XCX
XCX is a highly dangerous malware that causes a variety of problems inside the computer that it compromises. Security researchers classify XCX as a Trojan Horse due to its stealthy infection tactics and unpredictable behavior.
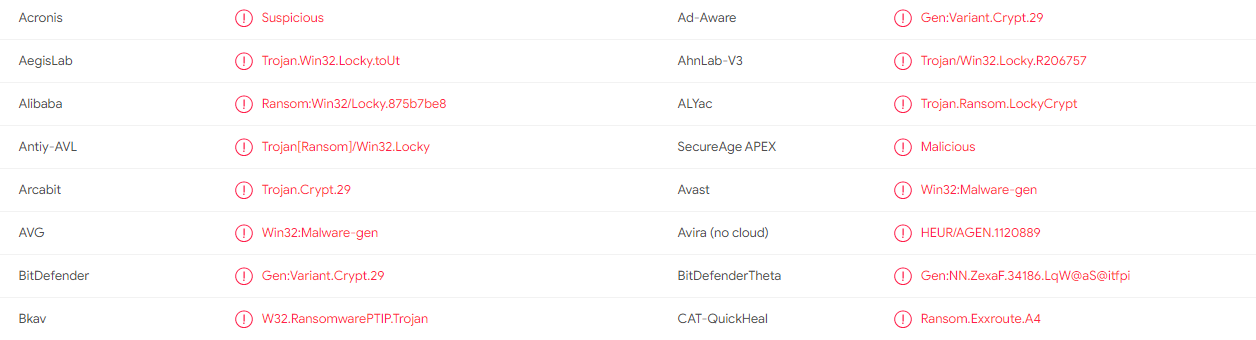
MUltiple VirusTotal scanners recognize XCX as a threat.
In case that you landed on this page because you have detected XCX inside your computer, below this article there is a free removal guide with comprehensive instructions on how to identify and remove this Trojan-based malware from your computer. And if the instructions there are not enough, or you simply need some quicker and professional assistance, the guide contains a link to a highly powerful anti-malware application that will handle the infection automatically. But before we get to this, we have to first provide you with some more information about the Trojan Horse infections and their malicious capabilities so that you are better prepared to deal with them in the best possible way.
One of the most typical features of Trojans like XCX, Presenoker and Wup.exe is that they are much stealthier than most other malware that you’ve heard about – ransomware, rootkits, spyware etc. While the ransomware or spyware virus is typically very basic and its malicious potential is very restricted to a single harmful action, Trojans are renowned for their multipurpose abilities.
Most members of the Trojan Horse group can effectively perform everything from data theft, system destruction and software corruption to providing full remote control over the computer to online hackers and crooks. Inserting other malware programs and starting different harmful activities in the background of the system are two more malicious uses of infections like XCX.
The XCX Virus
The single presence of the XCX Virus inside the computer means that you may become a victim of a variety of criminal deeds. That’s why it should be your top priority to remove the XCX Virus if you want your machine to be safe.
Unfortunately, detecting the Trojan can be the biggest challenge of all. The reason is XCX and the majority of other Trojan Horse infections are threats that cannot really be distinguished from the regular and harmless content that you interact with every day. The hackers may distribute their malicious creation via intriguing web offers, pop-up messages, different site-links and other types of web materials.
For example, if you are not cautious enough while surfing the web, you can possibly make the mistake of opening an infected attachment that can inject a Trojan inside your computer. A malicious executable may also be sent directly to your email address in the form of a spam message or an attachment. The same could happen if a cracked piece of software, a pirated application or some low-quality add-on is downloaded on your machine from a sketchy website.
That’s why sticking to reputable web locations and reliable download sources is important when it comes to preventing close encounter with viruses and malware. Keeping an eye on your system’s behavior is also a good idea since, sometimes, increased RAM and processor usage along with frequent crashes and error messages may indicate an invasion by a Trojan. However, as the symptoms may not always be present, your best bet is to install an anti-virus program that can protect your computer and identify possible malware instead of you.
SUMMARY:
| Name | XCX |
| Type | Trojan |
| Detection Tool |
XCX Virus Removal
You are dealing with a malware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to clean up and reset your browser to its original settings without the malware returning.
You can find the removal guide here.

Leave a Comment