Righ
Righ is a malware virus of the Ransomware family and it is able to stop you from opening, editing, or using any of your files until you agree to pay a ransom. Righ can be removed but its removal doesn’t release the locked files.
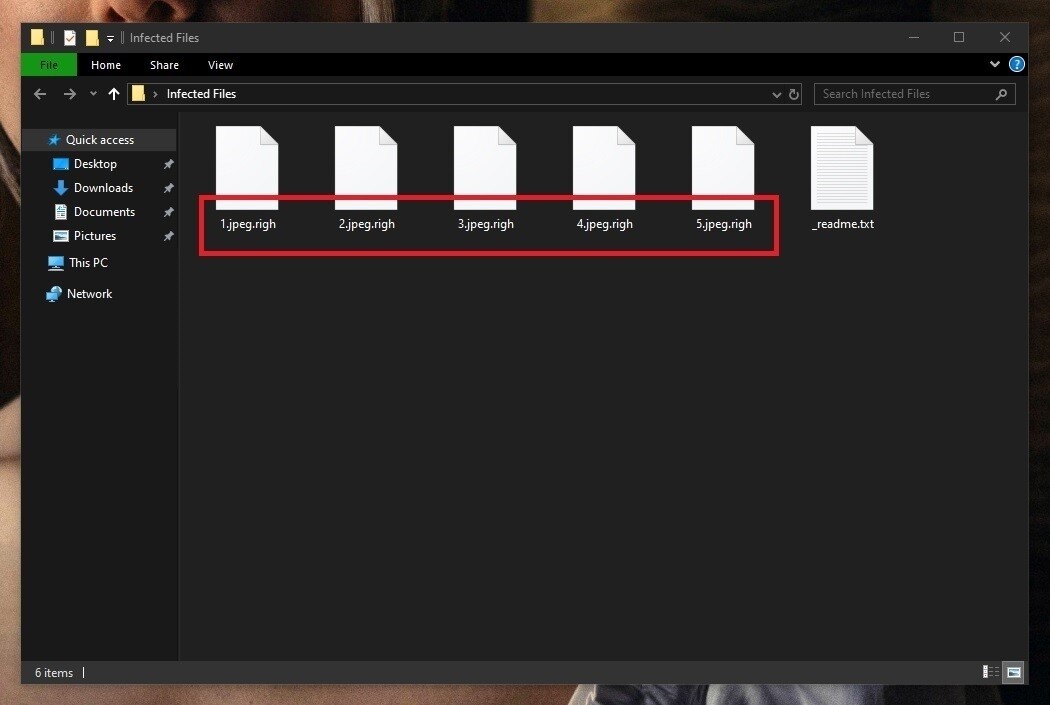
The Righ Virus will encrypt your files
However, it is still crucial that you eliminate this malicious computer virus. Righ is a Ransomware virus that can lock both the files that are currently in your computer and the files you may create or download in the future. Therefore, Righ must be removed from the PC to prevent further encryption of important data. In addition, if the virus is no longer in your computer, you would have the freedom to use backups to restore the locked files. The Righ file encryption is a process that typically can’t be reverted without the corresponding private key. However, you could circumvent the Righ file encryption if you have backups of your files available on other devices or in cloud storages. Here, again, it is really important to first remove the virus. Otherwise, you may lose the backup data because it may get encrypted the moment you connect your computer to the backup. Righ is a stealthy Ransomware that stays hidden until it locks up your valuable data. Once Righ completes the encryption, however, it automatically reveals its presences and it is at that moment when you should start the process of removing it. Hopefully, with the help of our guide available on this page, you should be able to make quick work of this virus and clean your computer so that you can start the process of trying to recover your data.
If you have this Ransomware in your computer at the moment, then you probably can’t open most or all of your files that are stored on the infected machine. If the files this virus has encrypted aren’t that important to you, it’s best to simply remove the virus and remember to better protect your computer in the future. Removing the Ransomware is actually the easy part when it comes to dealing with this sort of threats and it’s usually quite manageable. You can find a set of removal instructions down below and we advise you to follow them once you are through this article.
The Righ virus
The Righ virus is a hazardous computer program that belongs to the infamous Ransomware family of viruses. The Righ virus locks important user data in order to gain leverage and then blackmail the victims for a ransom payment they must send to free their files.
What if the locked files are valuable to you in one way or another? Well, in such a case you have several options. One of those options is, of course, to pay the ransom sum required by the hackers behind Righ. Doing so, however, guarantees nothing other than the loss of a sizeable amount of money on your side. You can send the full ransom amount and still not get the private key that can set your files free. After all, the hackers who have created Righ, Msop, Hets and who are now using it to blackmail you are criminals who can’t be trusted, especially when money is involved. This is why the majority of the security experts advise against the ransom payment and we too share subscribe to this advice.
The Righ file extension
The Righ file extension is a short sequence of characters that is added to the name of each file Righ encrypts. The Righ file extension can’t be removed manually by the user and only goes away once the file gets decrypted.
The other option is to remove the malware on your own (or maybe with the help of a reliable anti-malware program) and then try to restore your file using alternative means. For instance, if you have an external device with backup copies of your files, you should use it to restore your data by copying it back to the computer (but only after the Ransomware has been removed). In this regard, it is always a good idea to check all other devices, online cloud storages, and other Internet accounts where there may be some forgotten copies of the important files that the Ransomware has locked. If, after all, you don’t’ find any backups, you can also resort to the recovery section of the removal guide for Righ – the suggestions there may not always work but they are still a preferable alternative to the ransom payment.
SUMMARY:
| Name | Righ |
| Type | Ransomware |
| Detection Tool |
Remove Righ Ransomware
Search Marquis is a high-profile hijacker – you might want to see if you’re not infected with it as well.

Leave a Comment