Gestyy.com
Gestyy.com is a browser hijacker disguised as an extension for Chrome, Firefox, or Edge. Gestyy.com hijacks the settings of the homepage, the new tab page, or the search engine of the infected browser, and starts to initiate page-redirects to different websites.
A Browser Hijacker (Fuq.com, Gohoi.com) is an app that you probably don’t want in your computer due to some of the things it could do. Usually, an application of this type would get installed inside your browser and would try to alter it in ways that benefit the hijacker’s creator. The main purpose of this sort of program is online promotion – they seek to advertise different sites, services, and products on your screen. The more successful their promotional activities are, the higher the income that the hijacker’s creator would earn.
Usually, the hijacker will introduce changes to some of the elements in your browser. A new homepage address might replace the one you are used to and your search engine may also get modified to better serve the agenda of the hijacker. Also, sudden page-redirects are almost guaranteed if you have an app of this category in your Chrome, Firefox, Safari or Edge browsers. As we said, it’s all done with the aim of promoting something in order to generate revenue. However, these advertising activities oftentimes come at the expense of the users’ undisturbed browsing experience, and it is because of this that hijackers such as the newly reported Gestyy.com are seen as unwanted.
A typical example of a potentially unwanted program is the Segurazo Antivirus.
The Gestyy Virus
The Gestyy Virus is an unwanted software app that resembles a browser add-on and is known for rerouting the user’s traffic to advertising-heavy sites. The Gestyy Virus can be installed in Chrome, Firefox, and other browsers and it can change their settings without permission.
Speaking of Gestyy.com, this is among the latest representatives of its respective software category and if you have it in your system at the moment, you are probably wondering how you could get it removed. You may have already tried to uninstall this app without any success or you may have been able to temporarily remove it from the affected browser only to see it return to bother you the next time you start a browsing session. This is to be expected from an app of the hijacker category, as these programs are specifically designed to have difficult uninstallation. In most cases, users need help with the elimination of these apps, but the good news is that we can offer you such help on this page. Our steps in the guide below will share with you the information you will need to get rid of the unwanted software and restore the normal settings of your browser.
Gestyy.com, and other similar apps, are certainly not as dangerous as Ransomware, Spyware, Worms, or Trojans. Here, we aren’t talking about an actual virus intended to harm your system or to corrupt oyur data. Most hijackers lack any actual malicious abilities as their purpose isn’t to cause harm. However, this doesn’t mean that Gestyy.com can be regarded as a perfectly safe app. A problem with hijacker such as this one (other than their intrusive and disruptive nature) is the chance to get exposed to real online dangers if you keep such software in your computer. Sometimes, some of these redirects, banners, or ads that Gestyy.com might show on your screen may not be linked to what they seem to promote. Instead, they might be ads that have been “hijacked” by hackers and used to redirect users to phishing sites, or pages filled with Trojans, Ransomware, and other threats. For that reason, it is always much better to remove programs like Gestyy.com in order to prevent accidental exposure to more serious security risks.
SUMMARY:
| Name | Gestyy.com |
| Type | Browser Hijacker |
Remove Gestyy.com Virus

The first step towards the removal of Gestyy.com Virus from your Android device is to navigate to Settings, and find the App Manager, which could be named differently on your device (such as Apps, Manage Apps, Application Manager, etc.)
Once you find the App Manager, open the All Apps.
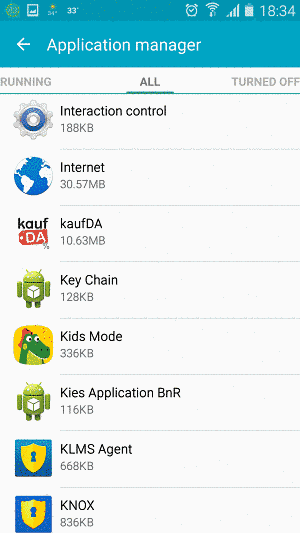
Next, try locating the app you believe that is causing you issues. If there is an app on your device that triggers ad generation and other odd actions, it typically should be located in the All Apps list. However, the app in question may not be labeled exactly Gestyy.com and could have another name. Thus, it could help to filter the list of All Apps by installation date in order to be able to see the new items on the list.
In case you could link the recent issues that you have been experiencing in your Android device to the downloading of a specific application from the list, then this app could be the source of the disturbance.
To deal with it, open it, then select the Force Stop option and then the Uninstall option.

The second step involves cleaning your browser from the Gestyy.com effects. The steps that you need to take are identical, regardless of the browser that you are suing, be it the Default Browser (Internet) or a web browser such as Chrome or another one. Still, for more clarity, we will explain the instructions in both of them.
Default Browser App (“Internet”):
- The first steps is to open the affected browser through the App Manager by finding it on the list.
- Next, tap the Force Stop button. This will quit the app and will allow you to proceed with the instructions below.
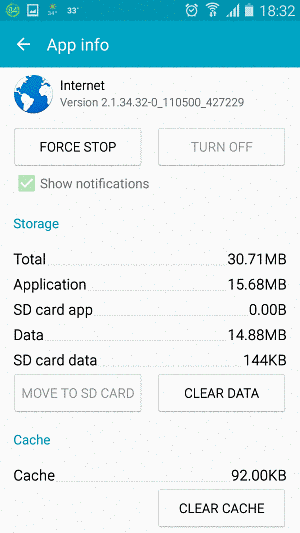
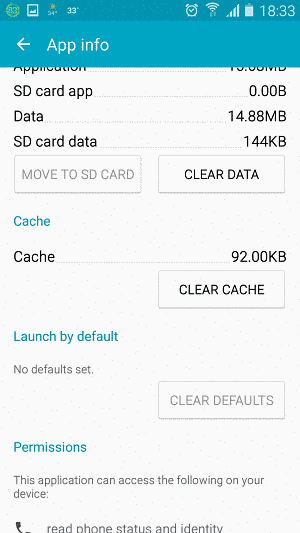
- The next thing you need to do is to click the Clear Data button.
- After that, tap the Clear Chache button. (In case any of the buttons is not active, don’t worry. Just proceed with the steps that follow.)
Google Chrome Browser:
- From the All Apps list find the Google Chrome app, open it and then select the Force Stop button.
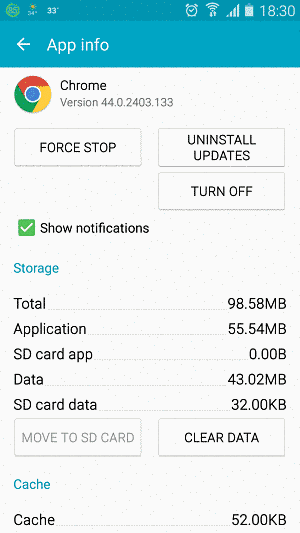
- Next, click on the Clear Data and Clear Cache buttons if they are active. Doing this will delete all the browser data that may be causing an oddly behavior.
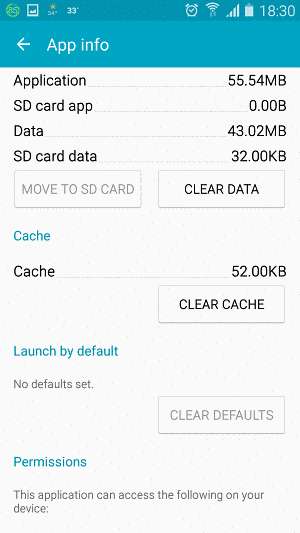

The final step is to Reboot your Android device in order for the deletions and changes to take place. After the Reboot, the problem should be solved.
Attention! When using your browser,it is likely that advertisements come from any of the websites you visit. Thus, if you are still receiving unwanted advertisements on your screen, you can try using an ad blocker. Just make sure you are really careful when selecting an ad blocker if you eventually plan to use one on your smartphone and select an app from a reliable developer.

Thanks for posting this. Hopefully it seems to have rid me of this annoyance. Cheers for your help.
It was an Office Viewer app in my case. Took me ages to find out….
It did it; it’s gone; it was app Talk Back
Thanks for the post. Its clear, simple and totally efficient.
Tried it all, can`t seem to shake this shi7e from my sony phone. I will try try try try again. Thank fuc& I wrote all my passwords down. I may renew my android system on my phone. Mucho thank you anyway.