Redl
Redl is a harmful virus program that won’t let you access your most important files unless you send a ransom payment to the hackers behind it. Redl keeps your files inaccessible through the use of an advanced encryption process.
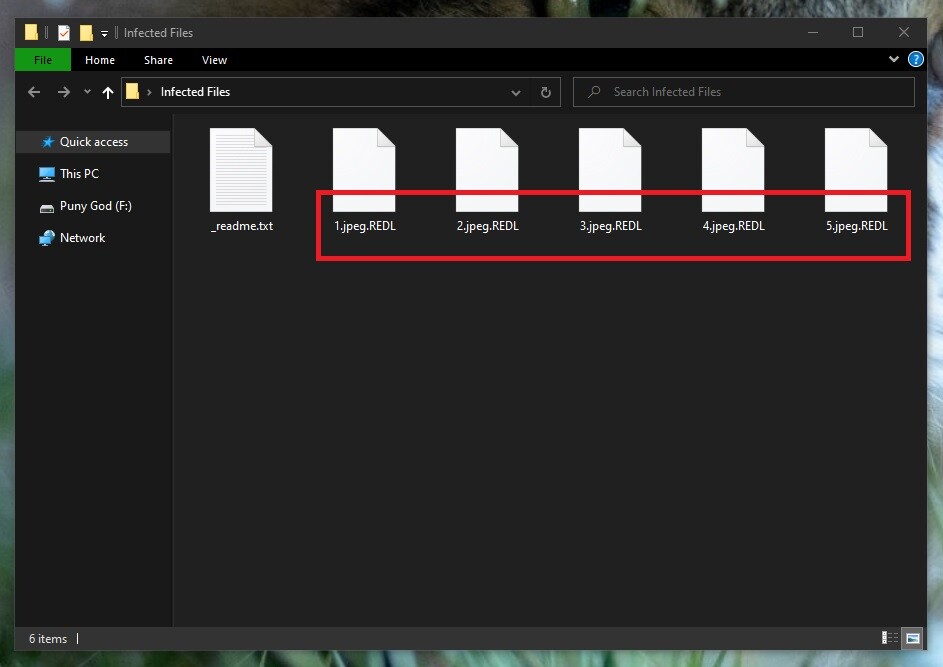
The Redl Virus will encrypt your files
If this virus is present in your computer and it has already managed to lock up your files, you have probably already seen the ransom-demanding note that these threats show their victims. Redl, Nbes and Gesd are Ransomware programs which will force you to pay money for the decryption of your files. Redl won’t harm your data but will also not release it unless you pay. The payment, however, may not be a very good option (we will talk about it more in the next paragraphs) as you’d be putting a lot of money on the line. However, what other options are there to counteract the lockdown on your files. The Redl file encryption is a very sophisticated process and it cannot be reverted through any conventional means. The Redl file encryption cannot be decoded by any antivirus or antimalware program. However, a good security tool can help you get rid of the virus. Redl is a dangerous piece of malware that can lock new files you download or create on your computer. Because of this, Redl must be removed ASAP unless you want to get more of your data locked-up. The good news is that we can help you remove this threat and we can offer you two methods to do it – a manual and an automatic one. However, the best course of action would be to combine the two methods as this would give you the highest chances of fully eliminating this malware virus.
The infamous Ransomware virus category consists of malware programs that more often than not lead to serious data loss once they attack the users’ computers. A Ransomware wouldn’t delete or corrupt the files it targets – instead it would encrypt them. An encrypted file is inaccessible without the right decryption key and, needless to say, this key is in the hands of the people who create such viruses. Their goal is to intimidate you into paying money for this key in order to prevent your data from remaining locked forever. Many users do indeed follow the demands of the hackers, but what they typically don’t consider is that it is possible, if not likely, that the criminal wouldn’t actually provide them with a working decryption key. Of course, once the ransom money is sent to the online crook there’s no getting it back.
The Redl virus
The Redl virus is a harmful Ransomware threat that will encrypt your files using a military-grade encryption algorithm and then tell you to pay a ransom to release them. The Redl virus rarely shows visible symptoms during the encryption making its timely detection nearly impossible.
All of this leaves the Ransomware victims who have had some important data locked up by the virus in a very unpleasant situation. Even if they pay, they may not get to recover their files and, also, many of the Ransomware victims don’t have a choice since the requested sum is too high for them to afford to pay it. There, however, may be another option out there and it all starts with getting rid of the virus that’s responsible for the lock-down on your files. The instructions offered on this page will give you the necessary instructions to help you remove Redl.
The Redl file encryption
The Redl file encryption is a software process that keeps you from accessing your data until you pay a ransom. The Redl file encryption can’t be reversed using regular software. To restore files from the Redl file encryption you need a private key.
Even if the Ransomware gets removed from the computer, the files that it has managed to lock-up won’t get automatically freed. However, with the virus gone, you will have the freedom to use any external backups you may have on other devices or to try out some of the suggested alternative recovery solutions that we have included in the data-restoration section of the guide. Unfortunately, the truth is that we cannot guarantee that even after you follow each of our instructions your files will get released. Still, trying the alternatives is free and won’t require you to spend money on a decryption key you may never really receive.
SUMMARY:
| Name | Redl |
| Type | Ransomware |
| Detection Tool |
Remove Redl Ransomware
You are dealing with a ransomware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to decrypt and recover your encrypted files (if it is currently possible). You can find the removal guide here.

Leave a Comment