This page aims to help you remove “Your computer was infected” Bitcoin Email Malware. Our removal instructions work for every version of Windows.
Many of our users reported that they have received an email with the following message:
Hi, I’m a hacker and programmer, I know one of your password is: *******************
Your computer was infected with my private malware, because your browser wasn’t updated / patched, in such case it’s enough to just visit some website where my iframe is placed to get automatically infected, if you want to find out more – Google: “Drive-by exploit”.
My malware gave me full access to all your accounts (see password above), full control over your computer and it was possible for me to spy on you over your webcam.
I collected all your private data, recorded few videos of you (through your webcam) and I RECORDED YOU SATISFYING YOURSELF!!!
I can publish all your private data everywhere, including the darknet, where the very sick people are and the videos of you, send them to your contacts, post them on social network and everywhere else!
Only you can prevent me from doing this and only I can help you out, there are no traces left, as I removed my malware after my job was done and this email(s) has been sent from some hacked server…
The only way to stop me, is to pay exactly 800$ in bitcoin (BTC).
It’s a very good offer, compared to all that HORRIBLE shit that will happen if you don’t pay!
You can easily buy bitcoin here: www.paxful.com , www.coinbase.com , or check for bitcoin ATM near you, or Google for other exchanger.
You can send the bitcoin directly to my wallet, or create your own wallet first here: www.login.blockchain.com/en/#/signup/ , then receive and send to mine.
My bitcoin wallet is:
Copy and paste it, it’s (cAsE-sEnSEtiVE)
You got 3 days time.
As I got access to this email account, I will know if this email has been read.
If you get this email multiple times, it’s to make sure that you read it, my mailer script is configured like this and after payment you can ignore it.
After receiving the payment, I remove all your data and you can life your live in peace like before.
Next time update your browser before browsing the web!
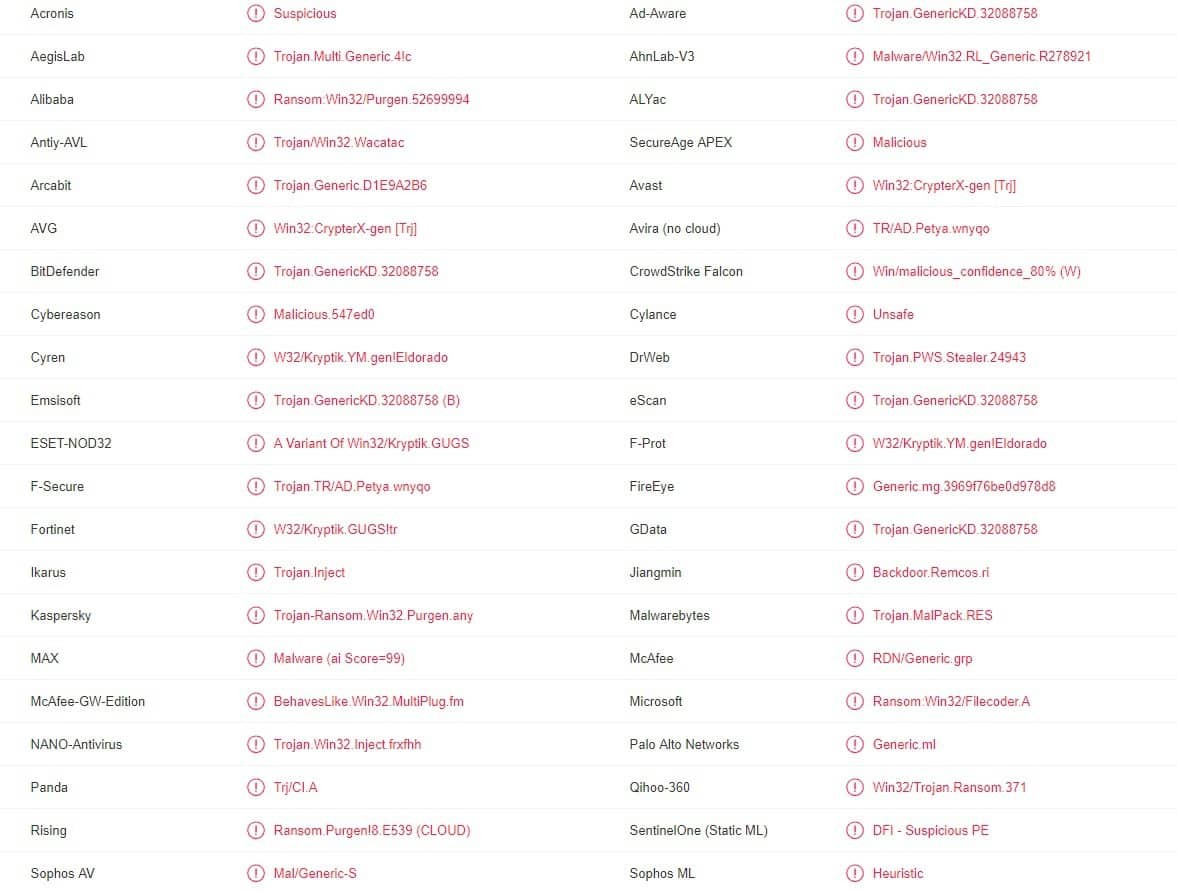
VirusTotal report shows that multiple antivirus programs detect the malware from “Your computer was infected” Email
There is definitely no need to tell you why it is very bad for your computer if it gets infected by a Trojan Horse. Not only PCs but also Mac machines are susceptible to such attacks and it is up to the user to ensure that their machine stays safe against this sort of threatening software. Of course, even if you are the most vigilant and well-prepared computer user, you may still get unpleasantly surprised by some nefarious program of the Trojan Horse category. A recent example of such a malicious software piece is the nasty “Your computer was infected” Email Malware. It is yet another harmful addition to the family of the Trojan Horse infections and this particular one is currently spreading over the Internet like a wildfire. If you are reading this post, then you are probably here because of this threat, more precisely, because it has managed to somehow invade your system. In such a case, there really is no time to waste and you must make sure that you do everything in your power to prevent damage to your system or to your virtual privacy and safety. A guide at the bottom of this article is where we advise you to start – it will provide you with general steps on how you may be able to find the malicious data related to “Your computer was infected” in your system and eliminate it so that the infection goes away. Following the guide is especially important if your antivirus program doesn’t seem to be effective against “Your computer was infected” Email and if the malware doesn’t allow you to install new security software. That being said, you should definitely try to use the help of some for of software-protection software if you can. If you currently do not have any type of security program on your machine or if the one that you do doesn’t seem to help against this Trojan, we advise you to check out the anti-malware tool we’ve included in our guide as it is know to be an effective solution against Trojans like “Your computer was infected”, Porn Blackmail Bitcoin Email Scam or “Hi, I’m a hacker and programmer, I know one of your password”.
What you are faced with if “Your computer was infected” is in your system
As we mentioned, “Your computer was infected” Email Malware is a new threat and this means that it is yet to show its full potential. The Trojans are well-known for their ability to cause various forms of harm and havoc – they are multifunctional cybercrime tools and you oftentimes cannot know what their specific goal/s may be. Some of the things you may face if your machine has gotten infected are theft of banking details, online accounts’ usernames and passwords and even of personal data such as images, videos, text documents, online conversations and more. In other cases, the Trojan may take over the system and allow the hackers to manipulate it and use to their own benefit – cryptocurrency mining, Denial of Service attacks on different sites and networks and so on. In the process, your machine may start to crash, freeze, get errors, have important data deleted and more. The key thing to remember here is that you cannot postpone the process of eliminating the threat – take the necessary removal measures when you can and do not later for later as then it may be too late to do anything.
SUMMARY:
| Name | “Your computer was infected” |
| Type | Trojan |
| Detection Tool |
Remove Your computer was infected Bitcoin Email
You are dealing with a malware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to clean up and reset your browser to its original settings without the malware returning. You can find the removal guide here.
For mobile devices refer to these guides instead: Android, iPhone

Leave a Comment