apple menu and click on Force Quit.
Alternatively you can simultaneously press ⌘ (the Command key situated next to the space bar), Option (the key right next to it) and Escape (the key located at the upper left corner of your keyboard).
If you have done it right a dialog box titled Force Quit Applications will open up.
In this new dialog window select Safari, then press the Force Quit button, then confirm with Force Quit again.
Close the dialog box/window.
![]()
WARNING! READ CAREFULLY BEFORE PROCEEDING!
Start Activity Monitor by opening up Finder, then proceed to ![]()
Once there, look at all the processes: if you believe any of them are hijacking your results, or are part of the problem, highlight the process with your mouse, then click the “i” button at the top. This will open up the following box:

Now click on Sample at the bottom:
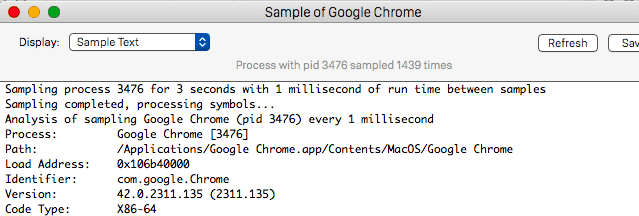
Do this for all processes you believe are part of the threat, and run any suspicious files in our online virus scanner, then delete the malicious files:

![]()
The next step is to safely launch Safari again. Press and hold the Shift key while relaunching Safari. This will prevent Safari’s previously opened pages from loading again. Once Safari is opened up, you can release the Shift key.
On the off chance that you are still having trouble with scripts interrupting the closing of unwanted pages in Safari, you may need to take some additional measures.
First, Force Quit Safari again.
Now if you are using a Wi-Fi connection turn it off by selecting Wi-Fi off in you Mac’s Menu. If you are using a cable internet (Ethernet connection), disconnect the Ethernet cable.
![]()
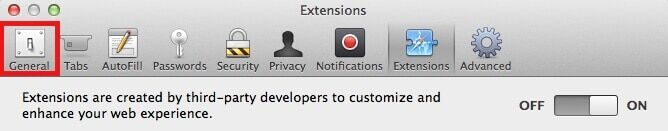
Re-Launch Safari but don’t forget to press and hold the Shift button while doing it, so no previous pages can be opened up. Now, Click on Preferences in the Safari menu,
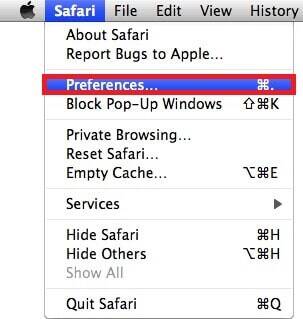
and then again on the Extensions tab,

Select and Uninstall any extensions that you don’t recognize by clicking on the Uninstall button. If you are not sure and don’t want to take any risks you can safely uninstall all extensions, none are required for normal system operation.
![]()
The threat has likely infected all of your browsers. The instructions below need to be applied for all browsers you are using.
Again select Preferences in the Safari Menu, but this time click on the Privacy tab,

Now click on Remove All Website Data, confirm with Remove Now. Keep in mind that after you do this all stored website data will be deleted. You will need to sign-in again for all websites that require any form of authentication.
Still in the Preferences menu, hit the General tab
Check if your Homepage is the one you have selected, if not change it to whatever you prefer.

Select the History menu this time, and click on Clear History. This way you will prevent accidentally opening a problematic web page again.
![]() How to Remove Iforgot.apple.com Scam From Firefox in OSX:
How to Remove Iforgot.apple.com Scam From Firefox in OSX:
Open Firefox, click on ![]() (top right) ——-> Add-ons. Hit Extensions next.
(top right) ——-> Add-ons. Hit Extensions next.

The problem should be lurking somewhere around here – Remove it. Then Refresh Your Firefox Settings.
![]() How to Remove Iforgot.apple.com Scam From Chrome in OSX:
How to Remove Iforgot.apple.com Scam From Chrome in OSX:
Start Chrome, click ![]() —–>More Tools —–> Extensions. There, find the malware and select
—–>More Tools —–> Extensions. There, find the malware and select ![]() .
.
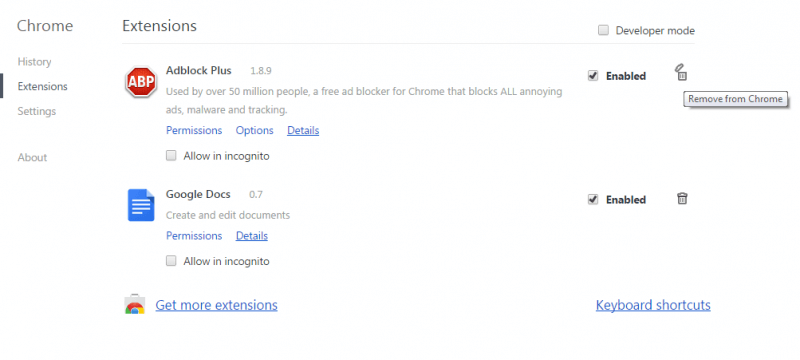
Click ![]() again, and proceed to Settings —> Search, the fourth tab, select Manage Search Engines. Delete everything but the search engines you normally use. After that Reset Your Chrome Settings.
again, and proceed to Settings —> Search, the fourth tab, select Manage Search Engines. Delete everything but the search engines you normally use. After that Reset Your Chrome Settings.
If the guide doesn’t help, download the anti-virus program we recommended or try our free online virus scanner. Also, you can always ask us in the comments for help!

Leave a Comment