We recently came across some user complaints about sudden pop-ups to a site called Antivirus Armor Hub (antivirusarmorhub.xyz) that occur in Google Chrome and other Chromium-based browsers. The users experiencing this report that the site claims to...
Latest Removal Guides
How to Remove the Imgcreator Virus
Imgcreator.zmo.ai is a website for generating AI images that seems perfectly legitimate at first sight, but many users have recently been getting automatic redirects to it for no apparent reason. This has led to a lot of confusion surrounding the...
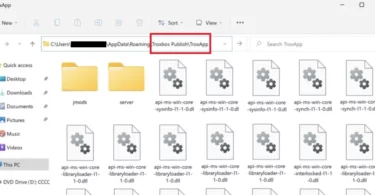
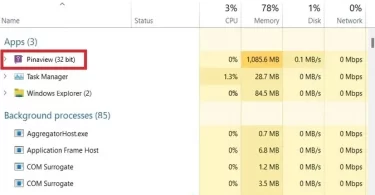
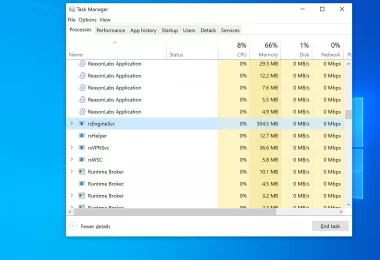
How to remove TroxApp from your computer
TroxApp is one of many iterations of a particularly stubborn browser hijacker app that gets in the system and takes over the browser after being installed through a file bundle or a dedicated setup.msi installer. We encountered many reports from...
How to Remove Skyjem
Skyjem is one of the most commonly encountered browser hijackers for Windows PCs in recent weeks, so we are actively monitoring it to provide you with the most relevant, up-to-date, and helpful information and removal instructions. Like most other...
How to Remove Encryption Defender CC From iPhone
We created this page to help users remove encryptiondefender.cc – a pop-up virus targeting primarily mobile users (especially iPhone), with a smaller mix of desktop infections as well. Most users refer to it as Encryption Defender, so...
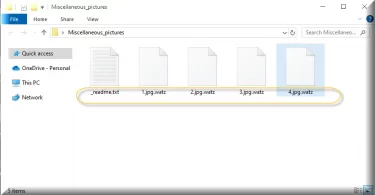
How to Remove and Decrypt the .Watz Virus Files
The Watz ransomware is one of the most commonly encountered interactions of the STOP/Djvu ransomware family, similar to .Waqa and .Qual. If this malware has attacked you and your files now have the .watz extension, then this guide is for you...
Latest Updated
Security News
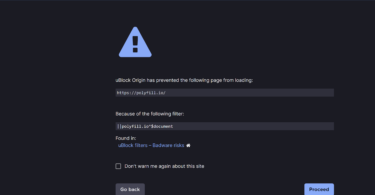
Polyfill.io infects 100k websites with malware
If you’ve been following the latest cybersecurity news, you might have heard about the recent supply chain attack involving Polyfill.io. I somehow missed this until today, due to, well, researching other malware. But the attack proved...
Cyber Security Monthly Recap: April 2024
April is over, but if you want to know what important has happened during the month, check out our selection of major topics from the cyberseucrity world. The past weeks were marked with the release of a number of security updates and reports...
Cyber Security Monthly Recap: March 2024
Hi there, lovers of security! Did you miss our Cyber Security Monthly Recap? We’re back with the third installment of our monthly series, which consists of brief but informative tidbits to keep you informed about the Security and Safety sector...
Cyber Security Monthly Recap: January 2024
Welcome to the January 2024 edition of Cyber Security Monthly Recap. This month, we’ve seen some significant events that emphasize the importance of protecting our digital world. From legal challenges to critical vulnerabilities, January 2024...
Cyber Security Monthly Recap: December 2023
December 2023 in the cybersecurity world was marked by a series of significant developments, reflecting the ever-evolving nature of cyber threats and the continuous efforts to counteract them. This month witnessed a range of events, from...
Cyber Security Monthly Recap: November 2023
November 2023 was a busy month for cybersecurity, with many incidents and insights reported by various sources. Here are some of the highlights of what happened in the cyber world in the past month. Widespread Ransomware Attacks November 2023...
Reviews
Tutorials
News Bulletin
HowToRemove.Guide is proud to present its merger with TinySoftware.com. TinySoftware.com is a security website dedicated to firewall protection, security solutions and vulnerability detection. In the past we have worked with the team at TinySoftware.com to effectively help users who have reached out to us with malware infections concerning website servers and entire company networks.
HowToRemove.Guide is a website dedicated to helping thousands of malware-infected users every day through self-help removal guides. Recently we expanded into general security, software reviews and backups, while the folks at TinySoftware.com became increasingly interested in the consumer malware removal niche.
This has allowed both parties to quickly realize that a partnership can benefit everyone – and the users most of all. The experience and expertise TinySoftware.com brings to the table will allow us to rapidly improve the technical help we bring to our users, which will in turn lead to better service we hope we hope will turn into a community. The services and pages on TinySoftware.com will remain on this website and will be accessible to all users who need them.