*Source of claim SH can remove it.
Botnet Blacklist
Botnet Blacklist is a computer threat that can start malicious processes on the infected computer without the users’ knowledge or permission. Due to its stealth and versatility, Botnet Blacklist can be described as a malware program from the Trojan horse type.
If you are about to deal with Botnet Blacklist or you suspect that this malicious program has compromised your computer and you need assistance to detect it, on this page you will find the needed information. It is important to learn about the possible effects that this Trojan horse may have, as well as the methods you can use to remove it. Your timely actions will help you to prevent some very unpleasant consequences and, hopefully, save your machine.
One of the first things that you need to know about viruses like Botnet Blacklist, Wup.exe, Presenoker is that they use a variety of tactics to infect users’ computers. Very often such threats may come in the form of harmless-looking notifications, pop-up ads, email messages, file attachments or web links that prompt the victims to click on them, open a link or a file, or download something on their computer. In other words, users need to somehow interact with the harmful Trojan transmitters for the malware to successfully sneak inside their machines and get them infected.
A common method of spreading Trojans like Botnet Blacklist is to disguise the virus as a free or pirated software piece that users can access and download easily. Of course, many people would take the bait, download the disguised virus on their computer and then launch its file believing that what they are getting is actually a helpful program or some free and useful tool. The moment the Trojan is downloaded and allowed to access some system settings, it is free to carry out its malicious agenda.
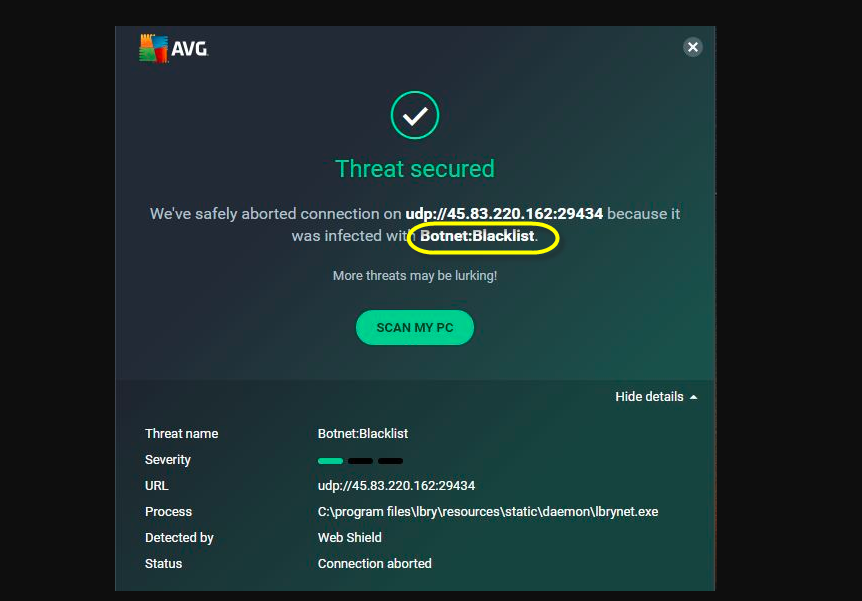
Botnet Blacklist on Avast
Another thing you should be cautious about is the potential symptoms that a virus such as Botnet Blacklist on Avast may cause. A Trojan horse like Botnet Blacklist on Avast can often remain almost invisible in the system for indefinite periods of time since it will show virtually no signs of its presence.
In some rare cases, however, there might be some red flags that should not be overlooked. Such could be the constant crashes of the system for no particular reason, unusual program errors, changes in the system’s settings, overall computer slowness or unresponsiveness. If there’s anything unusual about the way your computer works, you should do a full system check with reliable security software and remove anything that is flagged as harmful.
What type of damage may Botnet Blacklist do?
A Trojan horse virus like Botnet Blacklist can cause harm in many different ways. At the very beginning of this article we mentioned that the members of this class of malware can be very flexible. They can spy on the victims through the infected computer, collect confidential personal information, track computer processes, delete or modify system data, and force the system to conduct unlawful operations and tasks. Trojans can even insert other malware programs into the already infected machine. For example, Ransomware is a form of computer threat that is often injected into victims’ computers by such threats.
Whatever Botnet Blacklist is trying to do on your computer, however, you should not allow it to finish its task. Instead, use the instructions in the guide below and the professional removal tool to quickly detect and remove this malicious program before it has achieved its objective.
SUMMARY:
| Name | Botnet Blacklist |
| Type | Trojan |
| Detection Tool |
*Source of claim SH can remove it.
Remove Botnet Blacklist Avast Virus
You are dealing with a malware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to clean up and reset your browser to its original settings without the malware returning.
You can find the removal guide here.
For mobile devices refer to these guides instead: Android , iPhone

Leave a Comment