W97M.Downloader
W97M.Downloader is malicious software that can secretly act against the interest of the affected user. Once inside the system, W97M.Downloader can keep track of keystrokes, thereby stealing sensitive user information such as passwords and login credentials.
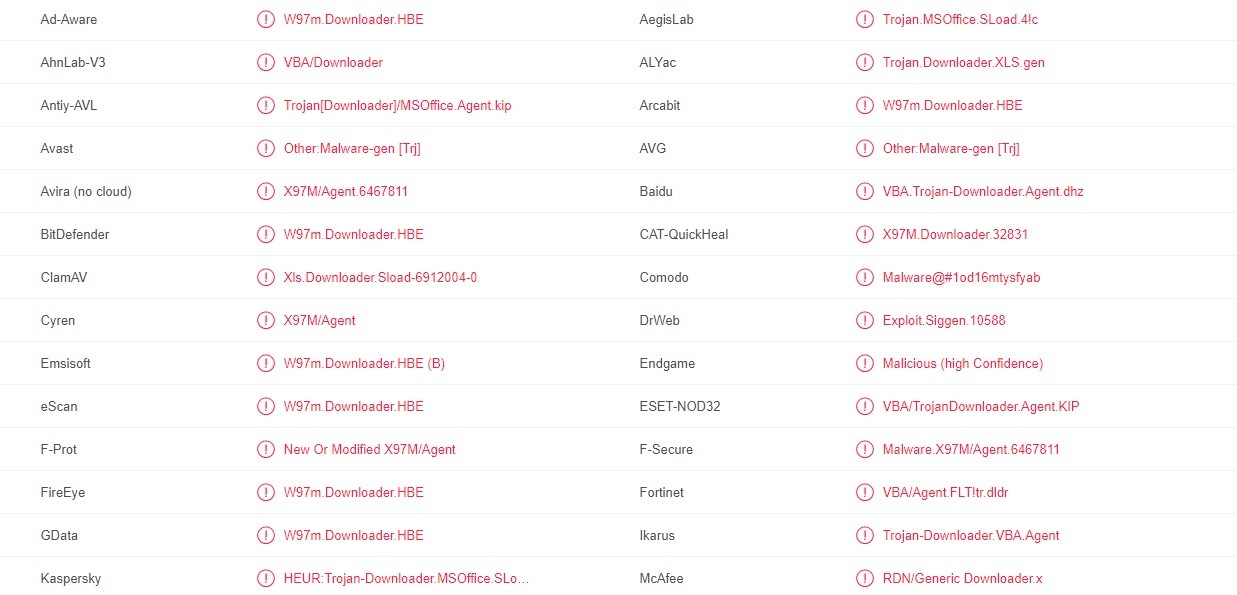
The W97M.Downloader Virus detected by multiple antivirus programs
The article that you are about to read is made with the sole aim to help you detect and remove W97M.Downloader from your PC. This threat is a very malicious Trojan horse, which, if not removed in time, can cause some irreparable damage to your system and your privacy. For this reason, we highly recommend you to eliminate it immediately the very moment you detect it on your computer. There are many reasons for that and our team has dedicated the next lines to reveal to you the type of harm that you may face and give you a better idea of what you are dealing with. What is more, we have assembled a special removal guide, which can show you the exact steps that you need to take in order to get rid of W97M.Downloader and all of its related hidden scripts. For your future system’s safety, we have also prepared some helpful prevention and protection tips, which may come in handy the very moment you remove the Trojan.
What are Trojans?
As their name suggests, Trojans are a type of malware that is usually developed to cause a certain type of harm, but secretly. The way they operate and infect computers is basically inspired by the Trojan horse from Greek mythology. Similar to the soldiers, who were hidden inside the Trojan horse from the myth about the Trojan war, threats like W97M.Downloader, Xxwxx.dll, Wup.exe usually hide inside some harmless looking types of online content. Their aim is to trick users into clicking on them and this way, unknowingly installing the harmful script inside their system. Once inside, these threats operate without any visible symptoms and are usually very hard to detect, unless you are using reliable antivirus software that can catch them. They basically rely on their ability to remain unnoticed in order to perform what they have been programmed for.
What can a threat like this do?
Trojans have gained their popularity as probably one of the nastiest types of malware namely because of their ability to hide in a wide variety of transmitters. This has helped them become a favorite tool for fraud and theft for many cyber criminals. What is more, as we said above, their harmful abilities have literally no limits. For example, they may sit quietly in your machine, setting up security holes in your OS or secretly collecting information, or they may provide the hackers with remote access and let them take control over your PC and everything that is inside it. Another very common criminal practice is the spreading of Ransomware and other nasty viruses via infections like W97M.Downloader. Nasty, isn’t it?
What does a Trojan look like?
That is probably the trickiest thing. A Trojan horse virus like W97M.Downloader can look like just about anything, therefore, it is very difficult to detect it without proper antivirus software. Usually, the malware may appear like an email attachment or a link sent from your friend, some attractive offer, a picture that you may click on, a popular ads site, a banner of a hot sale promotion, that interesting computer game you’ve got from your friend’s USB, a torrent, a link, a file, etc. Tricking users into installing them is what the Trojans rely on, that’s why they may often camouflage as absolutely legitimate types of content in order to mislead you and make you act against your interest and safety.
How do I protect myself against threats like W97M.Downloader?
When we discuss new additions to the Trojan horse family, just like W97M.Downloader, we usually advise our users to be extra careful when interacting with web content. The reason is the latest malware usually uses new and more sophisticated methods of distribution and infection and if you are not cautious, you may land yourself with a really nasty virus. Staying away from sketchy content, non-reputed software installers, shady websites, free downloads, intrusive ads and pop-ups, pirated materials, torrents and dubious links may greatly reduce your chance of meeting Trojans. Still, do not rely only on your estimation, which can easily be tricked, and protect your PC with a trusted antivirus.
How to remove W97M.Downloader?
Detecting and removing W97M.Downloader is the trickiest part of all. Since the malware tries to remain hidden in your system, you have to be very careful when screening for it. You should bear in mind that the harmful scripts may resemble some system files, that’s why you may need a good malware removal tool or some detailed instructions, just like the ones in the removal guide below, in order to recognize the Trojan and delete it.
SUMMARY:
| Name | W97M.Downloader |
| Type | Trojan |
| Danger Level | High (Trojans are often used as a backdoor for Ransomware) |
| Symptoms | Normally, this malware tries to remain unnoticed, therefore it usually has no symptoms that can give it away. |
| Distribution Method | Spam messages, ads, pop-ups, infected webpages, misleading links, malicious installers, torrents, pirate content. |
| Detection Tool |
W97M.Downloader Removal
If you have a Windows virus, continue with the guide below.
If you have a Mac virus, please use our How to remove Ads on Mac guide.
If you have an Android virus, please use our Android Malware Removal guide.
If you have an iPhone virus, please use our iPhone Virus Removal guide
![]()
Some of the steps will likely require you to exit the page. Bookmark it for later reference.
Reboot in Safe Mode (use this guide if you don’t know how to do it).
![]()
WARNING! READ CAREFULLY BEFORE PROCEEDING!
Press CTRL + SHIFT + ESC at the same time and go to the Processes Tab. Try to determine which processes are dangerous.

Right click on each of them and select Open File Location. Then scan the files with our free online virus scanner:

After you open their folder, end the processes that are infected, then delete their folders.
Note: If you are sure something is part of the infection – delete it, even if the scanner doesn’t flag it. No anti-virus program can detect all infections.
![]()
Hold together the Start Key and R. Type appwiz.cpl –> OK.

You are now in the Control Panel. Look for suspicious entries. Uninstall it/them. If you see a screen like this when you click Uninstall, choose NO:

![]()
Type msconfig in the search field and hit enter. A window will pop-up:

Startup —> Uncheck entries that have “Unknown” as Manufacturer or otherwise look suspicious.
- Remember this step – if you have reason to believe a bigger threat (like ransomware) is on your PC, check everything here.
Hold the Start Key and R – copy + paste the following and click OK:
notepad %windir%/system32/Drivers/etc/hosts
A new file will open. If you are hacked, there will be a bunch of other IPs connected to you at the bottom. Look at the image below:

If there are suspicious IPs below “Localhost” – write to us in the comments.
![]()
Type Regedit in the windows search field and press Enter.
Once inside, press CTRL and F together and type the virus’s Name. Right click and delete any entries you find with a similar name. If they don’t show up this way, go manually to these directories and delete/uninstall them:
- HKEY_CURRENT_USER—-Software—–Random Directory. It could be any one of them – ask us if you can’t discern which ones are malicious.
HKEY_CURRENT_USER—-Software—Microsoft—-Windows—CurrentVersion—Run– Random
HKEY_CURRENT_USER—-Software—Microsoft—Internet Explorer—-Main—- Random
If the guide doesn’t help, download the anti-virus program we recommended or try our free online virus scanner. Also, you can always ask us in the comments for help!

Leave a Comment