The Remote Administration Tool Email
The Remote Administration Tool (RAT) email is a scam campaign that uses spam emails to blackmail its victims. The I Hacked your PC group is behind the Remote Administration Tool email scam, and they try to scare you into thinking your computer has been compromised.
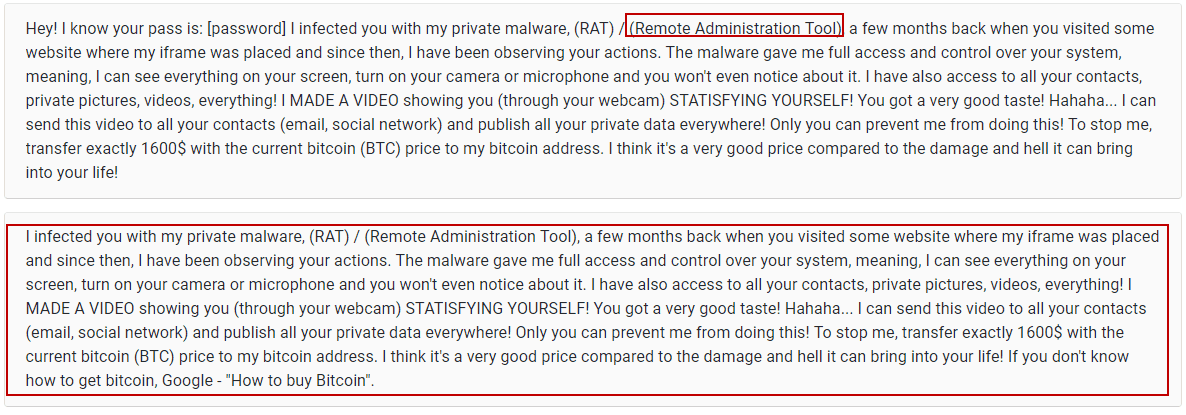
These are examples of the Remote Administration Tool Email
The malicious representatives of the Trojan Horse family of malware are probably the most commonly encountered malware threat on the Internet, they can cause many issues in your system and lead to all sorts of damage. In some cases, a Trojan may even affect you in real life, which is one of the worst things about this category of malicious programs. Our job here is to help our readers deal with different types of software issues, and malware infections. In this particular write-up, our focus will mainly be on a Trojan Horse threat named “Remote Administration Tool” Email. Due to the fact that this virus is very new, there are still some things that aren’t known about it. For instance, we can’t tell you the end goal of the people who are behind this virus. One of the reasons for that stems from the versatility of the abilities of most Trojans. Unlike other threats such as Ransomware, or Spyware, a threats like “Drive by exploit”, Porn Blackmail Bitcoin Email Scam or “Hi, I’m a hacker and programmer, I know one of your password” can be used in a variety of ways, and tasked with the completion of different tasks. Because of this, and because the research on “Remote Administration Tool” Email is still in progress, we can’t really tell you what you can expect if this infection enters your computer. Still, if you know or suspect that your system may have gotten infected by “Remote Administration Tool” Email, you should definitely remove the virus ASAP, or the consequences of its infection could be very severe.
The Remote Administration Tool Malware
The Remove Administration Tool Malware campaign is an email spam campaign where the targeted users receive a message with the following text: “Your computer was infected with my malware, rat (remote administration tool)” and demands for a bitcoin payment.
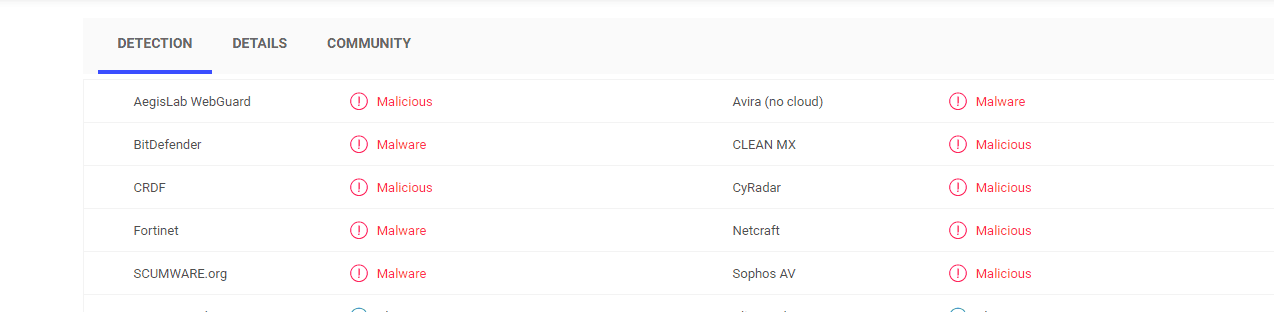
The antivirus scans from VirusTotal help us see the nature of the Remote Administration Tool Malware
The thing that makes Trojans such versatile tools of cyber-crimes is the level of access they gain inside an attacked computer. What most Trojans do is they gain Admin rights in the infected machine – those are the privileges that the Admin of the computer has. If a Trojan gains this level of access in a given machine, it would be able to start, stop, block and modify processes, Registry keys and files in the system. This means that the options in front of the hackers behind “Remote Administration Tool” Email would be vast – they would be able to do pretty much everything that you can do in your computer, and they may even be able to restrict your own access in the machine. In fact, many Trojans are able to prevent the user from installing security programs once the infection has already taken place. Some Trojans also block the security software that’s already present in the machine. This further burdens the process of removing the infection. As far as the actual uses of the Trojan are concerned, they could be many – from theft of sensitive info, to tasking the machine with spam spreading and BitCoin-mining activities, from downloading Ransomware in the computer, to using the machine for DDoS attacks alongside many other infected computers, and so on and so forth.
We may be able to help you deal with this
Hopefully, if you use our guide and the anti-malware tool present in it, you should be able to eliminate the “Remote Administration Tool” Email Trojan and all data related to it. However, be sure to waste no time, and start the removal process as soon as you can, because if you delay the removal, the damage caused by the malware may become irreversible.
SUMMARY:
| Name | “Remote Administration Tool” Email |
| Type | Trojan |
| Detection Tool |
How To Remove Remote Administration Tool Email
You are dealing with a malware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to clean up and reset your browser to its original settings without the malware returning.
You can find the removal guide here.
For mobile devices refer to these guides instead: Android, iPhone.

Leave a Comment