Piny
Piny is a file-encrypting infection that can restrict access to user files and demand a ransom payment for their liberation. Created by anonymous cybercriminals, Piny is malicious software used to extort money from web users, big and small businesses, and different organizations.
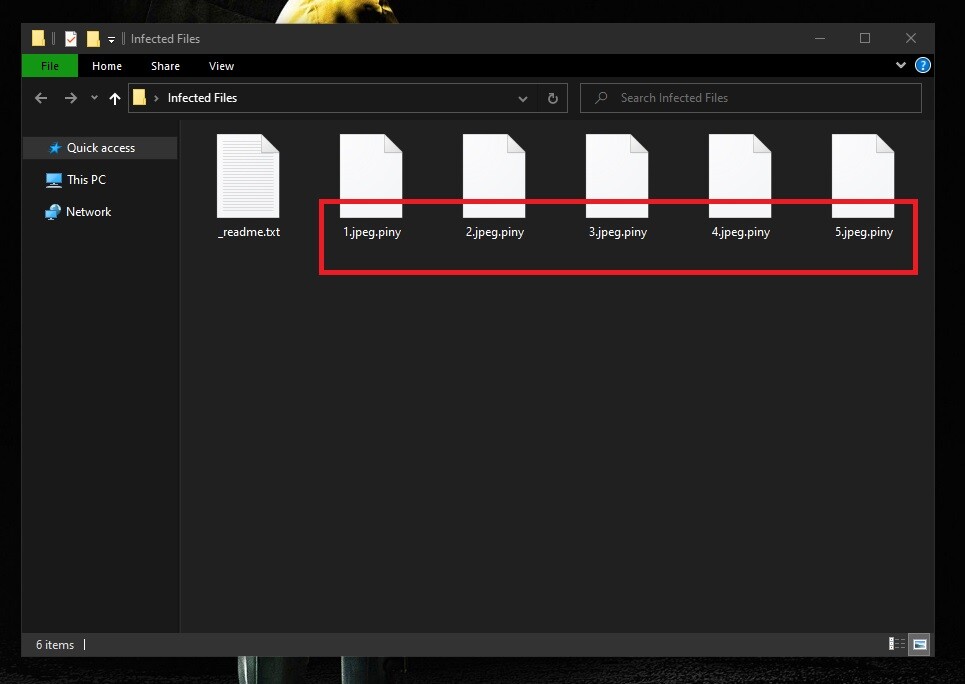
The Piny Virus will encrypt your files
Ransomware viruses have become the most terrible threat that one can face online and, sadly, nobody can stop them at the moment. Every day new variants are developed causing millions of infections with the sole aim to extort money from unsuspecting web users. Piny is one of the newest versions of Ransomware and it terrorizes users by encrypting their most valuable files. We have recently received a number of complaints from people infected by this terrible threat and most of them want us to help them remove the malware and provide them with a possible solution for the encrypted files. That’s why we would like to, first and foremost, explain the concept of ransomware so that you can get a clear understanding of how it operates. And then we will provide those who need a workaround for the Piny virus with a comprehensive removal guide and some file recovery suggestions.
The Piny virus
The Piny virus is a money extortion virus designed to encrypt valuable user information and keep it hostage for a ransom. The Piny virus typically demands a money transfer from its victims by displaying a ransom message on their screen.
The main reason why threats such as Piny, Nbes, Redl are considered so dangerous is that it is very difficult to crack their file encryption code. Basically, this is possible only with the help of a special decryption key which is kept in secret by the hackers who stay behind the infection. To obtain that key, the victims are asked to pay a ransom and are typically threatened that if they don’t transfer the required money within a given deadline, the decryption key will be destroyed and the encrypted files will remain inaccessible forever. The crooks that control the Ransomware usually place a threatening ransom-demanding message on the screen of the infected computer and provide concrete ransom payment instructions.
The Piny file encryption
The Piny file encryption is a process that converts user files into unreadable bits of data through the application of a secret file-encryption code. The Piny file encryption process typically happens in stealth and has no visible symptoms which can give it away.
The file encryption by itself is not a harmful activity but a commonly used method for data protection. And because no damage is caused to the files or the system and there is nothing that gets corrupted, stolen, or destroyed, most security programs do not to report the file-encrypting process that’s taking place in the background.
Luckily, certain alternative ways to possibly recover your information exist. That’s why we do not recommend that victims of Piny pay the ransom to the hackers before they give a try to some of those alternatives. The file-recovery attempts, however, should not begin unless the ransomware is fully removed from the system. This is critical because, if not removed, the virus can encrypt any recovered files including their backup copies that come in contact with the infected computer. For this reason, the first thing we advise you to do is to delete Piny in a safe and reliable manner and only then give a try to our file-recovery suggestions from the removal guide below.
SUMMARY:
| Name | Piny |
| Type | Ransomware |
| Detection Tool |
Remove Piny Ransomware
Search Marquis is a high-profile hijacker – you might want to see if you’re not infected with it as well.
You can find the removal guide here.

How to find recently deleted files?
Sry… Asking for recently added file. Help please
Hi Raghul Prashath,
just carefully follow the steps in our guide.
In Step 4, these files ‘%ProgramData% & %WinDir%” couldn’t be deleted.
Hi Haroon,
these are directories you have to check for unfamiliar files. Delete files that were recently added.