Zwer
Zwer is a malware program used for extortion that can deny its victims access to their files. Zwer asks for a ransom payment once it locks the targeted files and unless the demanded sum is paid, the data is to remain inaccessible indefinitely.
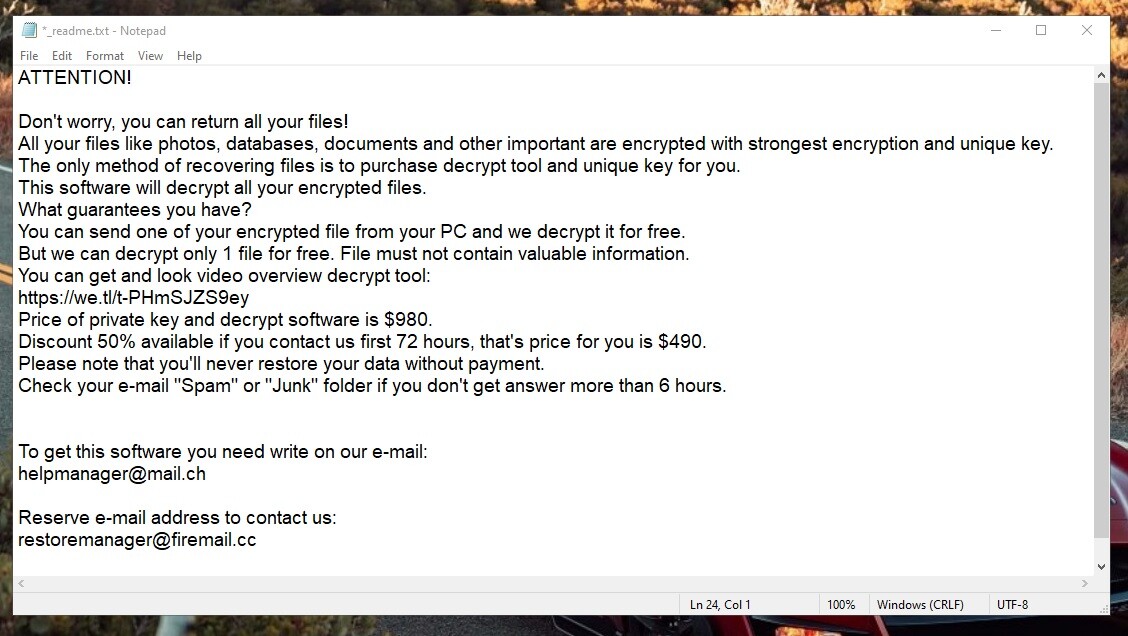
The Zwer Virus will show you this message.
Extortion schemes that involve the use of a Ransomware viruses like Zwer, Repp or Nlah are very common and millions of users fall victim to them every week. Currently, Ransomware, is one of the most widespread types of computer malware and even though it has been around for quite some time now, experts are still struggling to find ways to counteract new infections of this type.
The main factor that makes Ransomware so tricky to deal with lies in the method used for the locking of the targeted files. Maybe you’ve heard about the term file encryption in the past. This is an advanced form of data protection. When used on a certain file, the encryption makes the file inaccessible to anyone but the person who has a special digital key in their possession. This key is unique and can be applied only to the encrypted files that are present on a certain computer. The decryption key won’t work on encrypted files that are stored on another machine even if the encryption type that keeps them locked is the same.
The Zwer virus
The Zwer virus is Ransomware that uses this advanced file-locking method known as encryption to render its victims’ files inaccessible. The Zwer virus then demands a ransom in exchange for the matching access key that is in the hackers’ possession.
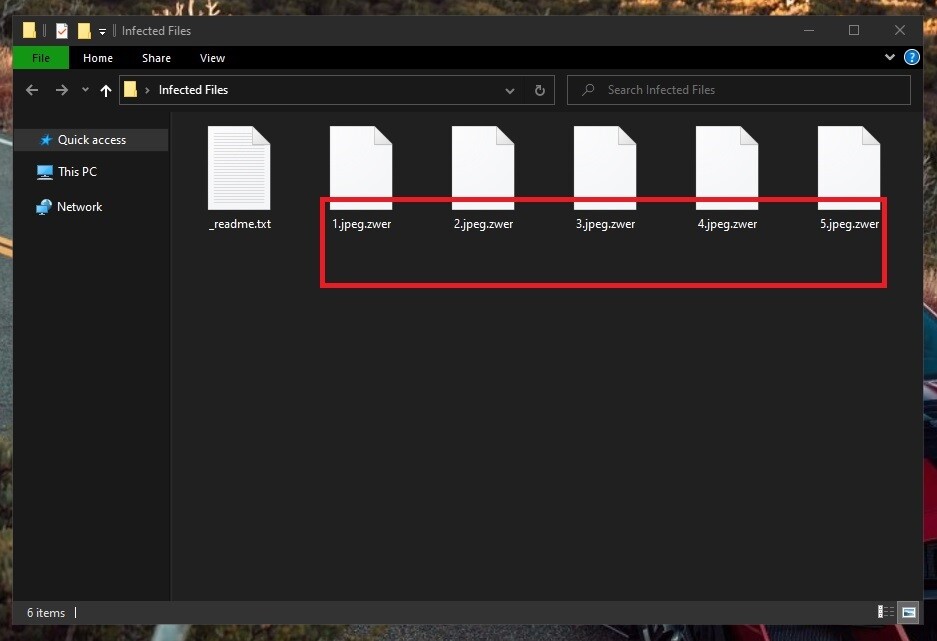
The Zwer Virus will encrypt all of your files.
Obviously, if the files kept on your computer that are now unavailable due to an attack by Zwer are highly valuable to you, you might be tempted to opt for the ransom transfer. However, doing so may not improve your situation and may worsen it instead. The hackers don’t care about the future of your data and so they could easily accept the payment without helping you restore your data. This is why most experts are in agreement that the payment should not be made unless all other options available to the Ransomware victim have been exhausted.
The Zwer file decryption
The Zwer file decryption is the opposite of the encryption process that this virus uses to lock important user files. The Zwer file decryption can usually be completed only if the user possesses the corresponding decryption key, yet there may be certain alternative options.
In the next lines, you will learn a possible way to get Zwer removed from your system. While this won’t release the files, it will give you the opportunity to try some potential recovery solutions that may get some of your files back to their normal accessible state. Also, if you have a data backup on an external device, now would be the time to use it. Just make sure to first remove Zwer with the help of our instructions or else you may end up getting the backup copies encrypted as well.
SUMMARY:
| Name | Zwer |
| Type | Ransomware |
| Detection Tool |
Zwer Ransomware Removal
You are dealing with a ransomware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to decrypt and recover your encrypted files (if it is currently possible).
You can find the removal guide here.

How to decrypt the files which are attached by .zwer extension
Hi Apoorv,
you can go to How to Decrypt Ransomware and follow the instructions there.