This page aims to help you remove TFlower Ransomware Virus for free. Our instructions also cover how any file encrypted by TFlower can be recovered.
TFlower is a very malicious program that belongs to the infamous Ransomware cryptovirus category. This infection is among the hardest to detect and because of that it is very effective in its malicious attack. As a typical cryptovirus, TFlower is pretty straightforward in its activities and follows a specific agenda. The goal of the infection is to sneak in the system without being noticed and to place a complex encryption to a number of files that it considers as important to you. Once it locks them up, the malware will immediately place a ransom-demanding notification with the help of which it will blackmail you to pay a certain amount of money in exchange for the unique access key which can reverse the applied encryption. Without applying that corresponding key, you will be unable to open or use any of your precious files, no matter what software you may try to use as help.
So, if you have some important work-related documents, personal projects, spreadsheets, images, audios or videos of a great value, you would be prompted to purchase that key or lose access to them forever.
The hackers who stand behind the malware would immediately offer you to pay a certain amount of money to obtain it, and will provide you with concrete instructions on how to do that. They will place a ransom-demanding notification on your screen to make sure that you know exactly what you have to do in case you want to make the payment.
TFlower Ransomware
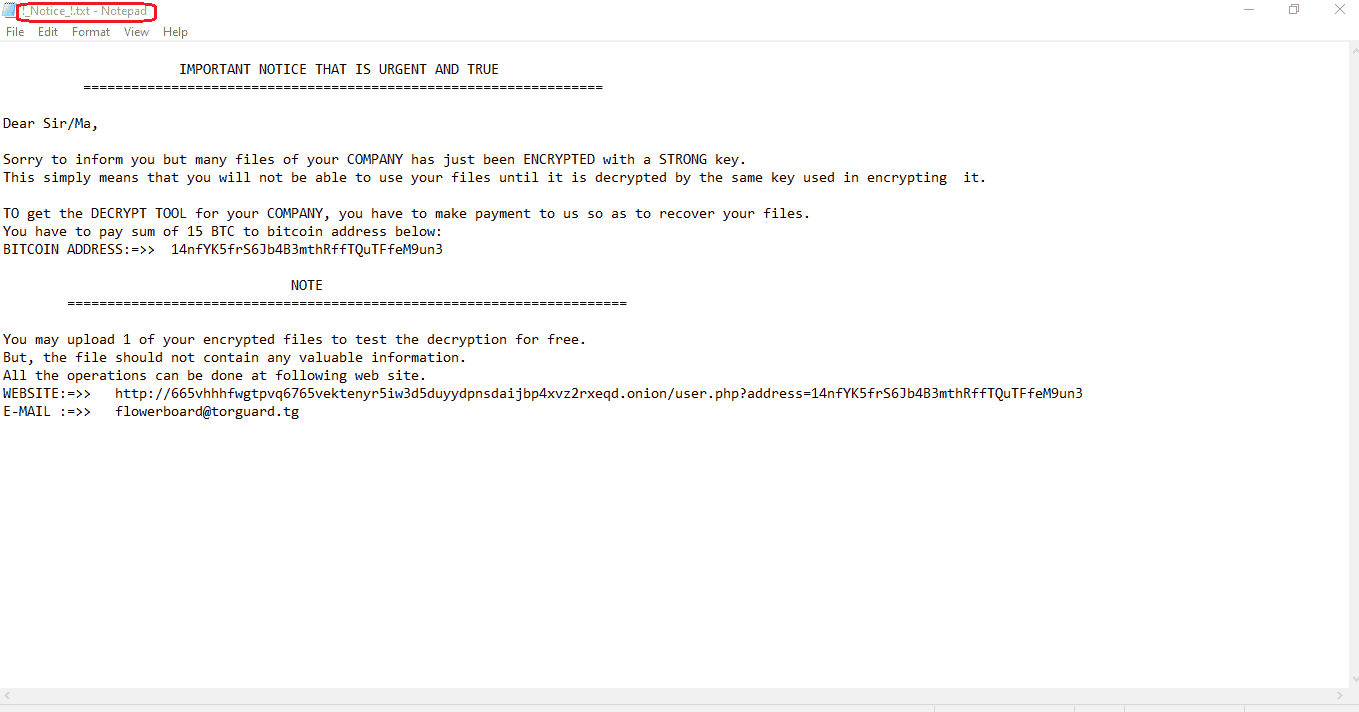
The TFlower Ransomware will leave you this message in a !_Notice_!.txt file explaining what you have to do to pay the ransom.
If you agree to send them your money, however, you should be aware of the fact that there is no way of getting them back, regardless of how effective the decryption key will be. What is more, there isn’t really a guarantee that sending the money would result in you receiving the decryption key. All you have to do is hope for the best. Whether the hackers will keep their promise and really send you what you need for the decryption of your files, and whether that key will really work is another story. All this makes it a rather risky to send your money to such criminals.
Sadly, there aren’t many other options once you have been infected with a cryptovirus. Therefore, if you don’t want to risk your money and want to explore some alternative solutions, the first thing we would advise you is to remove the Ransomware from the computer. You can use the instructions in the removal guide below as a starting point or simply run a system check the professional TFlower removal tool attached to the guide.
How to deal with the TFlower file encryption?
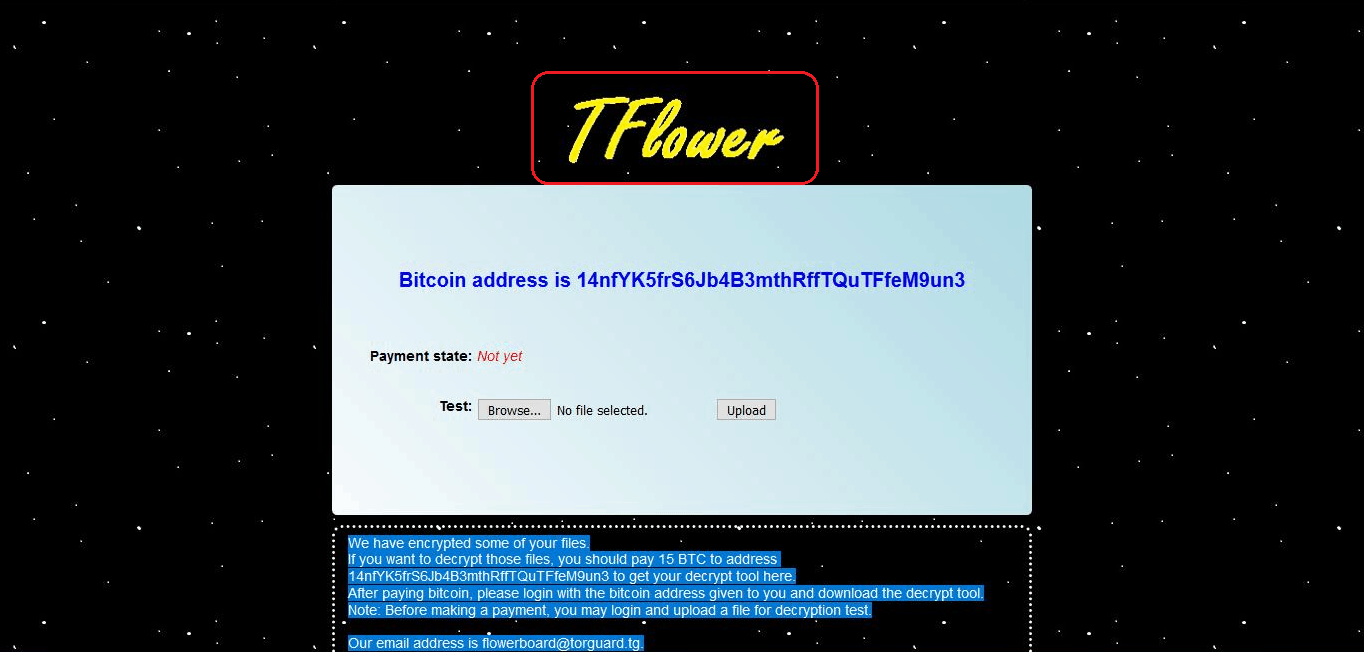
When you visit the site given to you by the ransomware it will have this written in it.
Typically, files encrypted by ransomware such as Format or Nelasod have their file extension changed so that no software can recognize and use them, but the TFlower Ransomware that does not encrypt files in any specific extension. Therefore, full data-recovery is only possible with the help of external data backup copies. Still, to get back some of the encrypted information, you may give a try to the file-recovery methods listed in the second part of the guide. Make sure, however, that you have first removed the infection otherwise you may risk the encryption of everything you manage to recover.
SUMMARY:
| Name | TFlower |
| Type | Ransomware |
| Detection Tool |
TFlower Virus Removal
Search Marquis is a high-profile hijacker – you might want to see if you’re not infected with it as well.
You can find the removal guide here.

Leave a Comment