*Source of claim SH can remove it.
PC Accelerate
PC Accelerate is a potentially unwanted program (PUP) that is promoted as a system optimization tool. Frequently linked with other PUPs like Altruistic and Taskbarify, it claims to improve computer performance but primarily operates by flagging non-existent or trivial system issues. These exaggerated alerts are strategically crafted to create a sense of urgency, prompting users to opt for its premium version. Users have reported persistent and forceful notifications encouraging this upgrade, so, despite its promotional claims, the intrusive nature of the PC Accelerate alerts raises concerns. Those in search of a reliable system optimizer are advised to approach the program and its notifications with caution and explore established and more transparent alternatives available in the market.
How to delete PC Accelerate?
To delete PC Accelerate from your device, you’ll need to navigate through your system settings and programs, locating the software in question and initiating the uninstallation process. Additionally, it’s recommended to explore relevant folders and files associated with PC Accelerate and remove them to ensure a thorough cleanup. A visit to the registry editor may also be necessary to delete any lingering entries but be cautious during this process to avoid unintended deletions to ensure a smooth removal of the software from your device.
What is PC Accelerate?
PC Accelerate is a potentially unwanted app that employs various distribution methods to infiltrate systems. Often, it is found on popular free software downloads through “bundling” – a tactic where it’s packaged alongside legitimate software and installed without the user’s explicit consent. Additionally, misleading advertisements or pop-ups may promote it as a beneficial tool, enticing users to download it. The software might also be promoted through fake system alerts claiming the user’s computer has performance issues.
How to get rid of PC Accelerate?
If you want to get rid of PC Accelerate, you need to use a reliable and reputable antivirus software that can scan your device for any traces of this and other PUPs, and remove them completely and safely. You can also use a manual method to get rid of PC Accelerate, but this method is not recommended, as it can be risky and complicated. You need to have some technical knowledge and skills, and be careful not to delete any important or legitimate files or registry entries.
Is PC Accelerate a virus?
Referring to PC Accelerate as the “PC Accelerate Virus” is misleading, as this software is not intended to corrupt the computer and its data. The use of the term “virus” is more of a casual description due to the software’s intrusive and suspicious actions. The main concern of users who have it installed on their systems stems from the fact that the app’s questionable prompts often make them think that their system may be at risk and prompt them to click on deceptive notifications. However, it’s important to note that the “PC Accelerate Virus” doesn’t possess the self-replicating features present in true viruses.
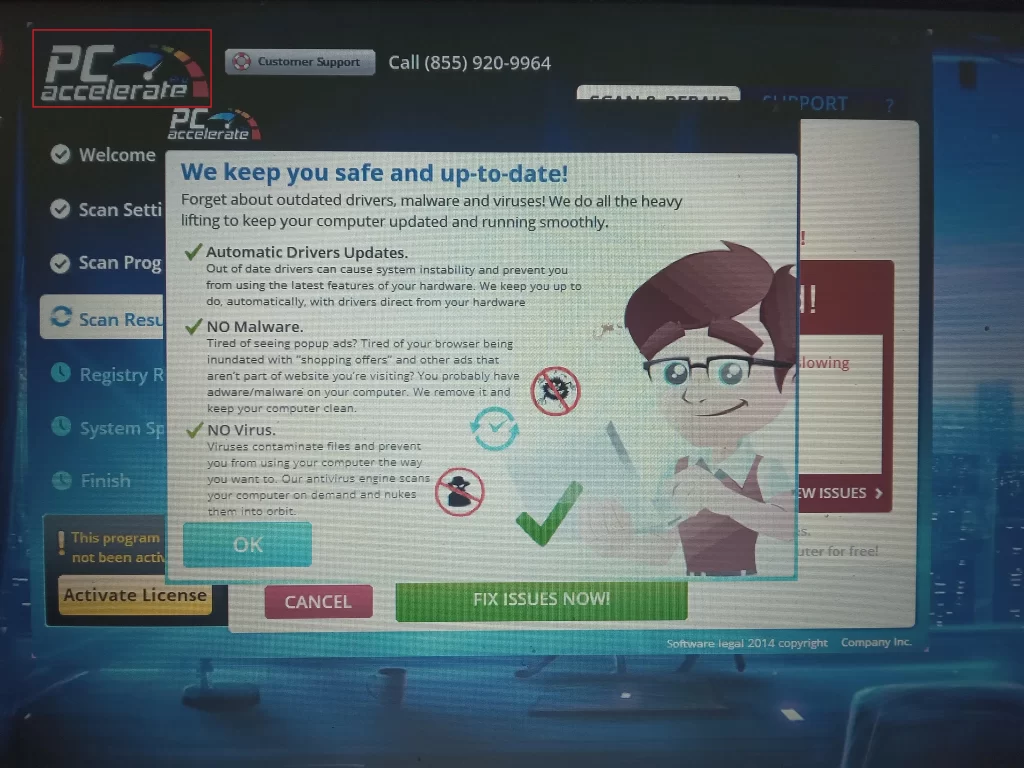
PC Accelerate Pro uninstall
PC Accelerate Pro represents the upgraded or premium version of the basic PC Accelerate software. However, the experience for users who opt for this premium version may not align with the promised enhanced features. Instead of the anticipated benefits, users might encounter a surge in the consumption of system resources, leading to potential slowdowns or performance issues. Additionally, the use of PC Accelerate Pro could introduce an increased level of intrusiveness, marked by aggressive pop-up notifications and optimization alerts appearing on the user’s screen. This behavior can be disruptive, affecting the overall user experience and causing frustration. Therefore, it’s crucial for users to be aware of these potential drawbacks when considering the premium version and think about PC Accelerate Pro uninstall options in case they don’t get the promised advantags.
How to uninstall PC Accelerate
If you’ve attempted to uninstall PC Accelerate, you might have noticed how challenging and frustrating this process is. Despite using the program’s uninstaller, users often find that this action alone doesn’t completely eliminate the software. The root of the problem lies in the alterations made by the app within the system. These changes enable the PUP to persist even after what seems like a successful uninstallation. PC Accelerate can embed files, registry entries, or processes that remain concealed and active, allowing it to either reinstall itself or continue impacting the system’s performance. Consequently, to uninstall PC Accelerate successfully, users frequently need to go beyond the standard uninstaller, resorting to specialized removal tools or manually locating and removing residual components.
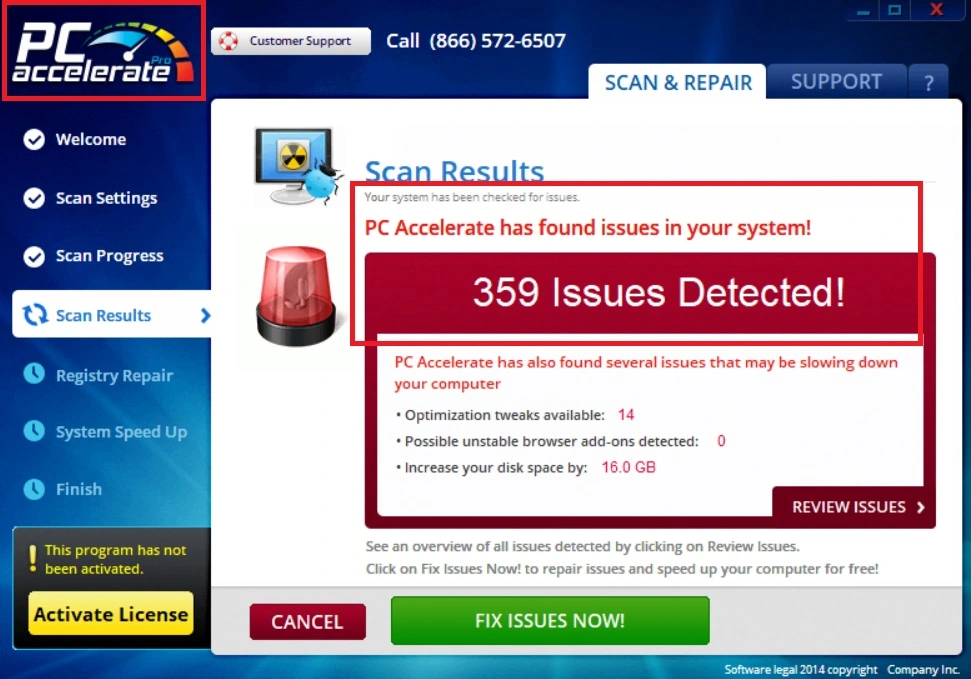
The PC Accelerate pop up
The PC Accelerate pop up is an alert that claims that your device is slow, infected, or outdated, and that you need to download and install the PC Accelerate Pro software to fix it. The PC Accelerate pop up can also display other messages, such as “Your device is at risk”, “Your device needs optimization”, or “Your device has errors” and can also show a fake scan or a fake countdown to persuade you to click on it.

Unfortunately, this pop up is not helpful and is designed to trick you into downloading and installing the paid version of the software, which can display more unwanted ads, pop-ups, banners, and notifications on your device, that may contain links to sponsored websites or downloads to PUPs like QuickTune Computer.
Remove PCAcceleratePro
Users who have tried to remove PCAcceleratePro share an effective approach that involves a combination of manual removal steps, and the assistance of professional removal programs. The need for this dual approach suggests that PCAcceleratePro can be particularly persistent and challenging to completely eliminate through manual efforts alone. Therefore, the use of specialized removal tools or programs designed for tackling such stubborn programs becomes crucial in ensuring a thorough and effective cleanup. Moreover, users express confusion and concern about how PCAcceleratePro infiltrated their systems without their knowledge. Investigations into this matter reveal that the primary method of distribution is through software bundling. This means that PCAcceleratePro is often bundled with other seemingly legitimate software during the installation process, and users may inadvertently agree to its installation by overlooking or accepting terms within the software bundle.
SUMMARY:
| Name | PC Accelerate Pro |
| Type | PUP |
| Detection Tool |
*Source of claim SH can remove it.
How to remove PC Accelerate
To Uninstall PC Accelerate Pro, you can find the program entry in your Control Panel and try to delete it from there:
- Start with pressing Winkey + R and type appwiz.cpl in the search field.
- Select OK and when a list of programs opens, find in it the entry for PC Accelerate Pro and click on it.
- Click on the Uninstall option from the top and follow the uninstallation wizard steps.
- Once the uninstallation completes, check for other suspicious programs, potentially related to PC Accelerate Pro, and uninstall them too.

This quick removal method could help you get rid of the unwanted program, but it’s also possible that this won’t be enough to fully remove PC Accelerate Pro. If that’s your case and PC Accelerate Pro is still present in the system, please, proceed to the more advanced steps shown below and complete all of them to delete all system entries and files that the unwanted program may have left behind.
How to Remove PC Accelerate Pro from Windows 10
To Remove PC Accelerate Pro from Windows 10, you must find and quit the PUP process and delete its files. Also, to make sure that PC Accelerate Pro is fully removed from your Windows 10 computer, you should delete the Registry entries for the unwanted program.

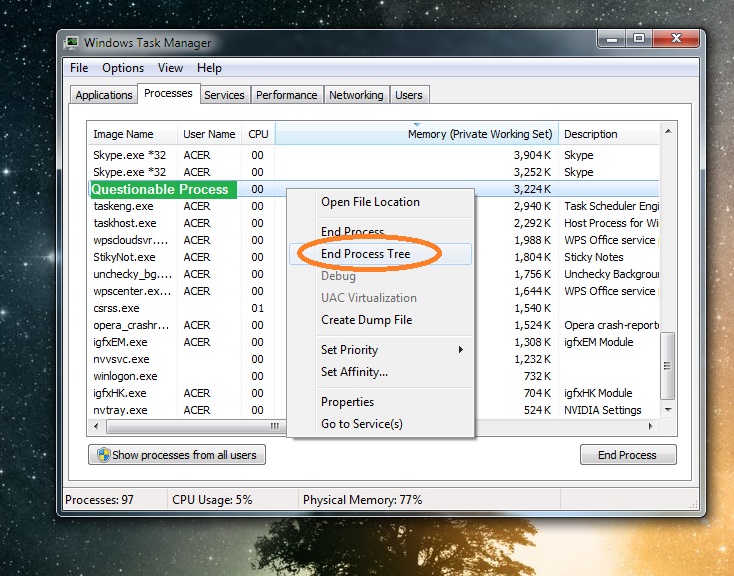
The first thing you should do is try to find the processes for PC Accelerate Pro and quit them from the Task Manager:
- Start the Task Manager (you can do that by pressing Ctrl + Shift + Esc or by searching for “task manager” in the Start Menu and clicking on the first item).
- Select Processes, and try to find a process named PC Accelerate/PC Accelerate Pro (or something similar). If you can’t find this, look for other questionable processes with unfamiliar names and high use of system resources (RAM memory and CPU).
- If you find a process named PC Accelerate Pro or something close to that, right-click on it, select Open File Location, select the process again with the right-click of the mouse and this time opt for End Process Tree.

Next, delete the File Location folder that you got sent to.
If you didn’t find a process named PC Accelerate Pro but have found another one that looks potentially unwanted, look up its name on the Internet and see what info comes up – if it seems the process is run by a legitimate program or by the Windows OS, leave it be and look for another suspicious one.
If there’s anything in your online search that suggests the process may be linked to PC Accelerate Pro or to another unwanted program, go to the process’ File Location and this time use the following free online scanner to test all files stored in that folder for malicious code:

In case any of the files are flagged as hazardous by our scanner, you must End the process tree of the suspicious process from the Task Manager even if the process has a name different from PC Accelerate Pro. After that, also delete the entire location folder where the files for that process are stored.

*Source of claim SH can remove it.
Now you must boot your PC into Safe Mode so that any unwanted PC Accelerate Pro processes you missed during the previous step won’t interrupt you throughout the rest of this guide since, while in Safe Mode, your computer’s system won’t allow suspicious third-party processes to run automatically. If you don’t know how to access Safe Mode, follow the link we’ve provided to a guide with detailed instructions on the matter.

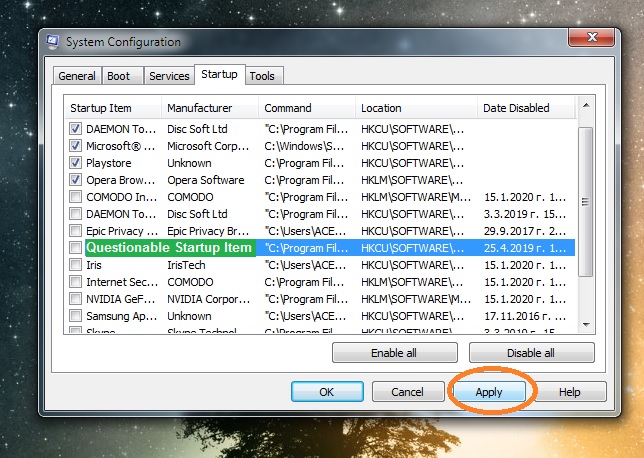
You should also check the Startup items of your computer and disable anything potentially related to PC Accelerate Pro:
- Press the Windows key and R key again and this time type msconfig and hit Enter.
- Open Startup in the window that appears on your screen and see if there is an item in the list of Startup items named PC Accelerate Pro.
- If there is one, disable it by removing the tick from its checkbox.
- If there isn’t a PC Accelerate Pro item, look for other ones that look like they shouldn’t be allowed to start automatically when Windows loads – those could be items with unfamiliar names or ones with unknown manufacturers – disable anything that doesn’t seem trustworthy.
- Once you disable all questionable entries that may be linked to the PC Accelerate Pro PUP, click on OK to exit the System Configuration settings and then proceed to the next step.

*Source of claim SH can remove it.
The Hosts file oftentimes gets hijacked by unwanted third-party apps like PC Accelerate Pro, so it’s worth checking that too:
- Type (paste) this in your Start Menu and hit Enter: notepad %windir%/system32/Drivers/etc/hosts.
- Check the bottom of the text, right where it says LocaHost. If you see lines of text below that, this means that the Hosts file has been manipulated by third-party software.
- Copy everything that’s after Localhost and paste it in the comments – we will have a look at it and tell you if it’s from PC Accelerate Pro.
- If we tell you that the text you’ve sent us is from the PUP, you will have to delete that text from your Hosts file and then save the changes made you’ve made to it.

Important!: To complete this final PC Accelerate Pro removal step, you must make certain changes in the computer’s Registry by deleting any items that may be related to the unwanted program. If you end up deleting something that you shouldn’t, you could damage your system, so it is critical that you only delete Registry items if you are certain that they must be removed. In case of uncertainty, make sure to request our aid through the comments section below.
The last thing you must do to make sure that there’s nothing left from PC Accelerate Pro on your PC is to clean the Registry entries it has added in your system’s Registry.
- Start by opening the Start Menu, typing regedit, and clicking on the regedit.exe file.
- Your OS will demand Admin permission to start the Registry Editor so click on Yes to confirm this.
- When you are in the Registry Editor, press together the Ctrl and F keys from your keyboard and type PC Accelerate Proin the search box.
- Press Enter to initiate the search and then if a result is found, delete that item.
- Repeat the search to find the next related item and delete that one too – keep doing this for as long as there are items in the Registry related to PC Accelerate Pro.
- Once the search stops yielding results, expand the folders from the sidebar to the left to navigate to the following three locations:
- HKEY_CURRENT_USER > Software > *Folder with an unusual name*
- HKEY_CURRENT_USER > Software > Microsoft > Windows > CurrentVersion > Run > *Folder with an unusual name*
- HKEY_CURRENT_USER > Software > Microsoft > Internet Explorer > Main > *Folder with an unusual name*
- Once you get to those locations, see if there are folders in them that seem out of place – such would be ones with unusually long names and/or with names that consist of randomized characters.
- Delete any questionable folders that you may find in those Registry locations. If you are unsure if a specific item(s) is related to PC Accelerate Pro and you don’t know whether to delete it, ask us in the comments first and proceed with the deletion only if we confirm that the item(s) should be removed.
Final Notes
This PC Accelerate Pro removal guide should help most of our readers to eliminate the unwanted program without any trouble. However, in rare cases, it is possible that PC Accelerate Pro manages to remain in the system even after one completes all of the instructions we’ve posted here. If this happens to you, remember that you can always try the removal tool present on this page. It will quickly find whatever’s left of the PC Accelerate Pro PUP on your PC and delete it for you. It will also keep your system safe and protected from other unwanted programs as well as from all types of harmful malware.

I have the virus but all it is doing is slowing down my laptop.
It worked for me.
thanks so much! follow your instruction, i successfully removed the damn PC accelerate from my computer!
on the processes of my window 10, it is named “MarSpeed”,
not PC Accelarate.
Just as a heads up, this app didn’t appear in my programs and features at all, and while showed PC Accelerate when running, the exe was actually PerecSpeedup. You might need to search for that, as well as RPerecSpeedup and RSpeedup
Thank you for your feedback Dan Jay.
My file was called AWAP